Data encryption/decryption method and inspection system
A monitoring system and data technology, applied in analog security/charging systems, closed-circuit television systems, digital transmission systems, etc., can solve problems such as difficulty in obtaining synchronization, difficult key management, and increased cost, and achieve easy implementation and key management. Handling simple effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
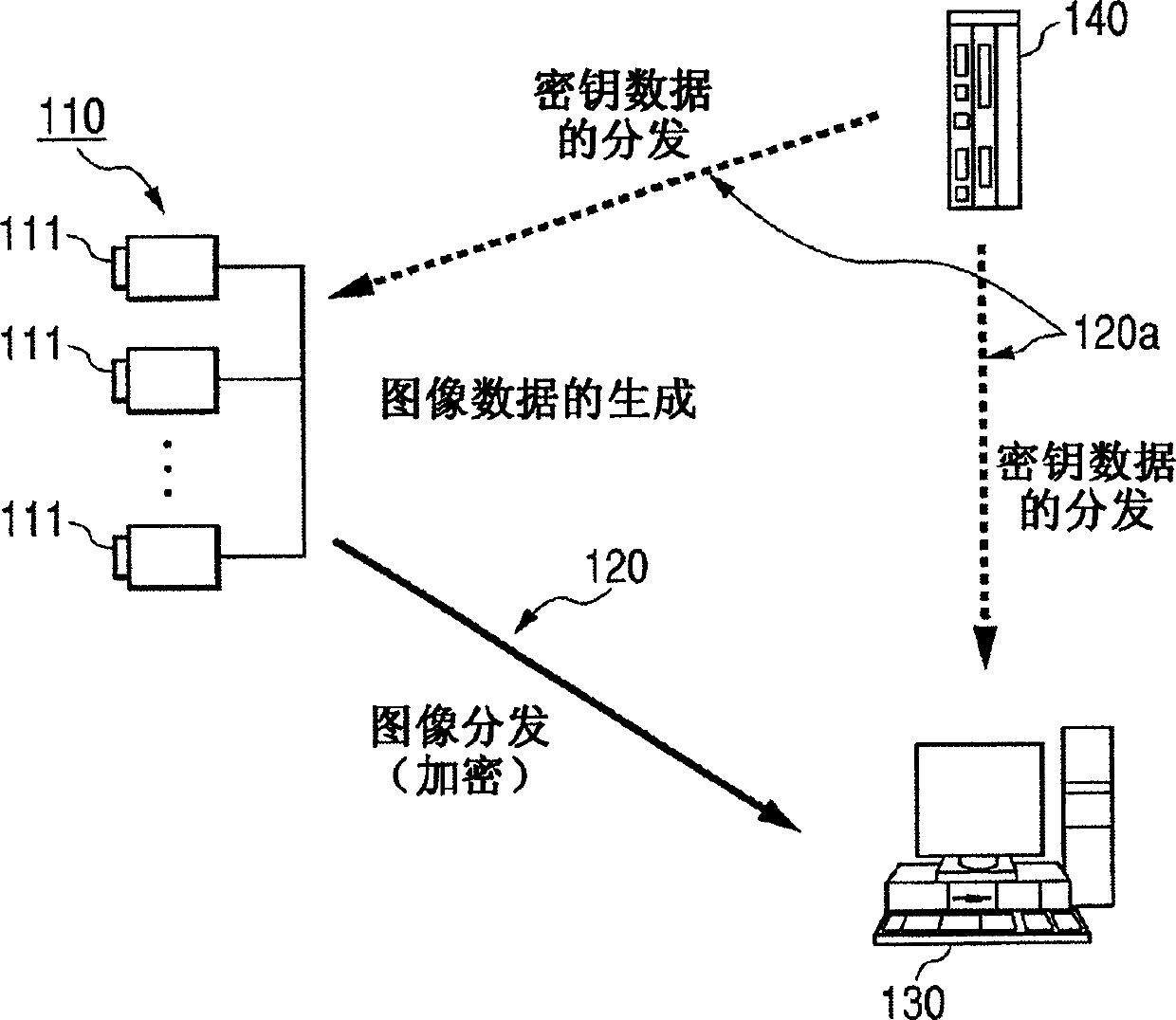
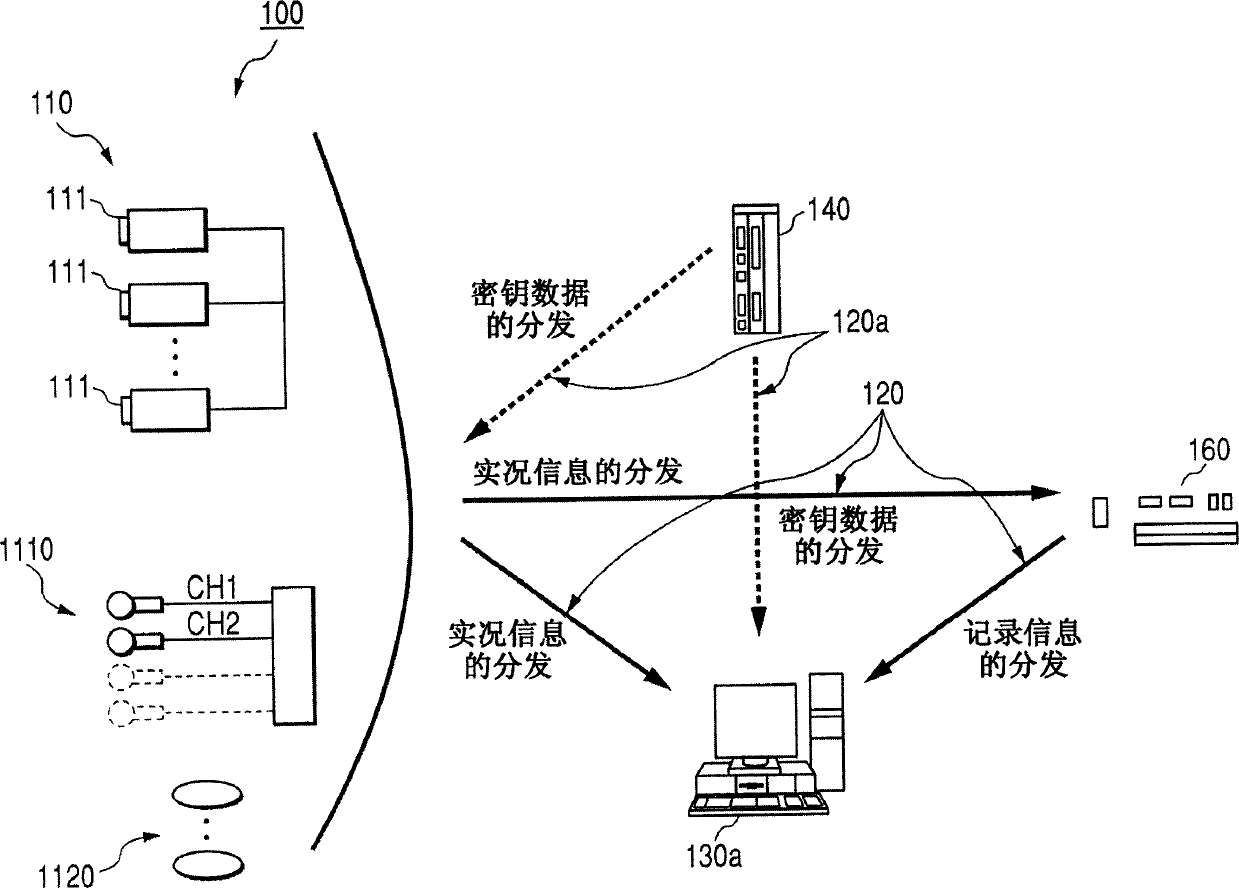
