Control method of intelligent terminal, man-machine interaction equipment and intelligent terminal
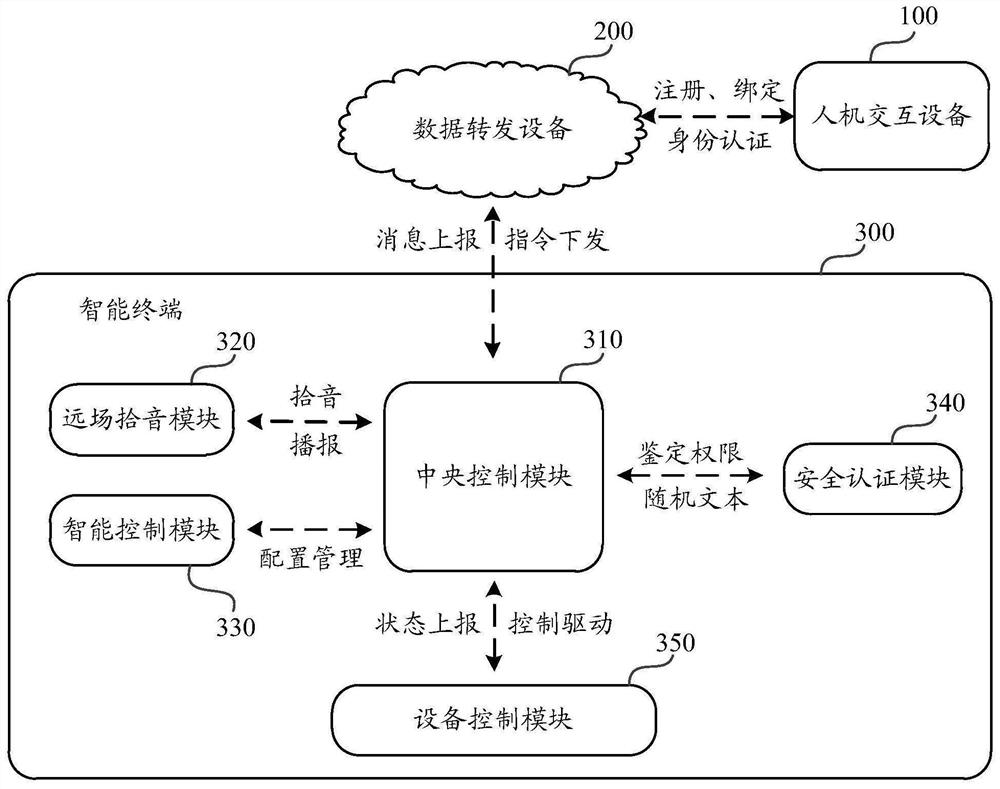
A technology of human-computer interaction equipment and intelligent terminals, which is applied in the field of intelligent terminals and intelligent equipment, intelligent terminal control methods, and human-computer interaction equipment, and can solve problems such as low security level, unreliable security measures, and leakage of camera privacy information.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0104] Embodiment 1 Unblocking the lens
[0105] Based on the static password verification method of the human-computer interaction device input device access password, the voiceprint recognition technology is added to realize the two-factor authentication. For the control of terminal lens shading, the user is first prompted to enter the static password for smart terminal access. After the password matches, the user is prompted to speak the text information randomly specified by the security authentication module, and the human-computer interaction device sends the collected audio information to the security authentication module. The voiceprint recognition unit in the module is compared with the voiceprint features at the time of registration, and only users who are successfully matched can pass the security authentication and are allowed to call the underlying device access interface. This two-factor authentication method solves security problems such as inputting, transferr...
Embodiment 2
[0139] Embodiment 2 Realize lens shading
[0140] In the embodiment of the present invention, the automatic shading of the smart terminal is carried out through the intelligent mechanism such as automatic or timing of the intelligent control module, so that the intelligent control system can realize physical shading at sensitive time or when the user does not use the camera, ensuring that the camera is physically completely shaded. Use a reliable method to eliminate the possibility of user privacy leakage, and solve users' concerns about privacy leakage. During specific implementation, the automatic shading of the smart terminal is realized in the following two ways:
[0141] 1. Automatic execution mechanism: When the intelligent control system starts self-inspection (usually it will verify functions such as shading and cruising to ensure that the hardware and structure of shading and motor rotation control are effective), video calls, remote monitoring and other services or a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More