Safety time synchronization method based on node identity recognition
A security time and identity recognition technology, applied in synchronization devices, security devices, network topology, etc., can solve problems such as failure to defend against witch attacks, loss of synchronization, etc., to reduce packet overhead, reduce communication energy consumption, and avoid channel collisions. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
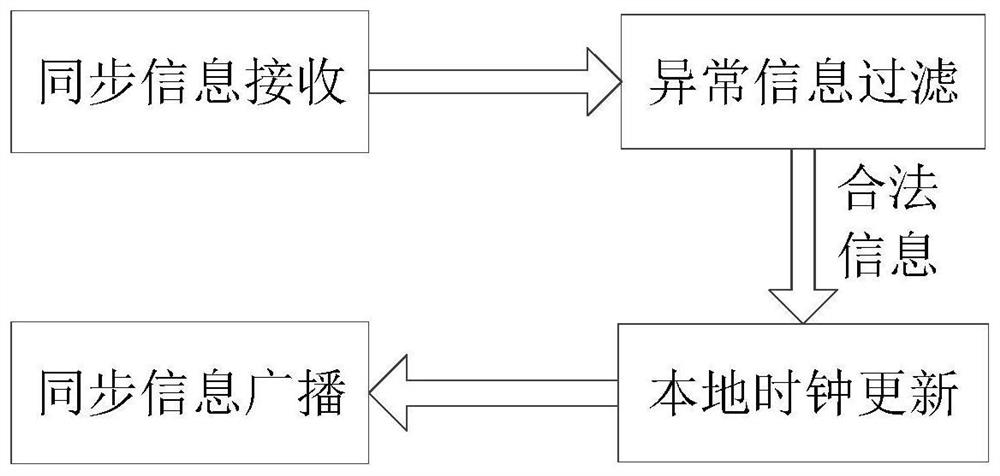
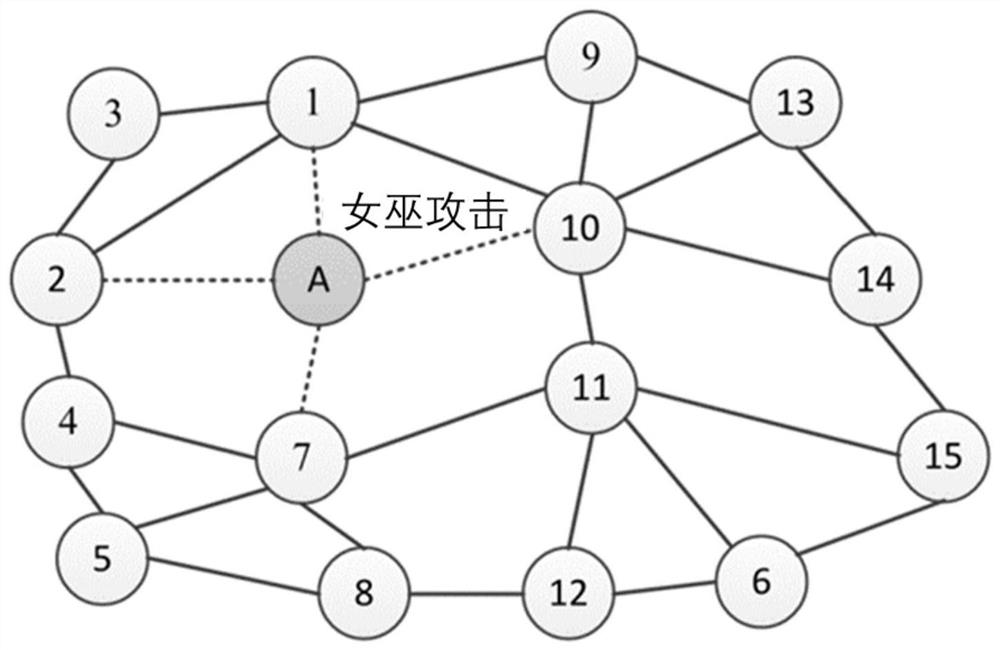
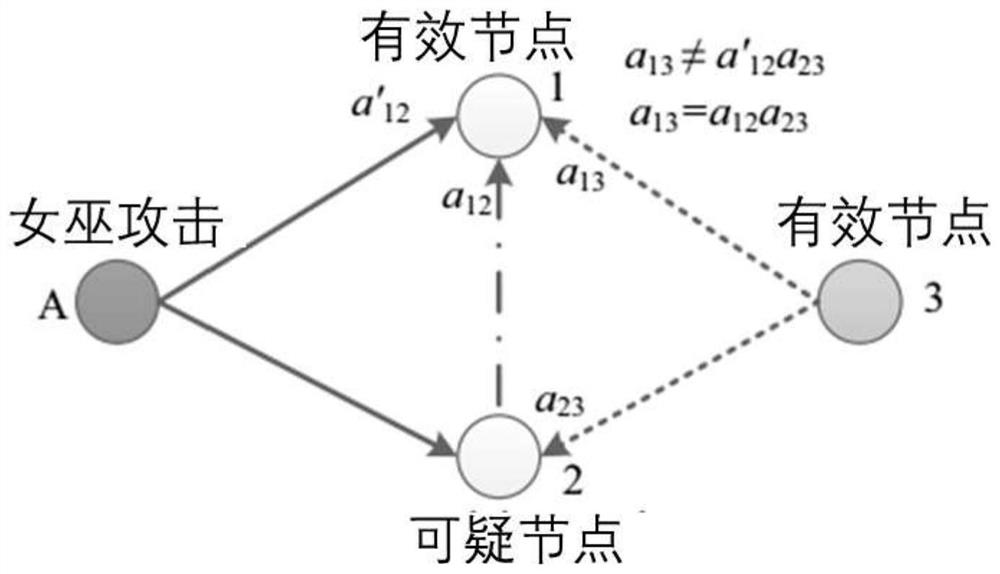
[0038] The invention utilizes the uniqueness of the relative clock slope of the sensor node to check and filter the abnormal information, then executes the corresponding synchronization algorithm by using legal information, and broadcasts the current clock state information, finally realizing the time synchronization of the whole network. The traditional secure time synchronization method based on information encryption and authentication cannot compensate cloc...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More