Computer application program verification method
A technology of application program and verification method, applied in the computer field, can solve the problems that the thief is difficult to escape and the computer application program is easy to leak, and achieves the effect of improving security and solving the problem of easy leakage.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0014] In conjunction with the accompanying drawings, the present invention will be described in further detail.
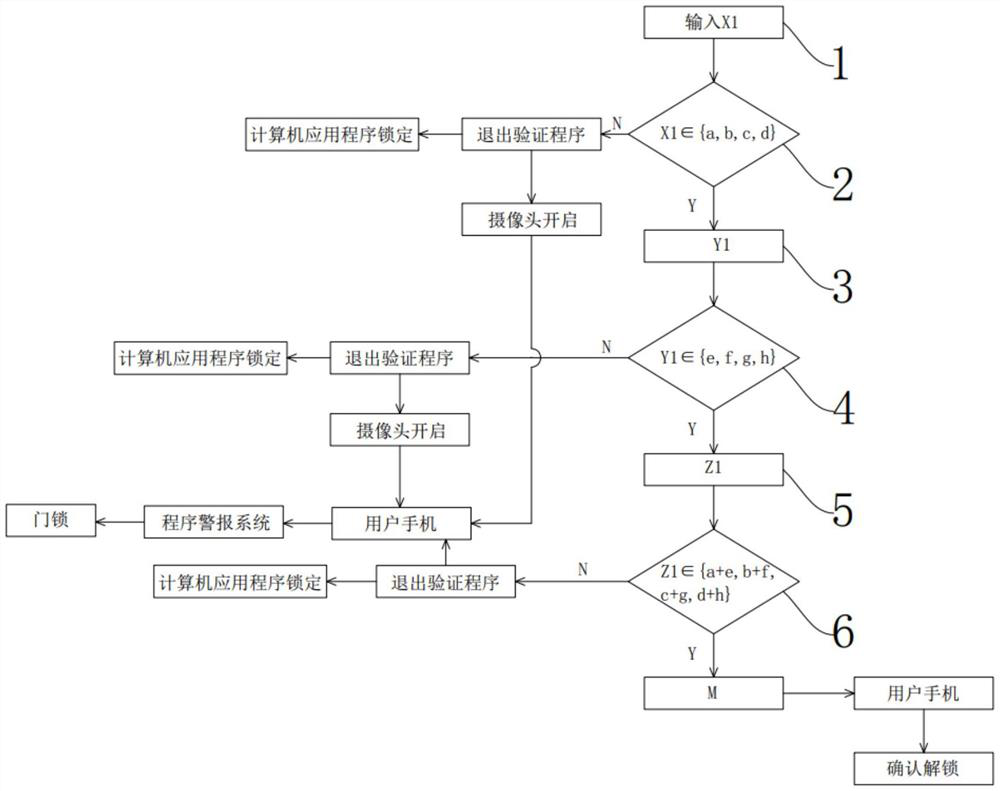
[0015] Such as figure 1 As shown, a computer application verification method of the present invention includes assignment one 1, verification one 2, assignment two 3, verification two 4, assignment three 5 and verification three 6, the assignment one 1 input X1, the verification one 2. Verify whether X1 is consistent, and if so, enter the link of assignment 23, if not, exit the verification program, and the computer application program is locked; said assignment 23 enters Y1, and said verification 24 verifies whether Y1 is consistent, if it is consistent, Then enter the link of assignment 35, if it does not match, then exit the verification program, and the computer application program is locked; the assignment 35 is input into Z1, and the verification 36 verifies whether Z1 matches, if it matches, it will be transmitted to the user's mobile phone, if it does not ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More