Safety protection method for ubiquitous power Internet of Things terminal in specific attack scene
A power Internet of Things and attack scenario technology, applied in the field of power information security, can solve problems such as inability to attack monitoring, achieve the actual value of large projects, and ensure the effect of network security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The technical solution of the present invention will be further described in detail below in conjunction with the accompanying drawings of the specification.
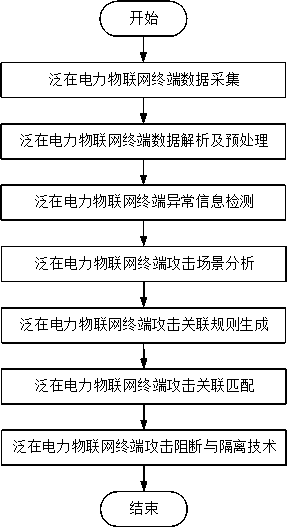
[0024] The development of the ubiquitous power Internet of Things emphasizes the integration of energy flow and information flow, and achieving information sharing and interconnection, network security is particularly important. The present invention proposes a security protection method for ubiquitous power Internet of Things terminal in a specific attack scenario, which protects the data of the power terminal according to the development needs of ubiquitous power Internet of Things, and helps to further improve the panoramic perception ability of the power grid. . The security protection methods for ubiquitous power IoT terminals in specific attack scenarios proposed in this article mainly include the following steps, such as figure 1 Shown.
[0025] Step 1, Ubiquitous power IoT terminal data collection. The perce...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More