Block chain-based proxy re-encryption method and system, and storage medium
A proxy re-encryption and re-encryption technology, applied in the field of applied cryptography, can solve the problems of security risks, opacity, and non-public traceability, and achieve the effect of preventing security risks and eliminating dependencies.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below can be combined with each other as long as they do not constitute a conflict with each other.
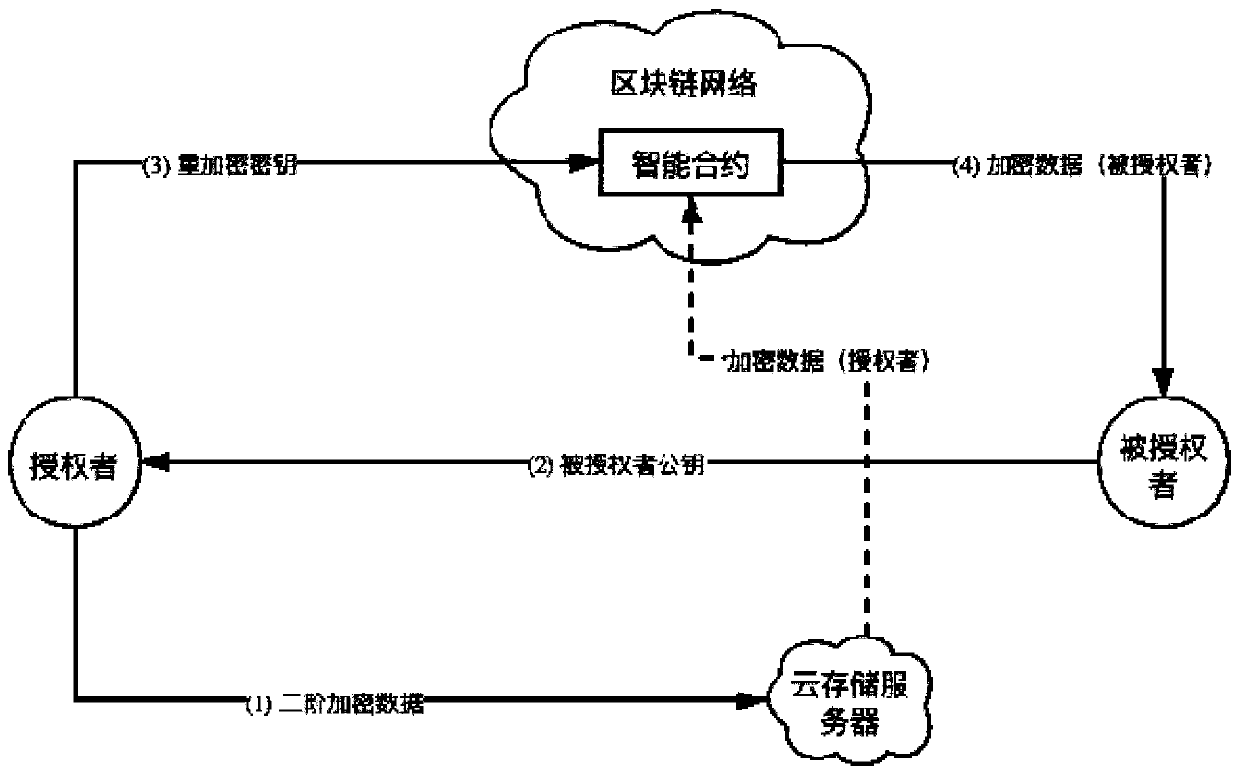
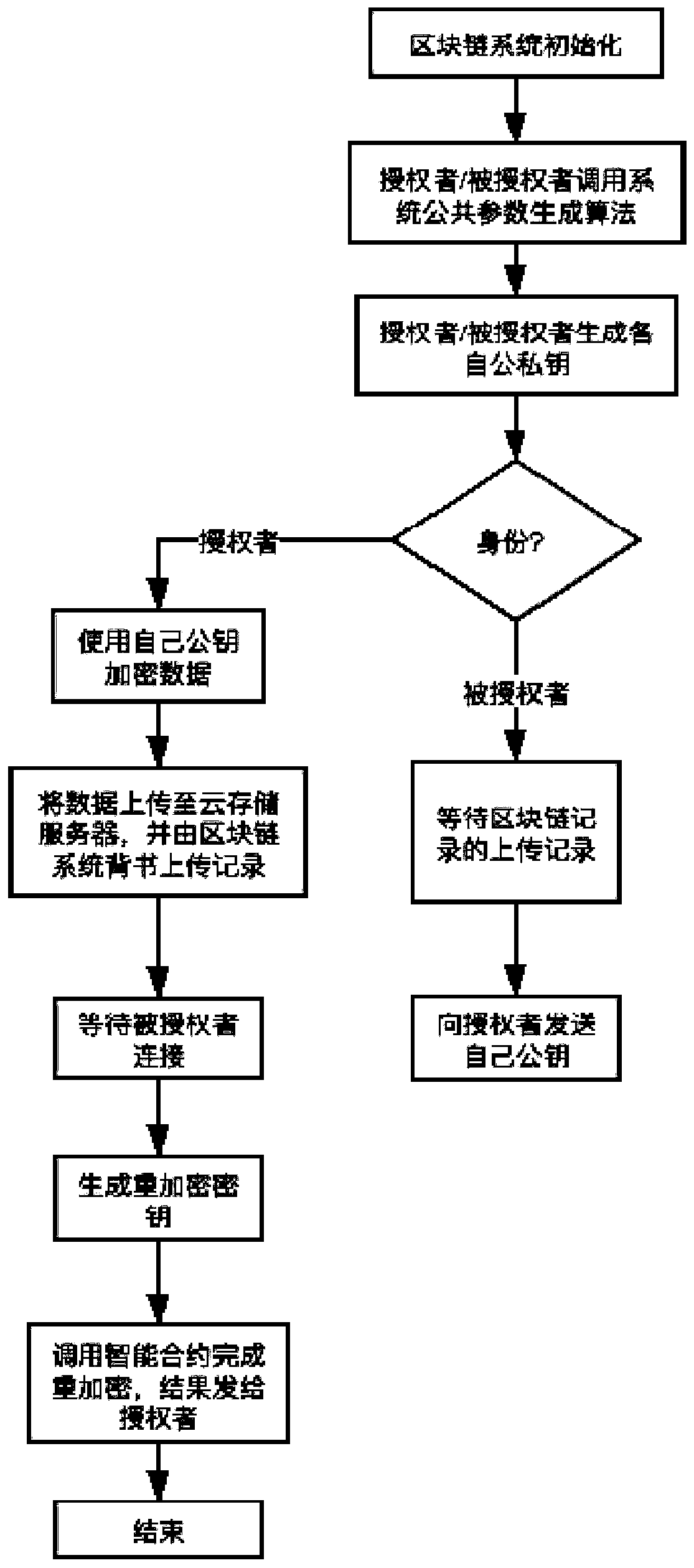
[0038] A block chain-based proxy re-encryption method provided by the embodiment of the present invention, the realization principle is as follows figure 1 shown. In the process of proxy re-encryption, the following four types of roles are included: authorizer, cloud storage server, blockchain system and authorized party. The specific process is as figure 2 shown.
[0039] (1) System initia...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap