Implementation method of north-south micro-isolation architecture
An implementation method and architecture technology, which is applied in the implementation field of north-south micro-isolation architecture, can solve problems such as inability to form isolation, hundreds or thousands, or even tens of thousands, and hidden dangers in network security, so as to improve security. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0016] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
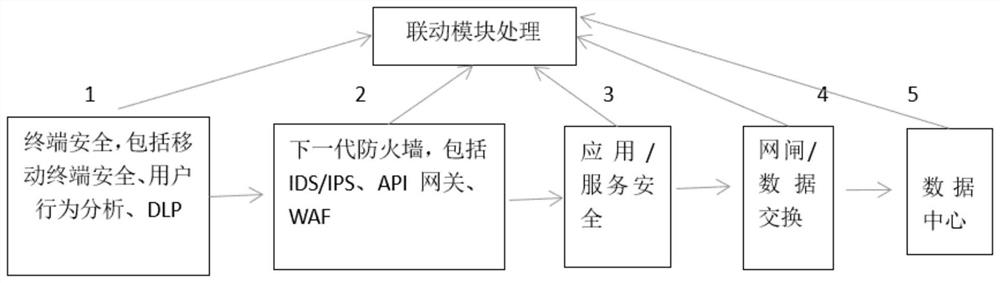
[0017] Such as figure 1 As shown, the implementation method of a north-south micro-isolation architecture disclosed in the present invention includes the following steps:
[0018] (1) In the entire north-south network architecture, a zero-trust micro-isolation architecture is used for comprehensive reconstruction. The network elements in the micro-isolation architecture include but are not limited to terminals, next-generation firewalls, and application / service security. Gatekeeper / data exchange and data center; the described micro-isolation architecture can be:
[0019] 1) Based on the micro-isolation of the host agent, the data flow in the network is visible, and the data flow is transmitted to the central server through the agent located in the network endpoint.
[0020] 2) Micro-isolation is realized based on the virtual machine monitorin...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More