Lightweight anonymous authentication method suitable for resource-limited equipment
An anonymous authentication and resource-constrained technology, applied in the field of information security, can solve problems such as limitations, achieve the effect of reducing requirements and reducing computing overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0035] The solutions of the present invention will be further described below in conjunction with the accompanying drawings and embodiments.
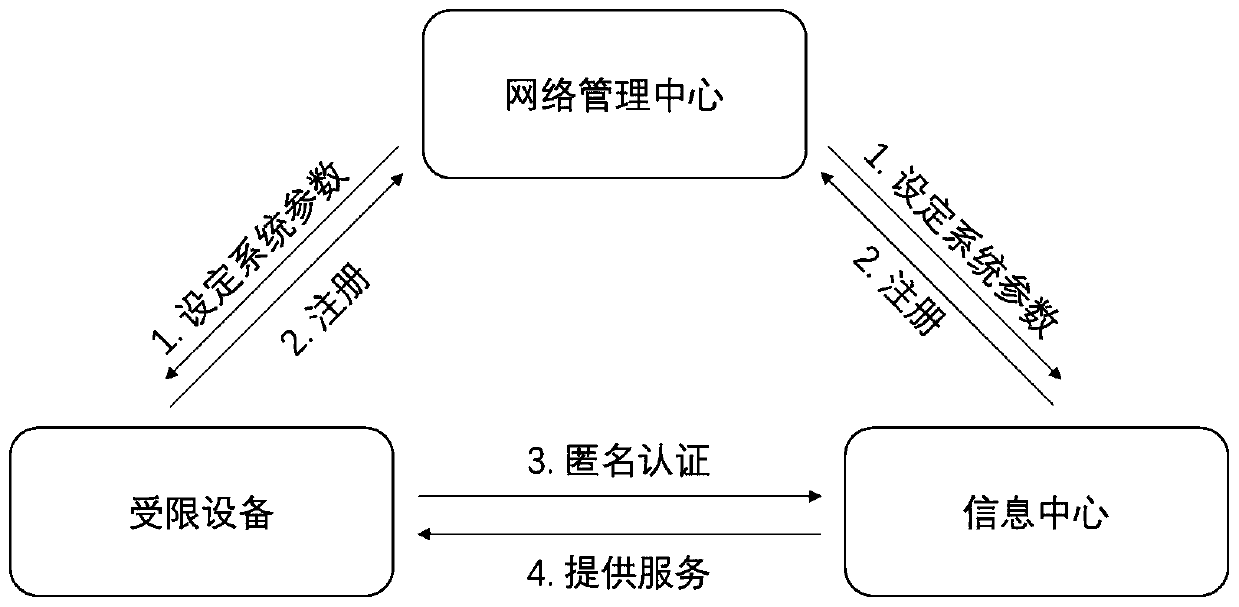
[0036] A lightweight anonymous authentication method suitable for resource-constrained devices proposed by the present invention is implemented by using an information system model, and the information system model includes the following three entities, such as figure 1 Shown:
[0037] Network Management Center (Network Management Center): acts as a key generation center and is responsible for the registration of restricted devices and information centers in the information network. It is similar to a trusted third party and manages the entire information network and is responsible for the initialization of public parameters.
[0038] Restricted Equipment: Communication terminals with limited computing resources should register with the network management center and pre-load public parameters before accessing the information center and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More