Vulnerability detection method and device, equipment and storage medium
A vulnerability detection and detection technology, applied in the field of network information security, can solve the problems of low precision, high false alarm rate/missing negative rate, etc., achieve low false positive rate and false negative rate, high accuracy rate, and alleviate high false positive rate effect of influence
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
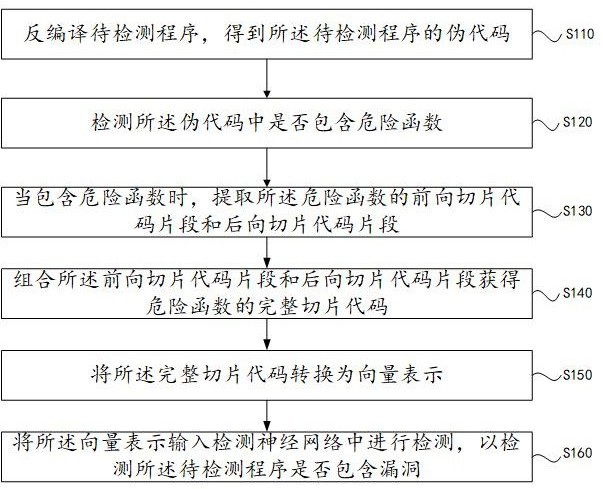
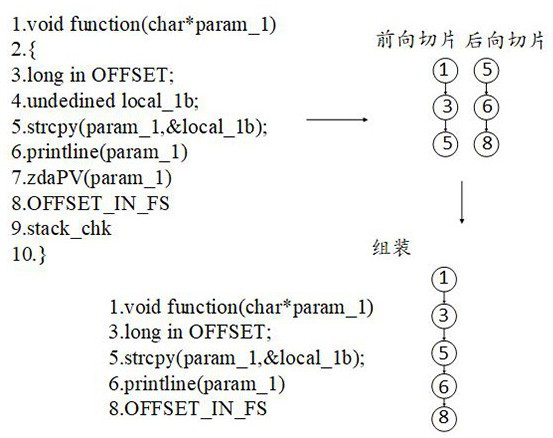
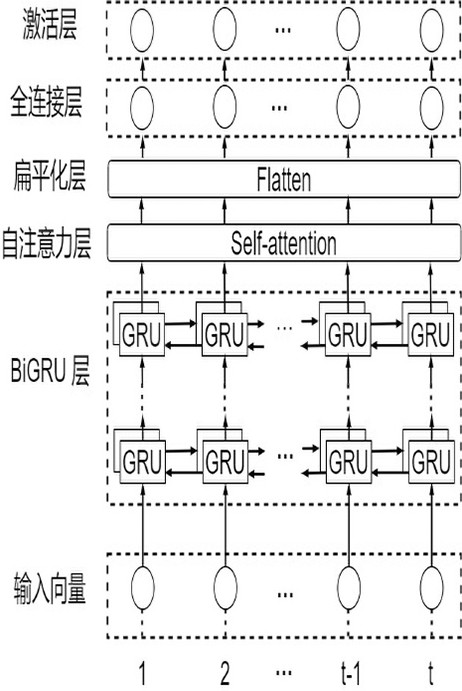
Method used
Image
Examples
Embodiment Construction
[0045] Next, the technical scheme in the present application will be clear and completely, and the embodiments described herein are described herein, and not all of the embodiments of the present disclosure, not all of the embodiments of the present application. Based on the embodiments in this application, all other embodiments obtained by those of ordinary skill in the art without creative labor, are the scope of the present application.
[0046] There are still some problems with existing binary code clone vulnerability detection techniques, such as:
[0047] I. Pattern-based matching requires experts to define the cost of human labor costs, and typically produce a high false positive rate or leakage rate.
[0048] Second, code-based similarity detection can only detect code multiplex vulnerabilities, and for the case with different code structures, but there is a similar vulnerability triggering scene, it will lead to higher missing.
[0049] Third, due to the existence of the...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More