Method, device and equipment for protecting SYN Flood attack
A packet and client technology, applied in the field of communication security, can solve problems such as hacker attacks, coarse-grained filtering conditions for legitimate IPs, and unsolved hacker SYNFlood attacks, so as to ensure normal operation and improve attack protection capabilities.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
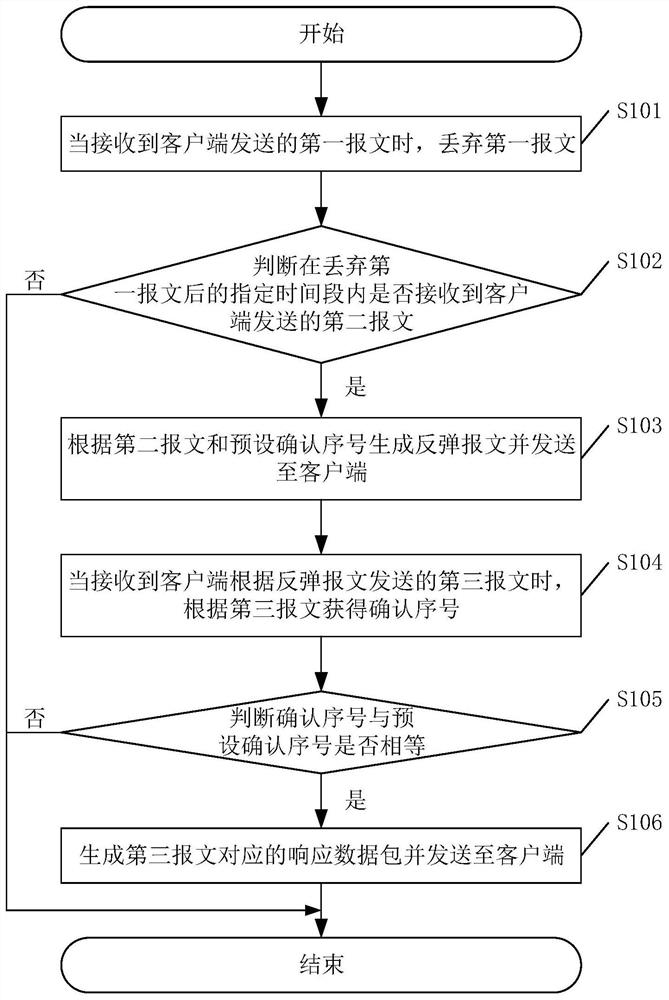
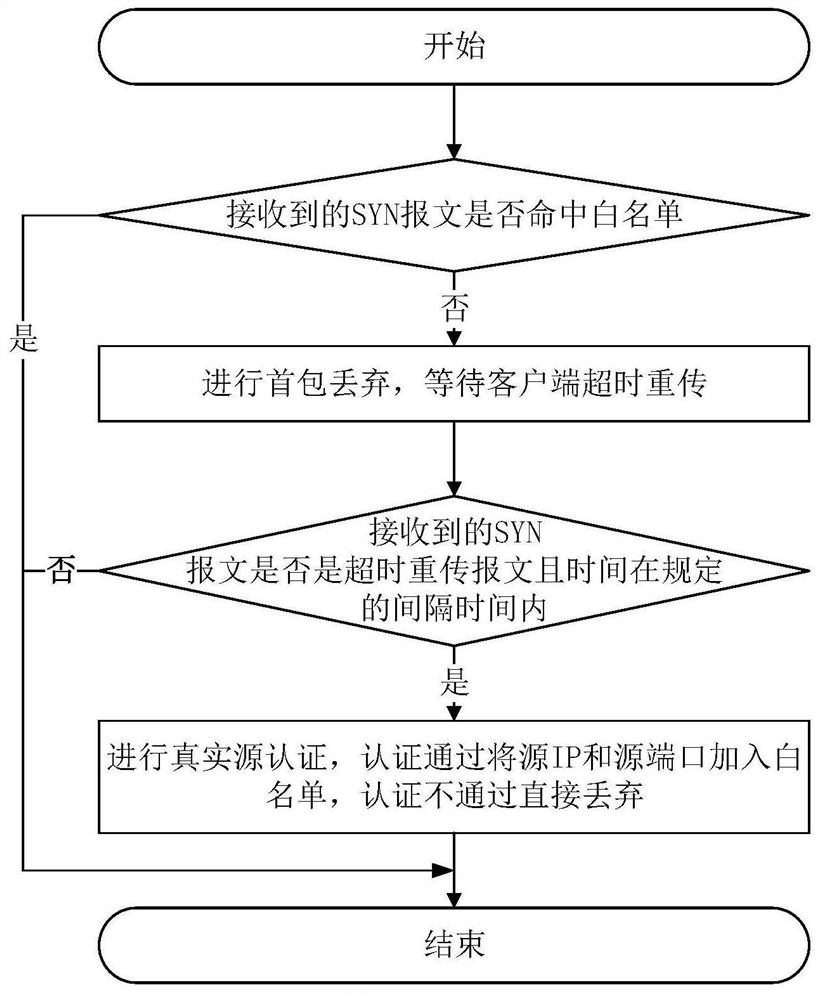
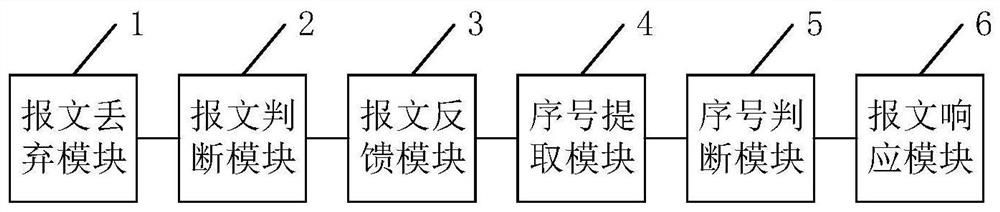
[0055] The core of this application is to provide a method for protecting against SYN Flood attacks. This method for protecting against SYN Flood attacks can effectively solve the problem that hackers use legal IPs to carry out SYN Flood attacks, further improve the attack protection capabilities of the system, and ensure the normal operation of the system. Operation; another core of the present application is to provide a device, system and computer-readable storage medium for preventing SYN Flood attacks, which also have the above-mentioned beneficial effects.
[0056]In order to describe the technical solutions in the embodiments of the present application more clearly and completely, the technical solutions in the embodiments of the present application will be introduced below in conjunction with the drawings in the embodiments of the present application. Apparently, the described embodiments are only some of the embodiments of this application, not all of them. Based on t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More