Security protection method and device, electronic equipment and storage medium
A security protection and security technology, applied in the field of network security, can solve the problems of finding security holes, losing accounts and passwords, hacking attacks, etc., and achieve the effect of reducing security hazards
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] Embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings.
[0054] It should be clear that the described embodiments are only some of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
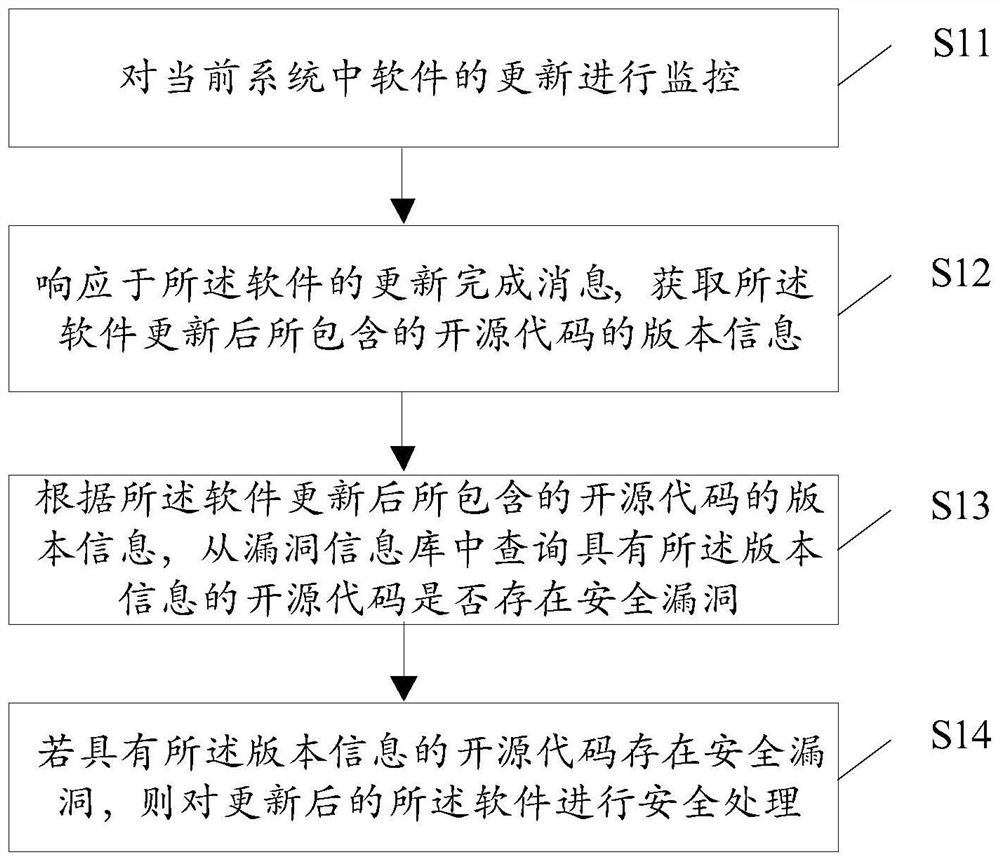
[0055] An embodiment of the present invention provides a security protection method, which can be executed by a security protection device implemented by software and / or hardware, see figure 1 , the method can include:
[0056] S11, monitoring the update of the software in the current system; the software contains open source codes;
[0057]Open source code refers to a series of software collections whose source code is open and can be used, copied, modified and redistributed freely. At present, when developing sof...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More