A re-random identification encryption and decryption method
An encryption, decryption and identification technology, applied in the field of re-random identification encryption and decryption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0077] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
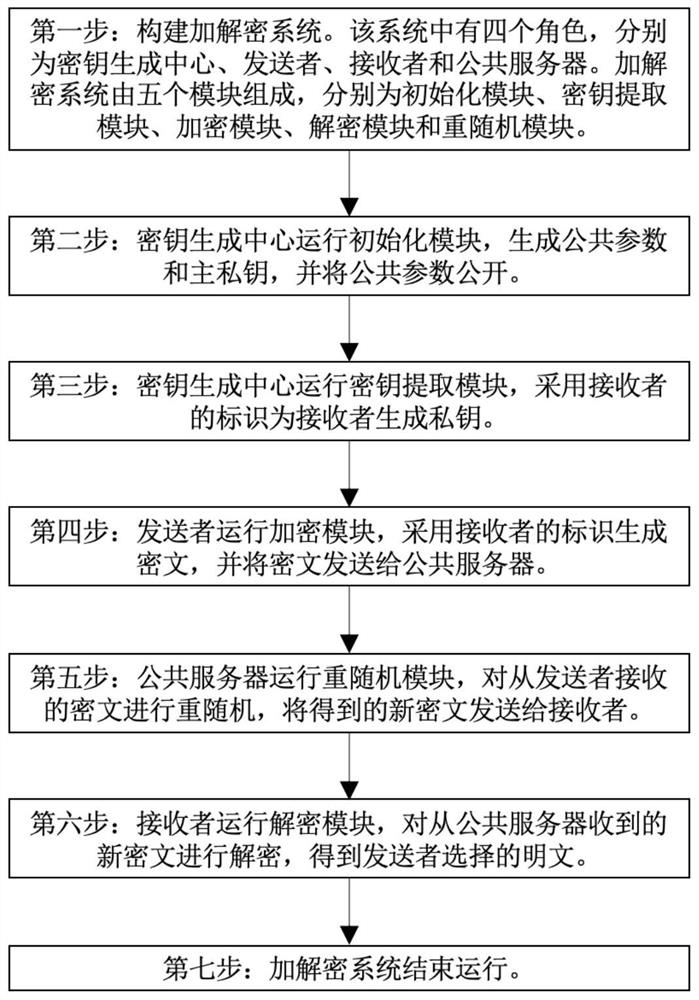
[0078] Such as figure 2 Shown, the present invention comprises the following steps:
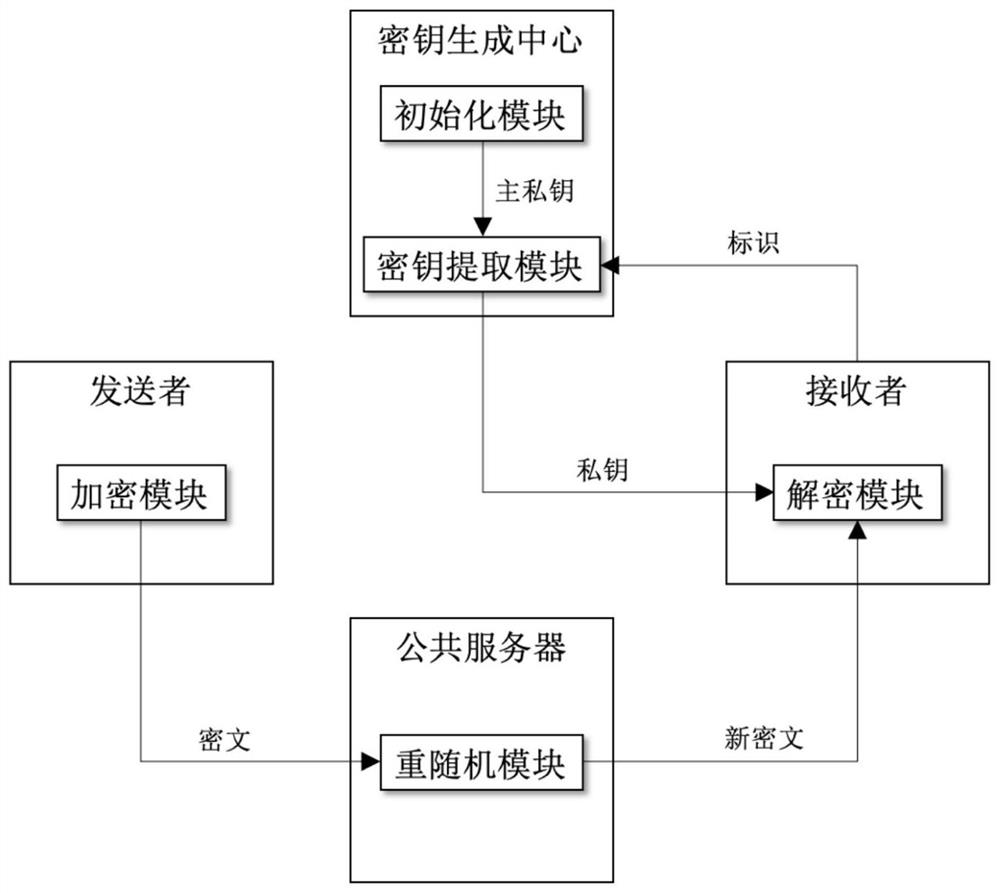
[0079] Step 1: Build an encryption and decryption system. Such as figure 1 As shown, there are four roles in the encryption and decryption system, namely key generation center, sender, receiver and public server. The encryption and decryption system consists of five modules, which are initialization module, key extraction module, encryption module, decryption module and rerandom module. The initialization module and key extraction module are deployed in the key generation center, the encryption module is deployed in the sender, the decryption module is deployed in the receiver, and the re-random module is deployed in the public server.
[0080] Step 2: The key generation center runs the initialization module, generates public parameters and master private...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More