Allocation method and device for computing resources
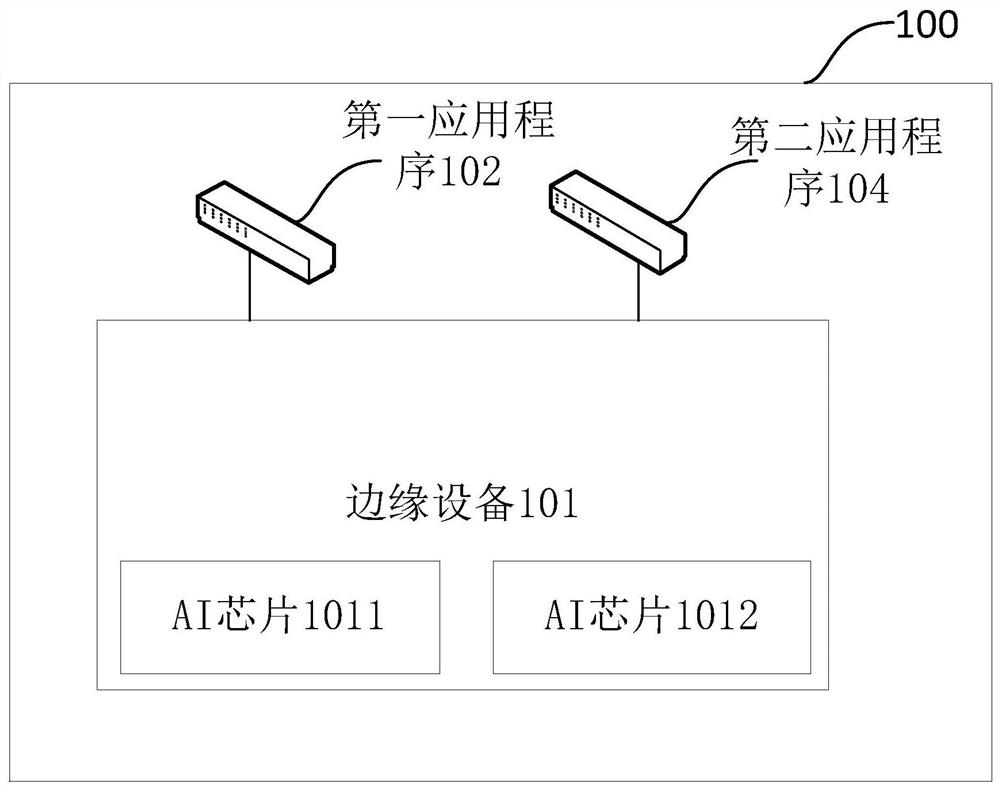
A technology of computing resources and allocation methods, applied in the field of Internet of Things, can solve the problems of competing for computing resources, unable to meet the computing needs of applications, and unreasonable use of computing resources.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0098] Embodiment 1: see Figure 4 , is an exemplary flow chart of a method for allocating computing resources in the embodiment of the present application, and the process may be executed by a first application program. Such as Figure 4 As shown, the following steps may be included:
[0099] Step 401: Send the first request to the edge device.
[0100] The first request here may contain the identity information of the first application, and related descriptions can be found in the above figure 2 The description in the embodiment of the method will not be repeated here.
[0101] Step 402: Determine whether the account creation is successful. If the account is successfully created, step 403 is executed, and if the account creation fails, step 401 is executed.
[0102] It should be understood that if the first application program receives the first response sent by the edge device, it can be considered that the account creation is successful; if the first application prog...
Embodiment 2
[0108] Embodiment 2: see Figure 5 , is an exemplary flow chart of a method for allocating computing resources provided in an embodiment of the present application, and the process may be executed by an edge device. Such as Figure 5 As shown, the following steps may be included:
[0109] Step 501: Receive computing resources requested by a first application program.
[0110] Among them, the relevant description of the requested computing resources can be found in the above figure 2 The description of the method embodiment shown in step 201-step 202 will not be repeated here.
[0111] Step 502: Determine whether the requested computing resource exceeds a first threshold. If it exceeds, execute step 503, and if not, execute step 504.
[0112] The first threshold here may be predetermined according to empirical values, which is not specifically limited in this application. Among them, related descriptions can be found in the above figure 2 The description of the embodim...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More