Method and device for monitoring access based on short link
A technology of short link and forbidden access, applied in the computer field, can solve the problem of no short link follow-up monitoring, etc., and achieve the effect of safeguarding the interests of users
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
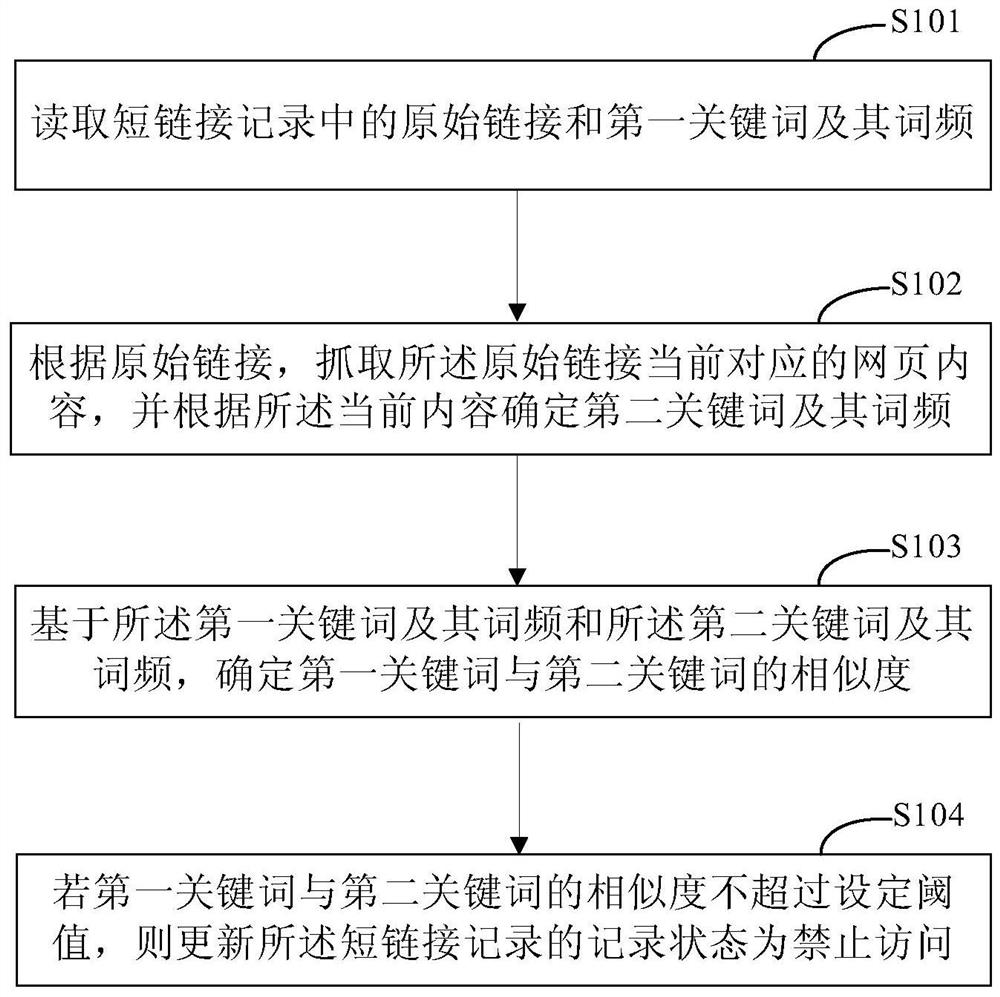
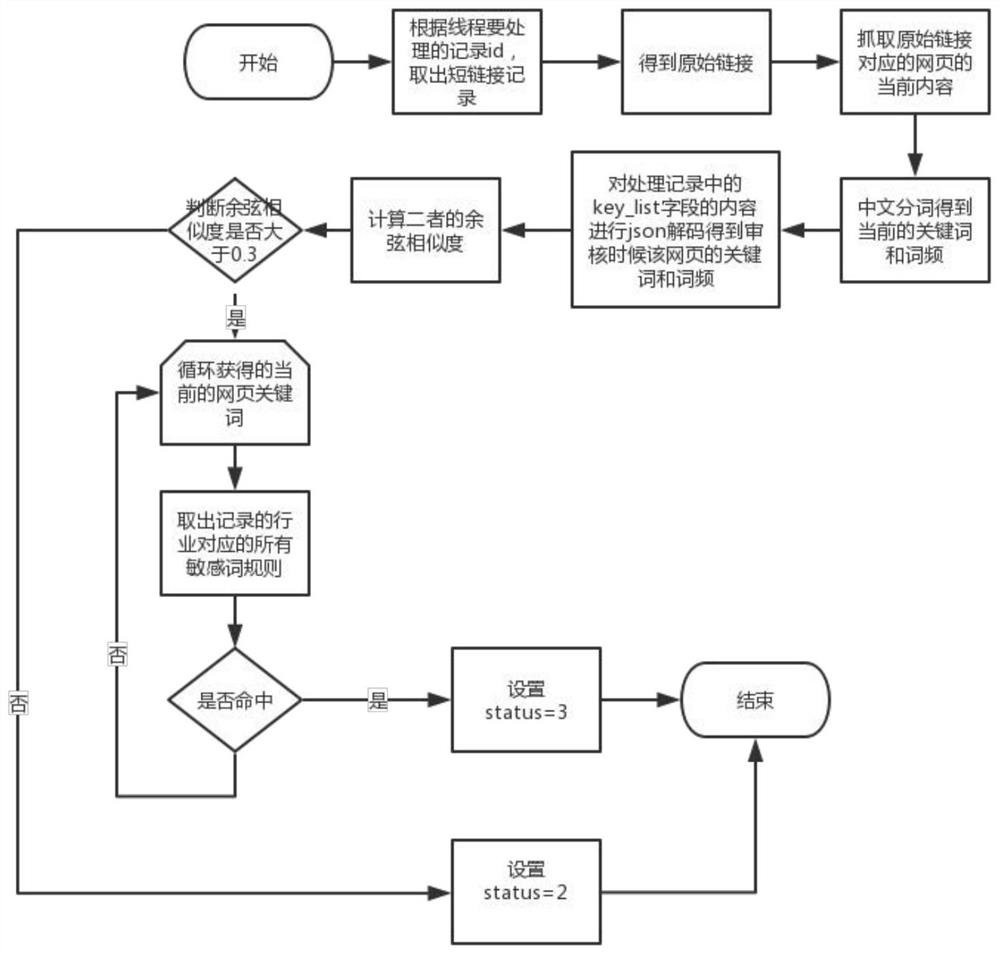
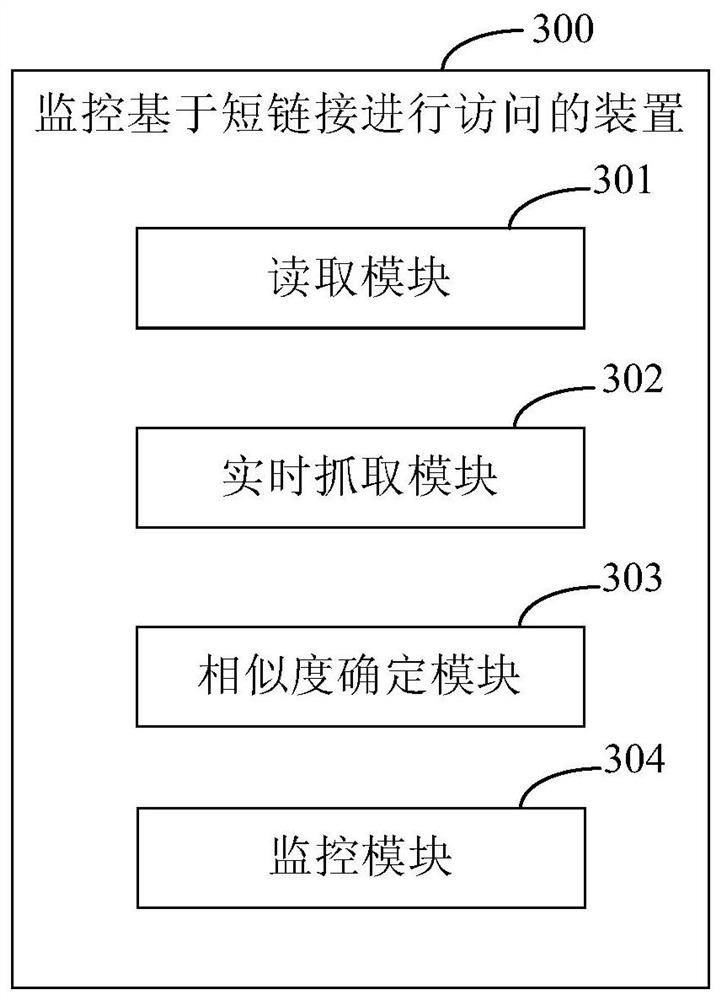
Method used
Image
Examples
Embodiment Construction
[0028] Exemplary embodiments of the present invention are described below in conjunction with the accompanying drawings, which include various details of the embodiments of the present invention to facilitate understanding, and they should be regarded as exemplary only. Accordingly, those of ordinary skill in the art will recognize that various changes and modifications of the embodiments described herein can be made without departing from the scope and spirit of the invention. Also, descriptions of well-known functions and constructions are omitted in the following description for clarity and conciseness.
[0029] The following application scenarios can be taken as examples to describe the embodiments of the present invention in detail:
[0030] Enterprises (that is, the service party in the present invention) often need to send short messages (that is, push information) to users, and some short messages need to include some enterprise-related hyperlinks. Short message virtu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More