Application program vulnerability detection method and device, computer equipment and storage medium
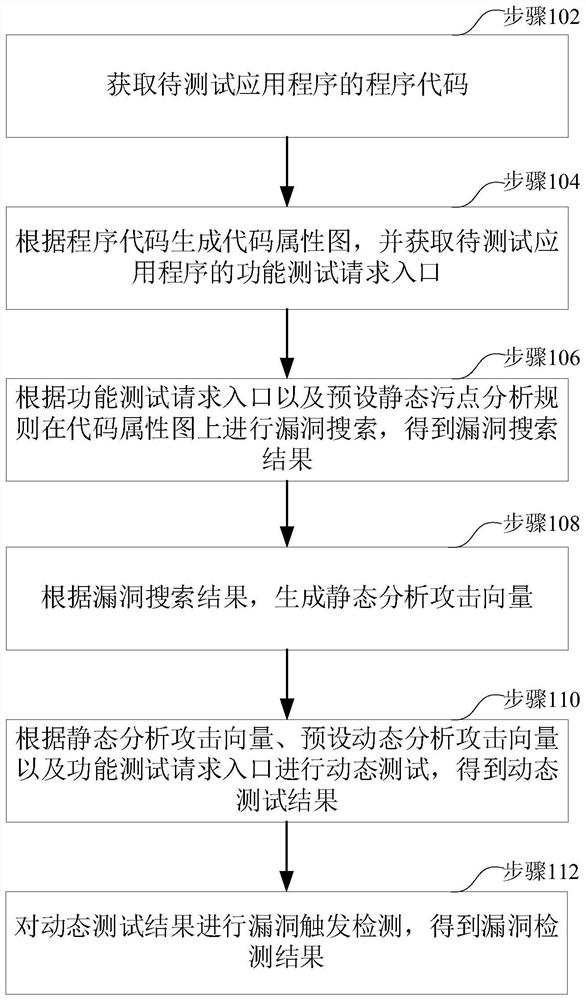
An application program and vulnerability detection technology, which is applied in the computer field, can solve the problems of low accuracy rate of security testing and high false alarm rate of vulnerabilities, and achieve the effect of improving the accuracy rate of security testing and reducing the rate of false alarms of vulnerabilities
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] This application relates to artificial intelligence technology. Artificial intelligence is the theory, method, technology and application system that uses digital computers or machines controlled by digital computers to simulate, extend and expand human intelligence, perceive the environment, acquire knowledge and use knowledge to obtain the best results. In other words, artificial intelligence is a comprehensive technique of computer science that attempts to understand the nature of intelligence and produce a new kind of intelligent machine that can respond in a similar way to human intelligence. Artificial intelligence is to study the design principles and implementation methods of various intelligent machines, so that the machines have the functions of perception, reasoning and decision-making.
[0045] Artificial intelligence technology is a comprehensive subject that involves a wide range of fields, including both hardware-level technology and software-level technol...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More