Anonymous data sharing method and system based on data source and data master hiding
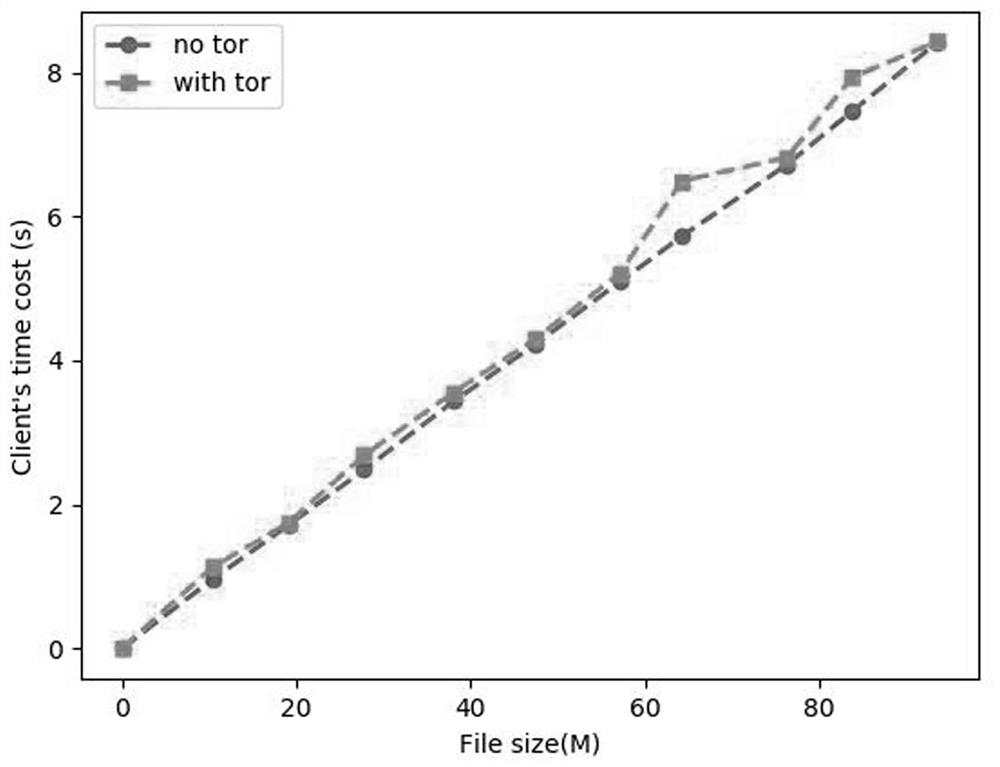
A data sharing and data master technology, applied in the field of network security, can solve the problems of increasing client overhead, leaking IP addresses, affecting user experience, etc., to reduce client overhead, realize access control, and ensure the effect of forward security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
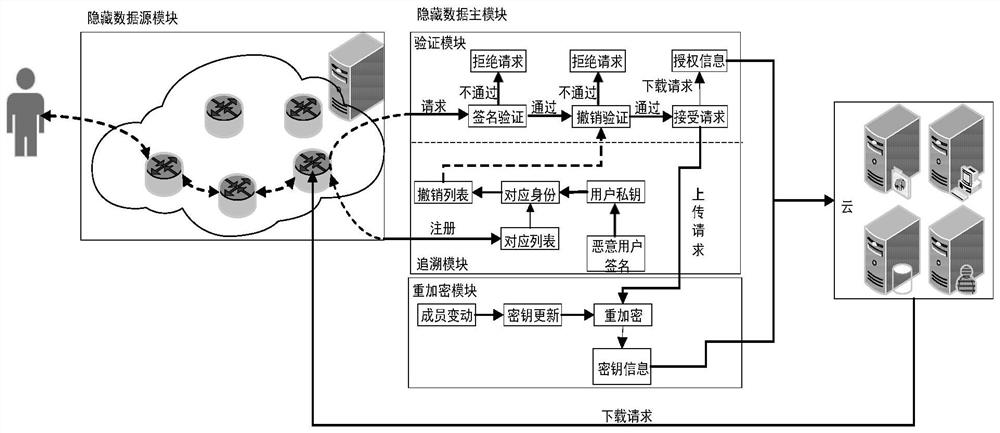
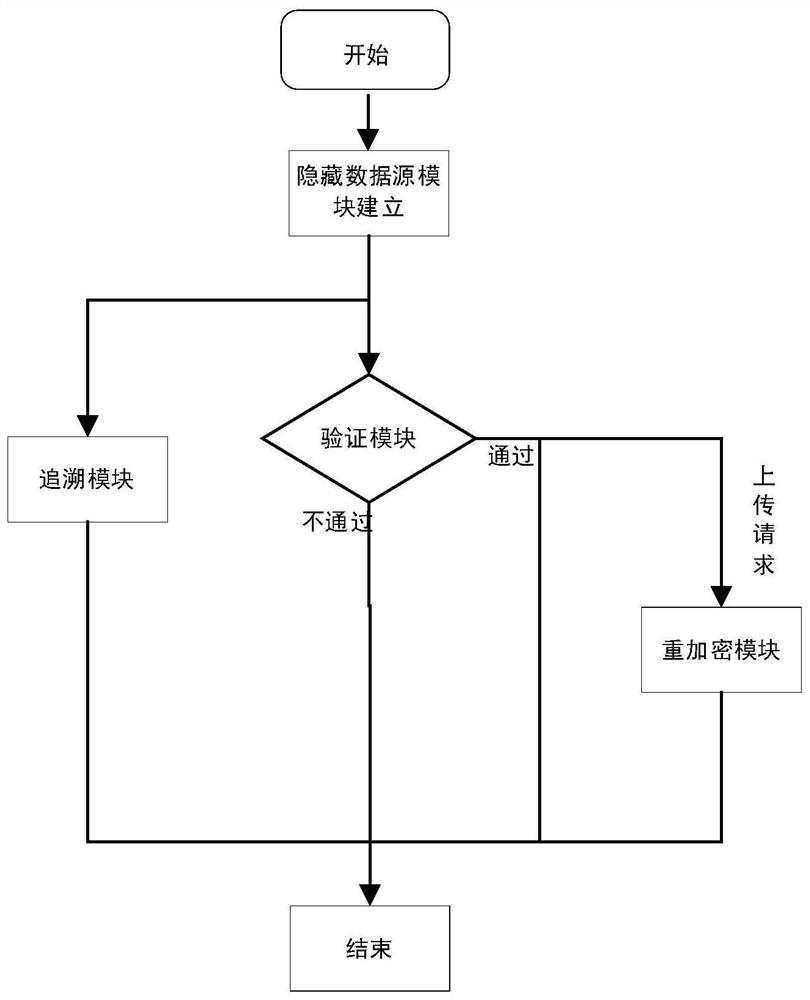
[0083] In this embodiment, a group of patients need to submit their detailed medical conditions to the hospital. These patients hope that their data can be uploaded safely and accurately, but they do not want to expose their information to other data sharers. In the process of uploading data, authentication is required. If you want to pass the authentication without revealing your identity information, you need to perform anonymous authentication.
[0084] In this regard, the existing anonymous authentication has the following situation: a malicious user uploads some false information in order to obtain benefits. At this time, the authentication scheme needs to be able to trace the user, and the trace user means that the real identity of the user can be traced. However, existing technologies such as ring signatures do not have the ability to trace users. Therefore, while using group signatures to implement anonymous authentication to ensure user identity privacy, they still hav...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More