Reflection attack detection method and device and electronic equipment
A reflection attack and detection method technology, applied in the field of network security, can solve problems such as economic loss, great harm, and low cost, and achieve the effects of improving security, reducing operating burden, and responding quickly
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
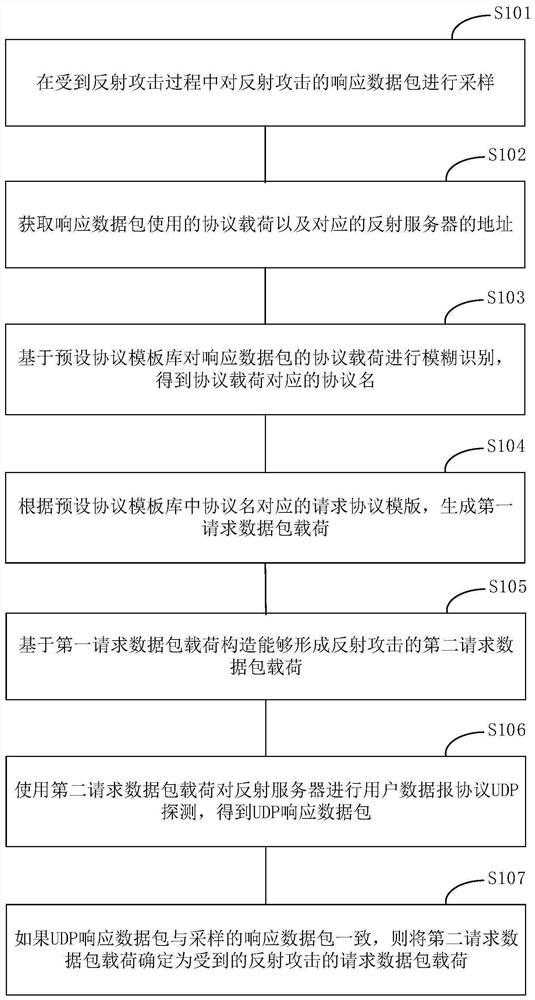
[0035] Exemplary embodiments of the present disclosure are described below in conjunction with the accompanying drawings, which include various details of the embodiments of the present disclosure to facilitate understanding, and they should be regarded as exemplary only. Accordingly, those of ordinary skill in the art will recognize that various changes and modifications of the embodiments described herein can be made without departing from the scope and spirit of the disclosure. Also, descriptions of well-known functions and constructions are omitted in the following description for clarity and conciseness.
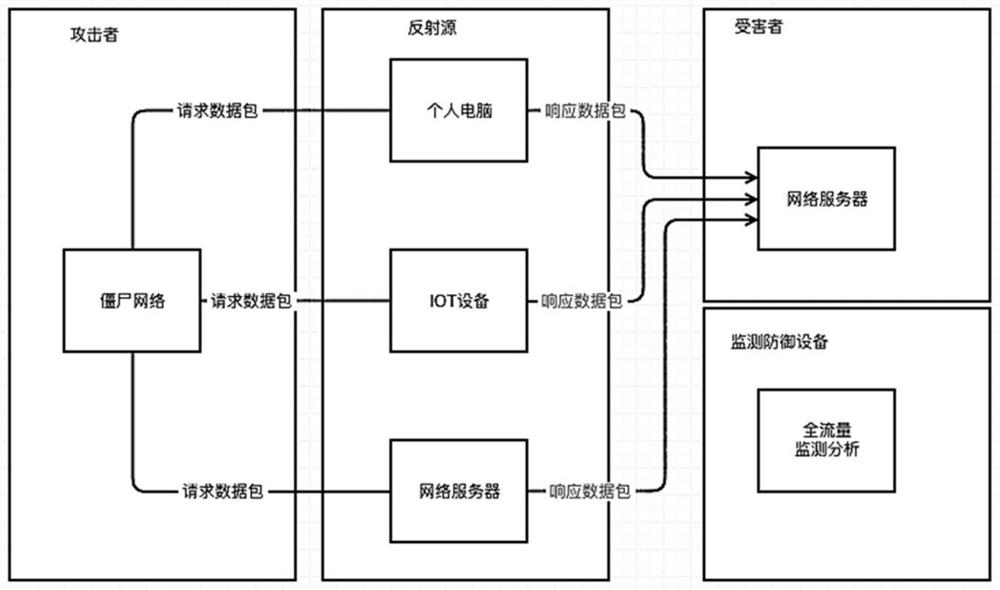
[0036] In the current network security confrontation scenario, security personnel usually quickly restore reflection attack methods and issue attack reports, so as to provide early warning of network attacks, promote reflection source governance, and achieve the purpose of mitigating network attacks. However, in most scenarios, for the sampled protocol data, it mainly r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More