Data encryption method, federal modeling method and device and computer equipment
A data encryption and data technology, applied in digital data protection, integrated learning and other directions, can solve the problem of leaking the intersection ID of both parties
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0027] The technical solutions of the present invention will be clearly and completely described below in conjunction with the accompanying drawings. Apparently, the described embodiments are some of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0028] In addition, the technical features involved in the different embodiments of the present invention described below may be combined with each other as long as there is no conflict with each other.
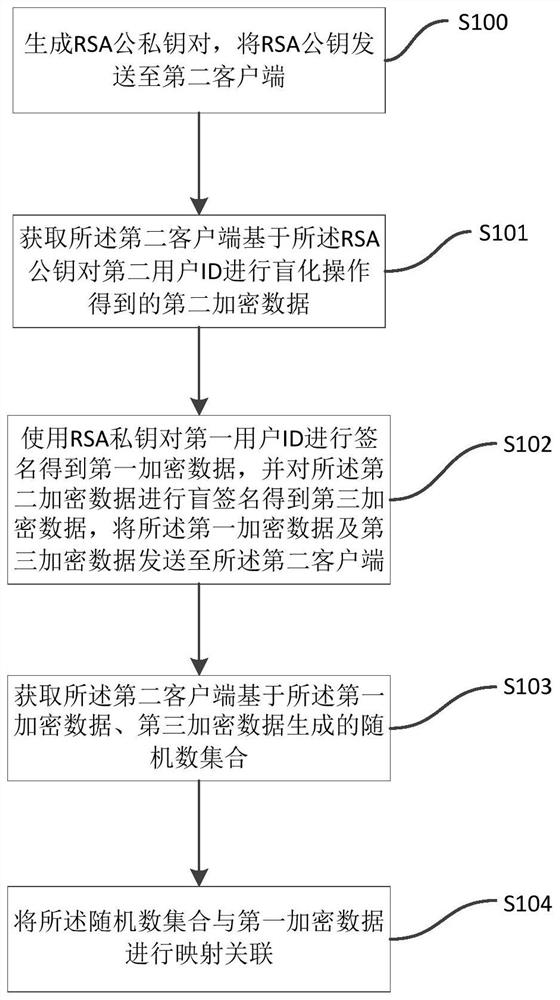
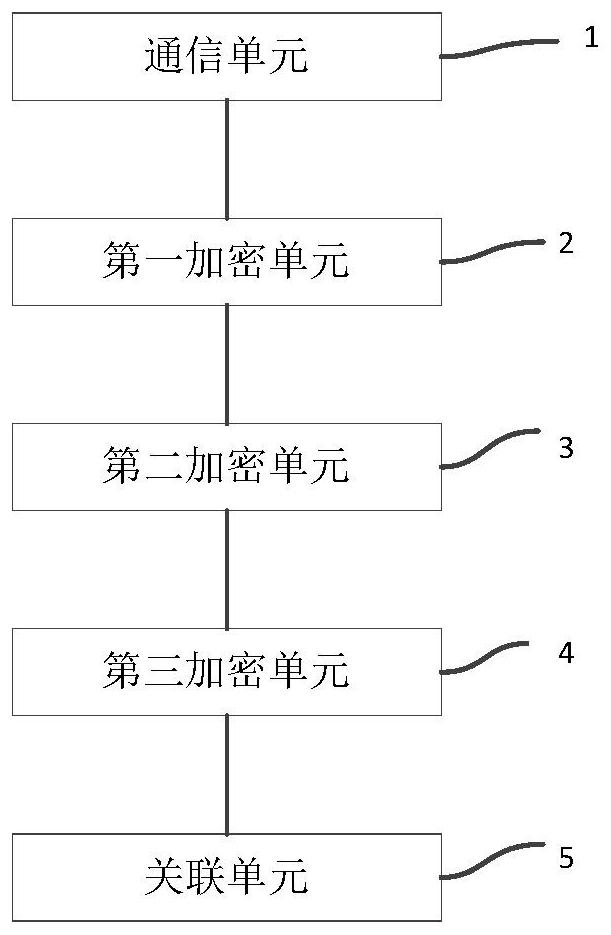
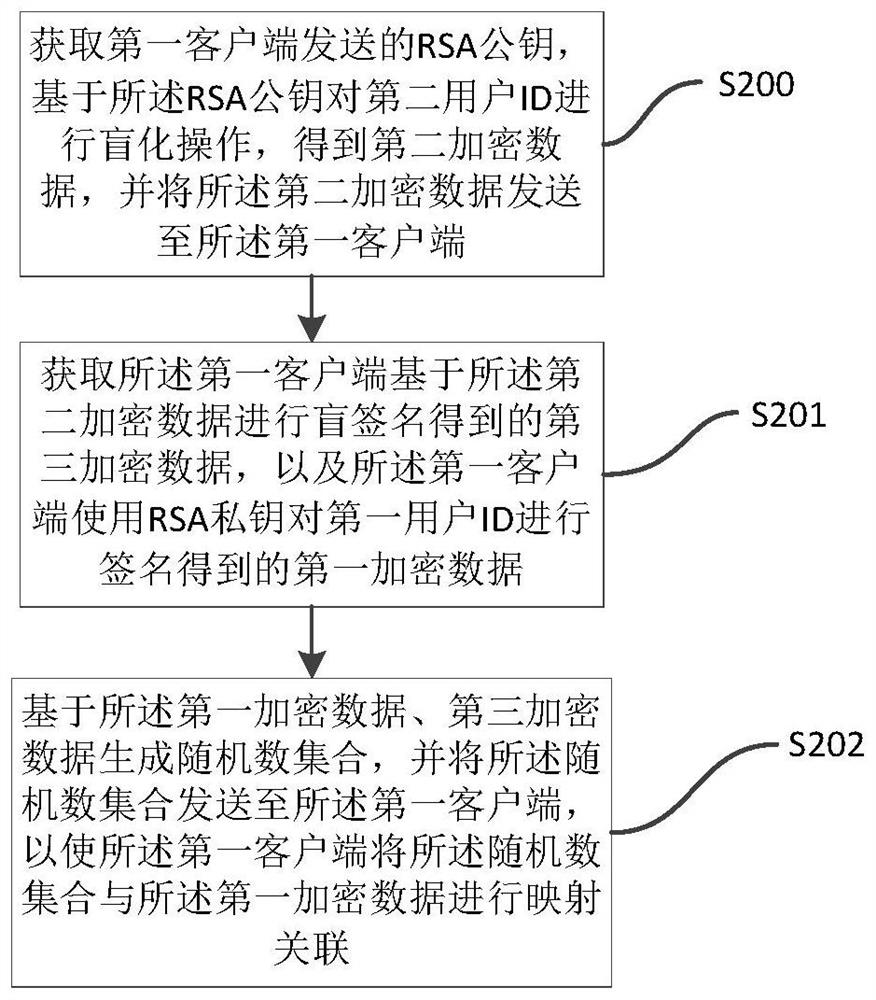
[0029] In the embodiment of the present invention, during the data interaction process between the first client and the second client, the interaction data is encrypted and decrypted, and the interaction data is generated through a blind-unblinding operation after the interaction data is blindly signed. The r...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More