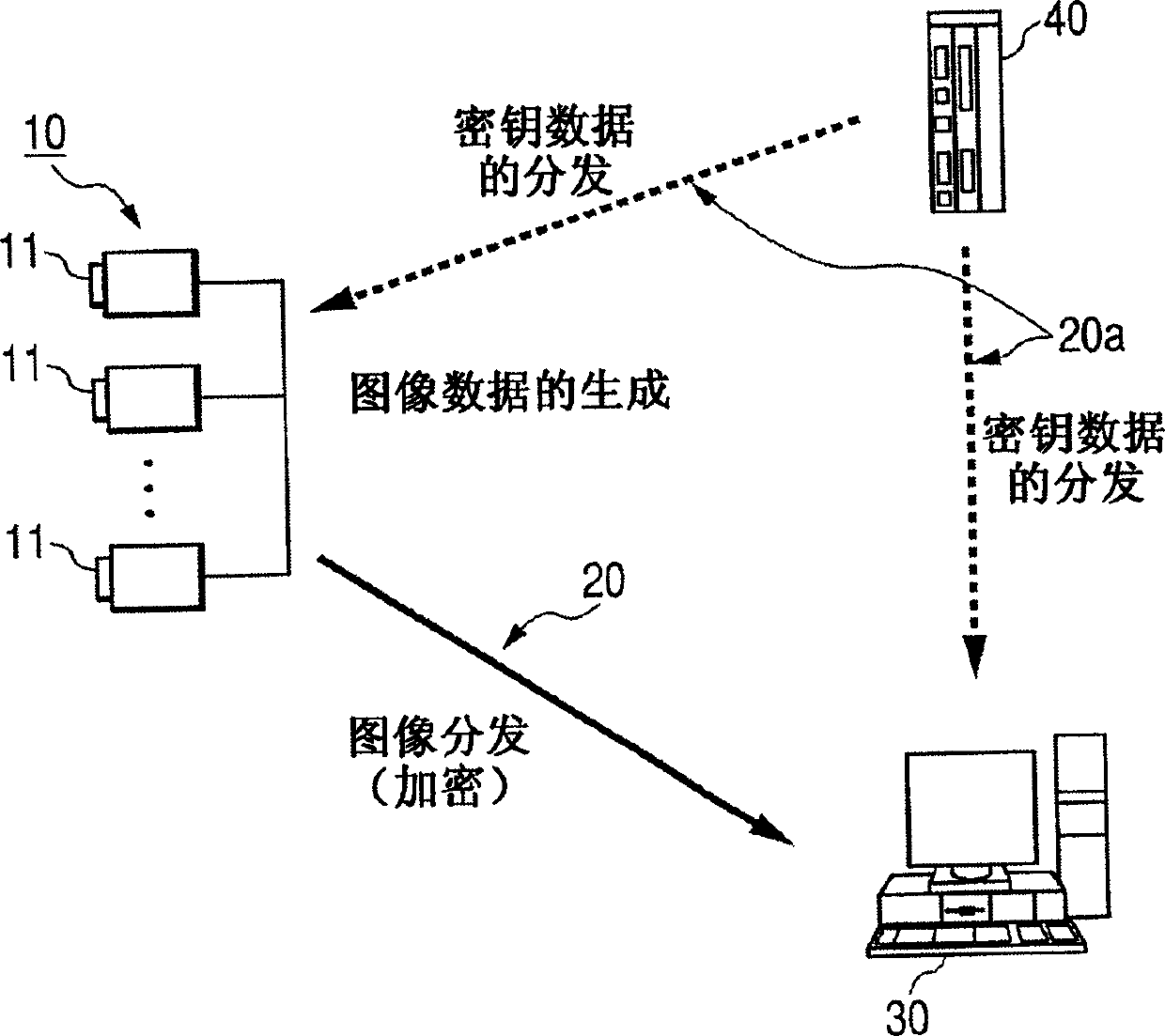
[0033] Embodiments of the present invention will now be described in detail with reference to the accompanying drawings. A data encryption / decryption method and a monitoring system will be described. In an embodiment, image data obtained by a surveillance camera is used. Figure 1 shows an embodiment of a monitoring system according to the invention.
[0034] The surveillance system shown in FIG. 1 has an image distribution device 110 including an image distribution unit 111 such as a surveillance camera, an image reproduction device 130 , and a key management device 140 . In this embodiment, the image distribution device 110 distributes encrypted image data to the image reproduction device 130 via the network 120 . Therefore, it is not necessary to secure the communication path with IPsec or SSL in order to secure the image data.
[0035] On the other hand, key information is transmitted in directions indicated by dotted arrows via the network 120a between the key managemen...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More