Access request response method and device and electronic equipment
A technology for access requests and electronic equipment, applied in electrical components, transmission systems, etc., can solve the problem of unpredictable prevention of illegal intrusion, and achieve the effect of reducing the possibility of remote illegal intrusion, preventing theft of authority, and improving security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
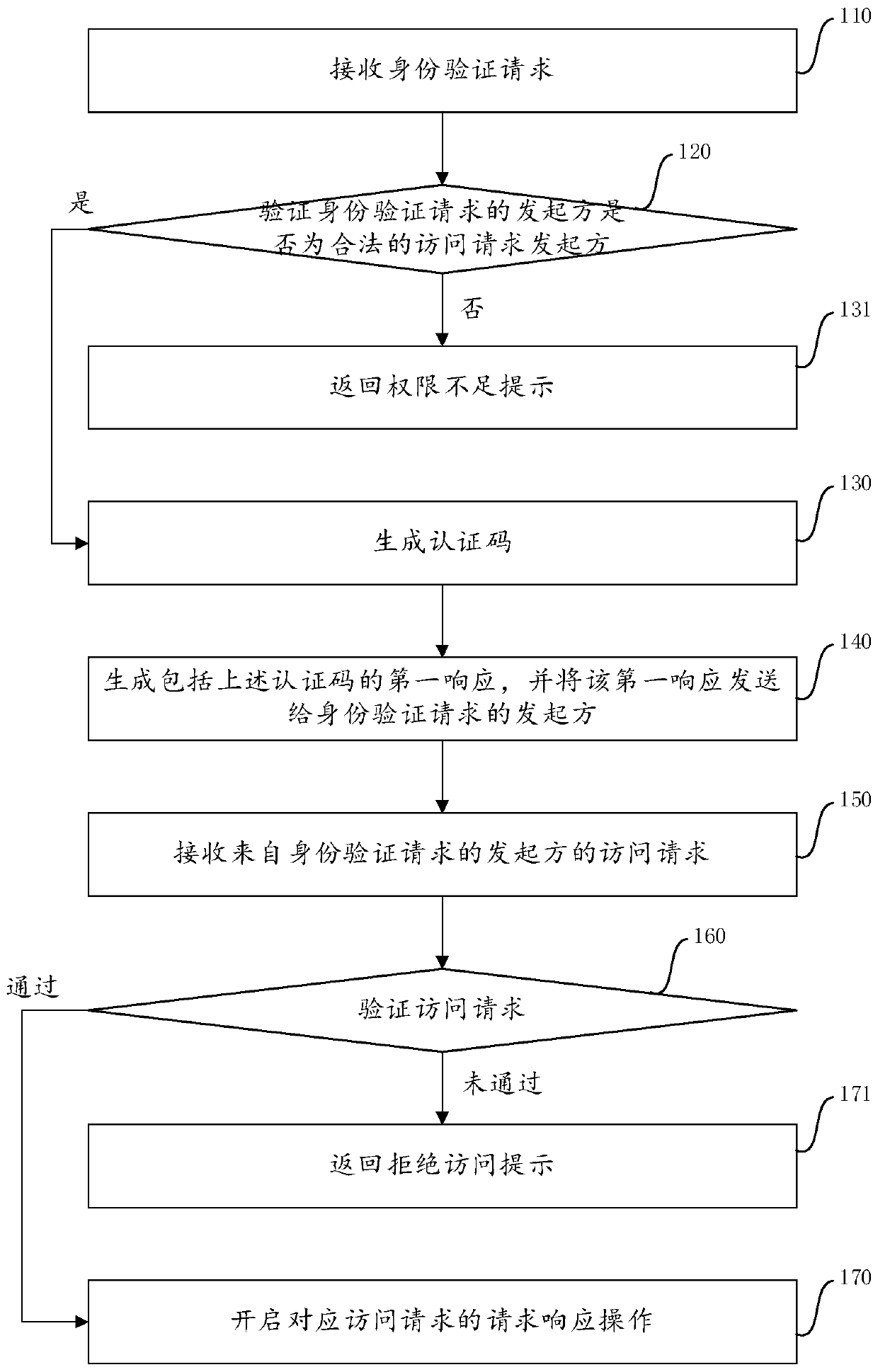
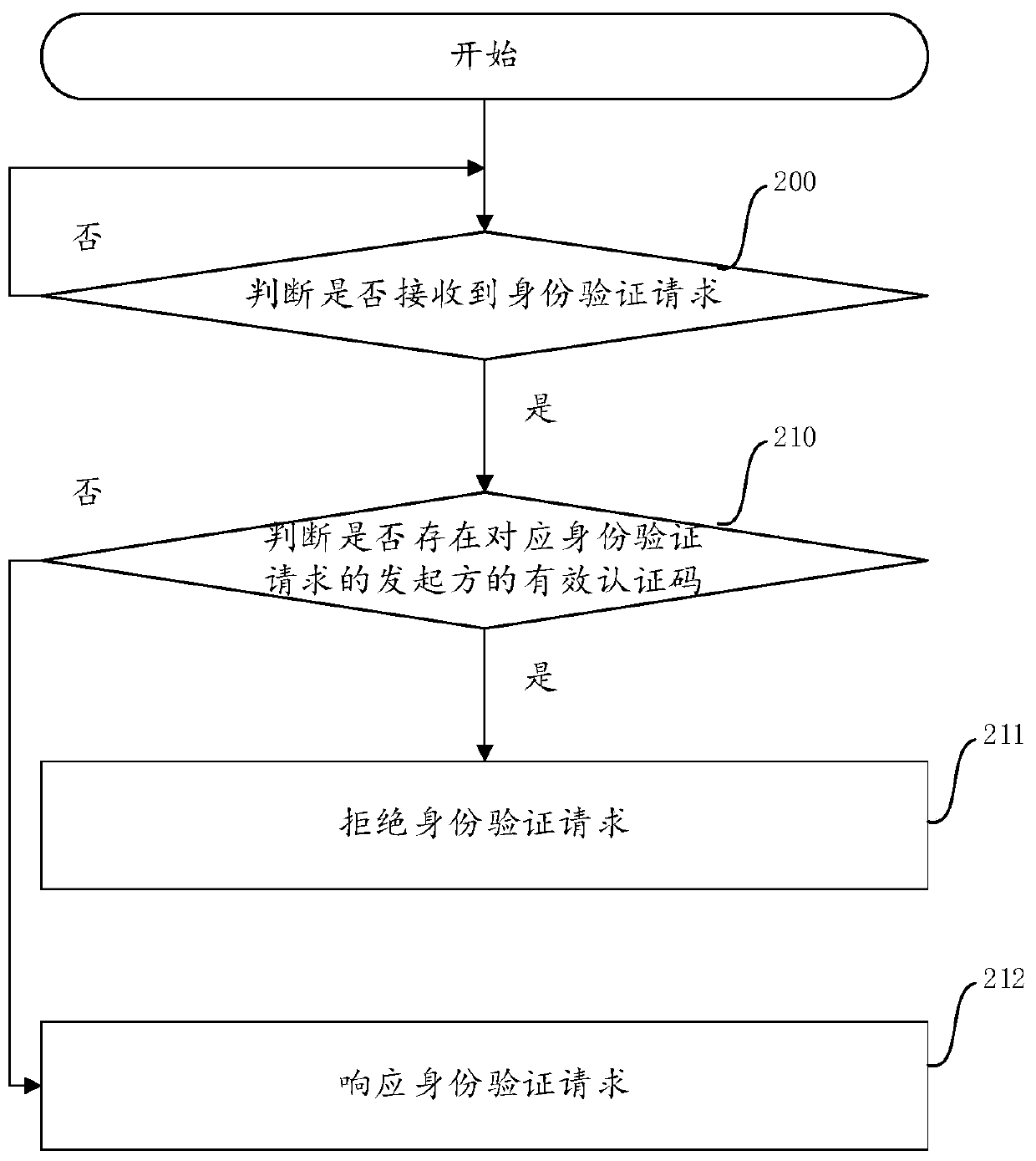
[0070] In order to improve the security of remote control, the embodiment of the present application proposes a response method for access requests to provide a permission verification method between the initiator of the access request and the device to be responded, which is easy to operate and effectively improves the efficiency of remote data interaction. safety. Specifically, in order to propose the method of the embodiment of the present application, the inventor first analyzes the implementation details of the remote data interaction application scenario.
[0071] Generally, when an access request is initiated to a remote target device with automatic response capability, before the target device responds to the access request, it needs to authenticate the originator of the access request to confirm whether it has the authority to initiate the access request. When the target device confirms that the initiator has the authority to initiate the access request, it will respo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More