Security maturity assessment method.
A mature and safe technology, applied in computer security devices, instruments, preventing unauthorized use of memory, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0013] Exemplary embodiments of the present invention are described with reference to the accompanying drawings. Throughout the drawings, for consistency, like items are indicated by like reference numerals.
[0014] In the following detailed description of the invention, numerous specific details are set forth in order to provide a better understanding of the invention. It will be apparent, however, to one skilled in the art that the present invention may be practiced without these specific details. In other instances, well-known features have not been described in detail so as not to obscure the invention.
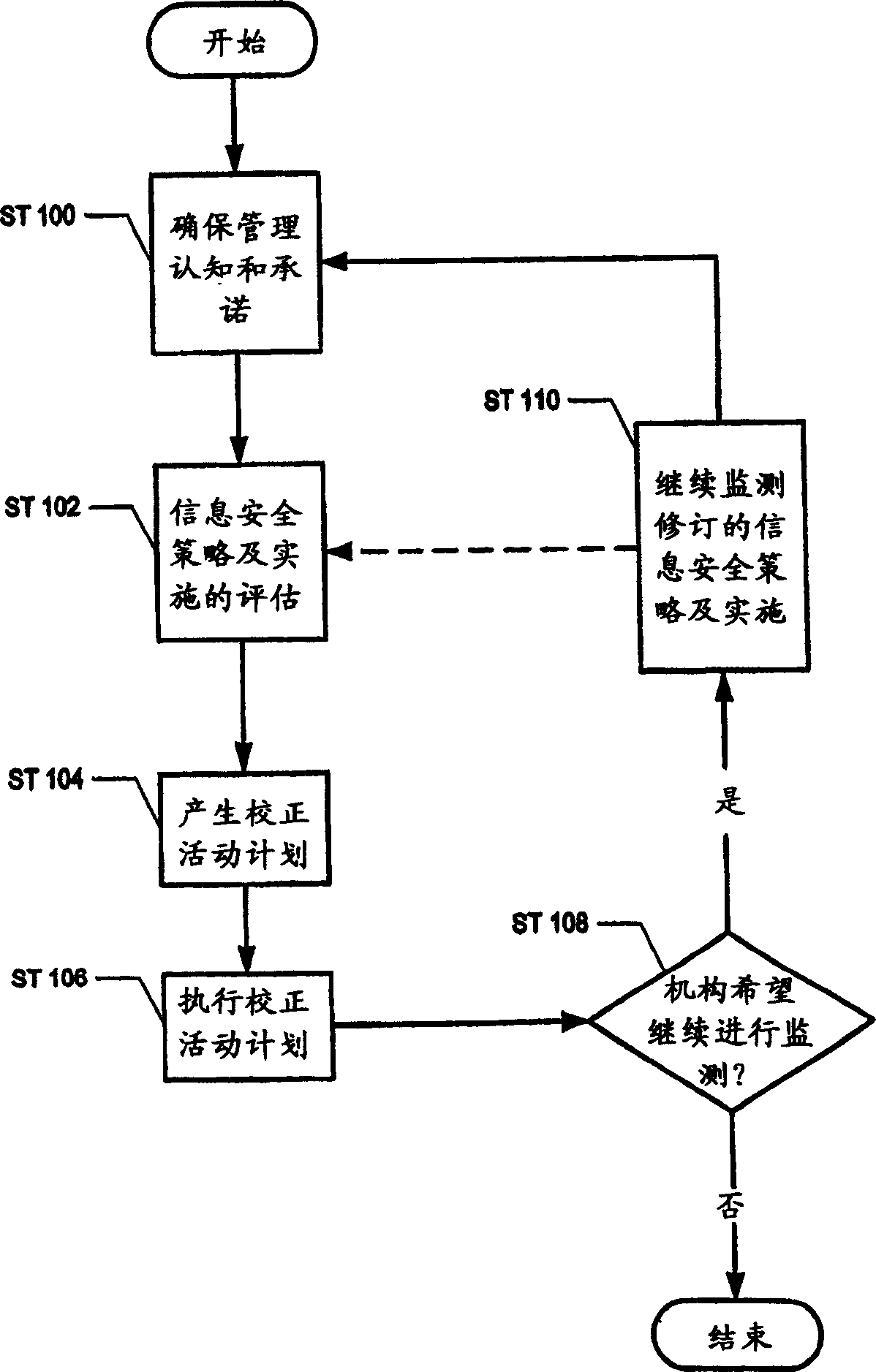
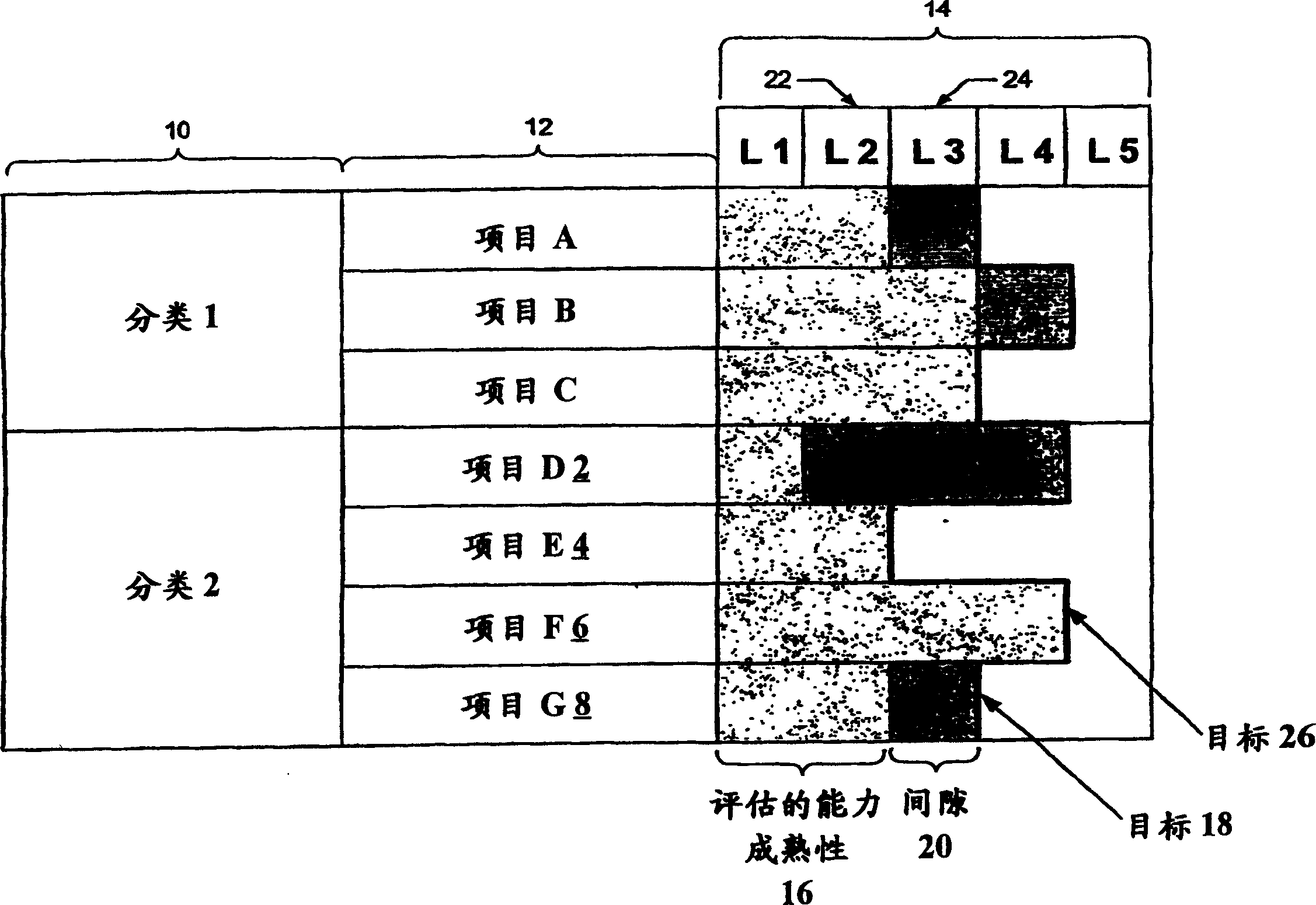
[0015] The present invention relates to a method for assessing the security maturity of an organization. In addition, the present invention also relates to utilizing a security assessment matrix to assess an organization's security maturity. In addition, the present invention also relates to base the safety assessment matrix on the BS7799 / ISO17799 standard and the Cap...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More