Multi-party secure multiplication
A multi-party and secure technology, applied in the field of information security, can solve problems such as exposing private data
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
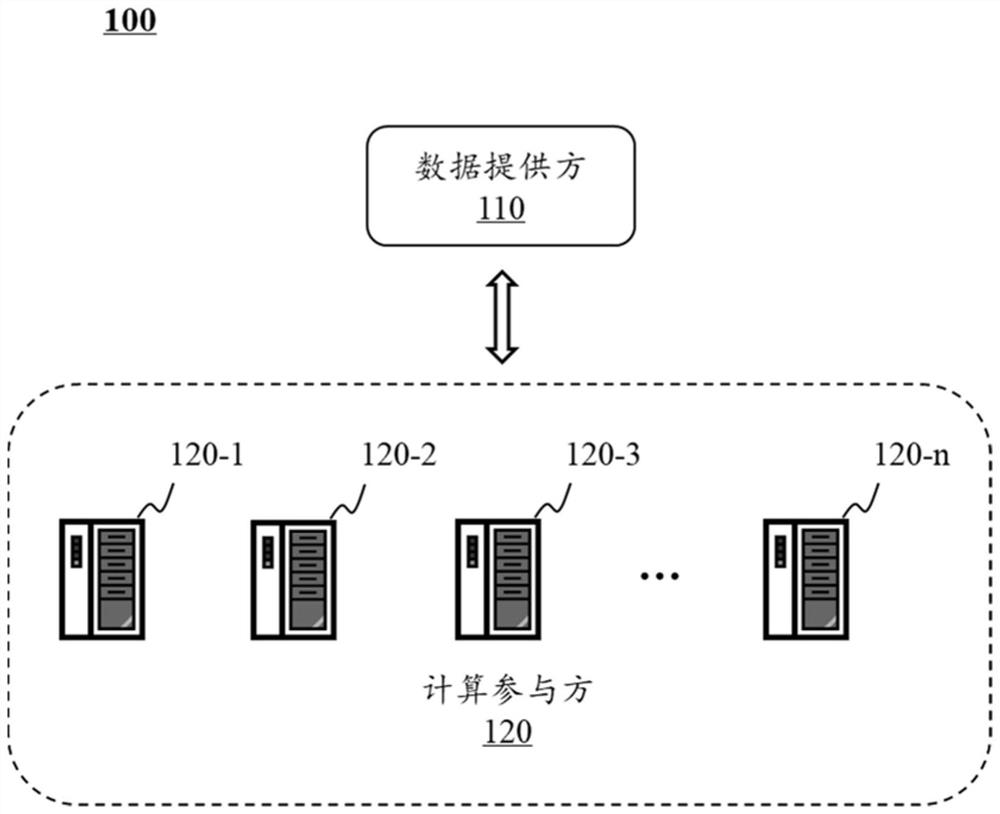
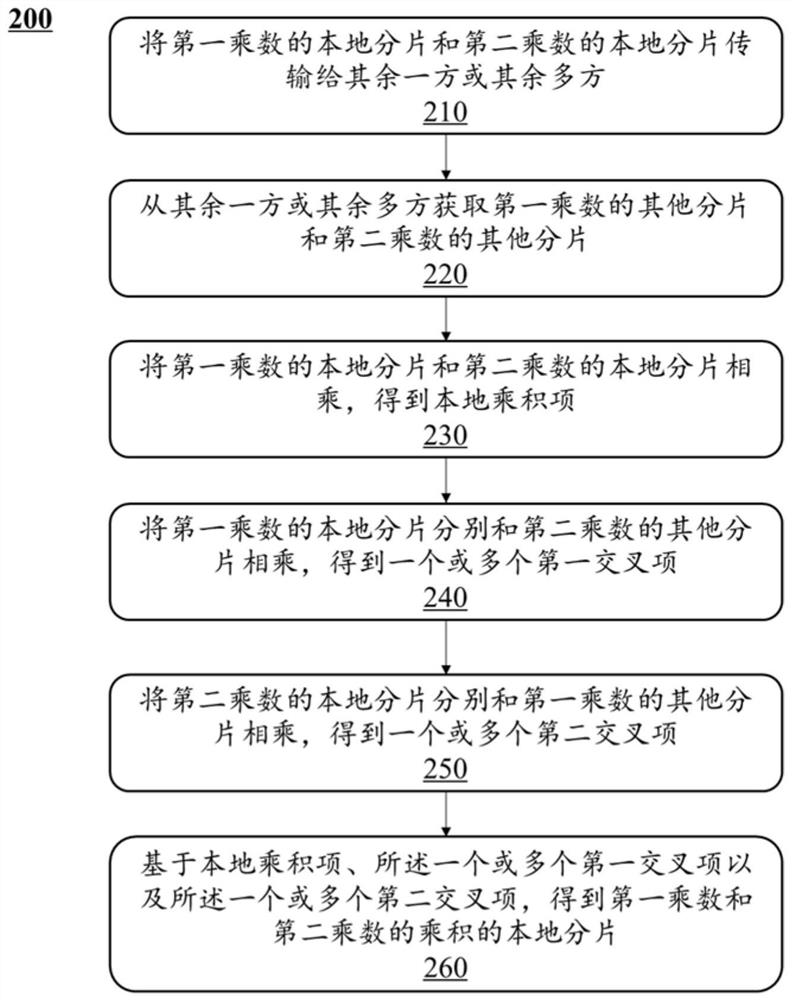
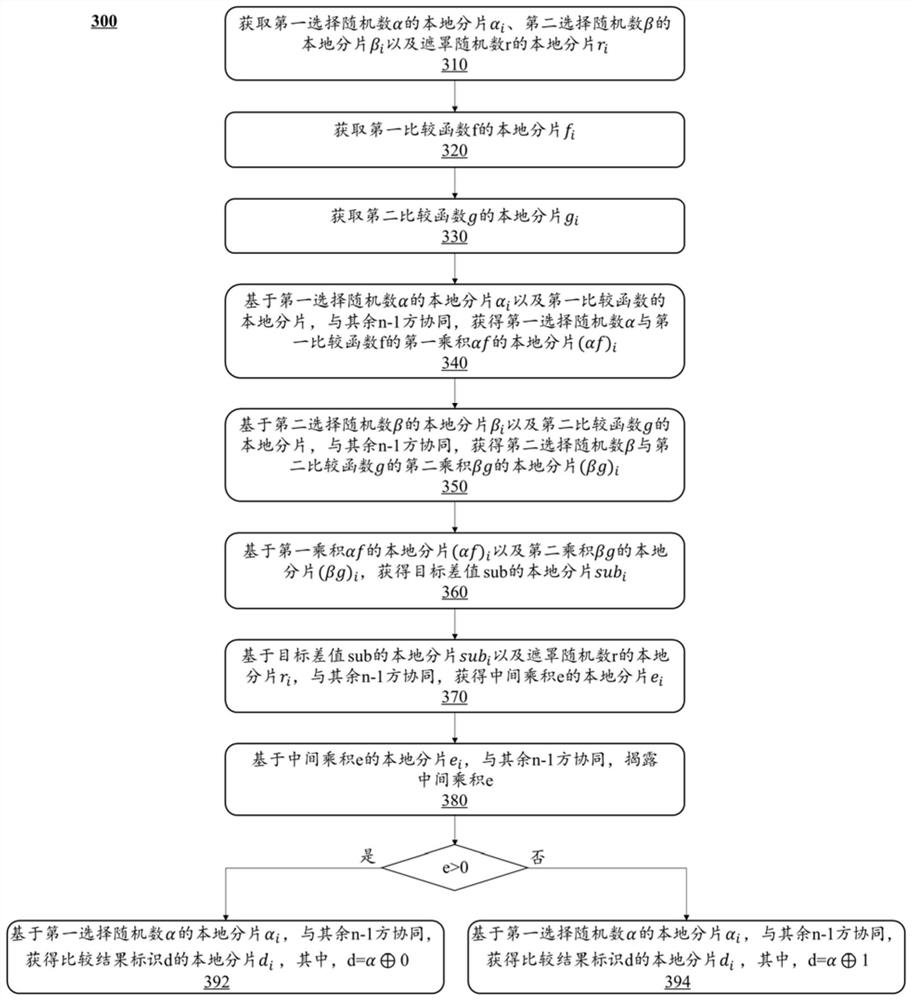
[0058] In order to illustrate the technical solutions of the embodiments of the present specification more clearly, the following briefly introduces the accompanying drawings that are used in the description of the embodiments. Obviously, the accompanying drawings in the following description are only some examples or embodiments of the present specification. For those of ordinary skill in the art, the present specification can also be applied to the present specification according to these drawings without any creative effort. other similar situations. Unless obvious from the locale or otherwise specified, the same reference numbers in the figures represent the same structure or operation.
[0059] It should be understood that "system", "device", "unit" and / or "module" as used herein is a method used to distinguish different components, elements, parts, parts or assemblies at different levels. However, other words may be replaced by other expressions if they serve the same p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More