Security system, security method, and non-transitory computer readable medium
a security system and computer readable medium technology, applied in the field of security systems, can solve problems such as inefficiency in visual inspection, and achieve the effect of accurate detection of suspicious actions
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
first exemplary embodiment
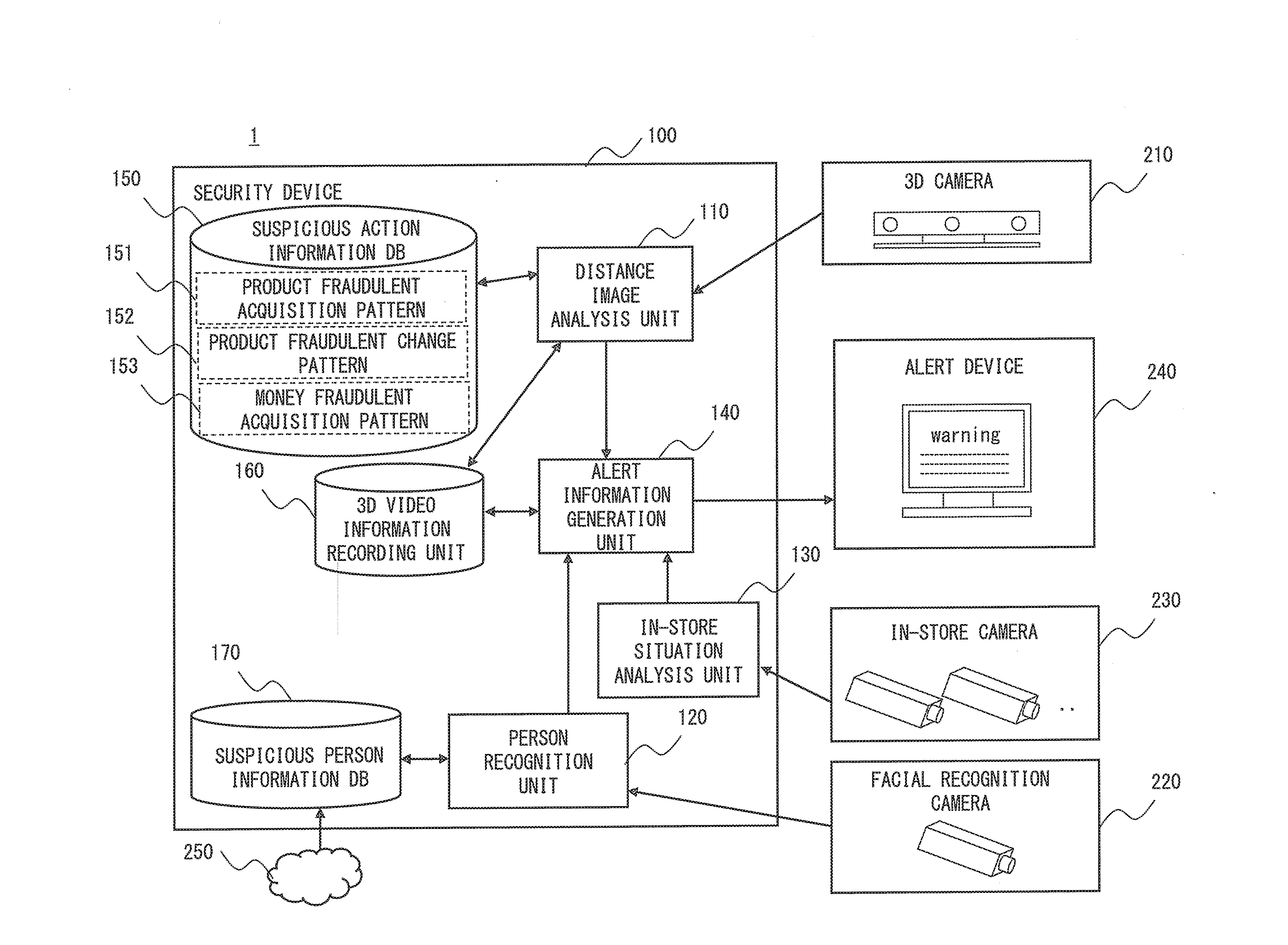
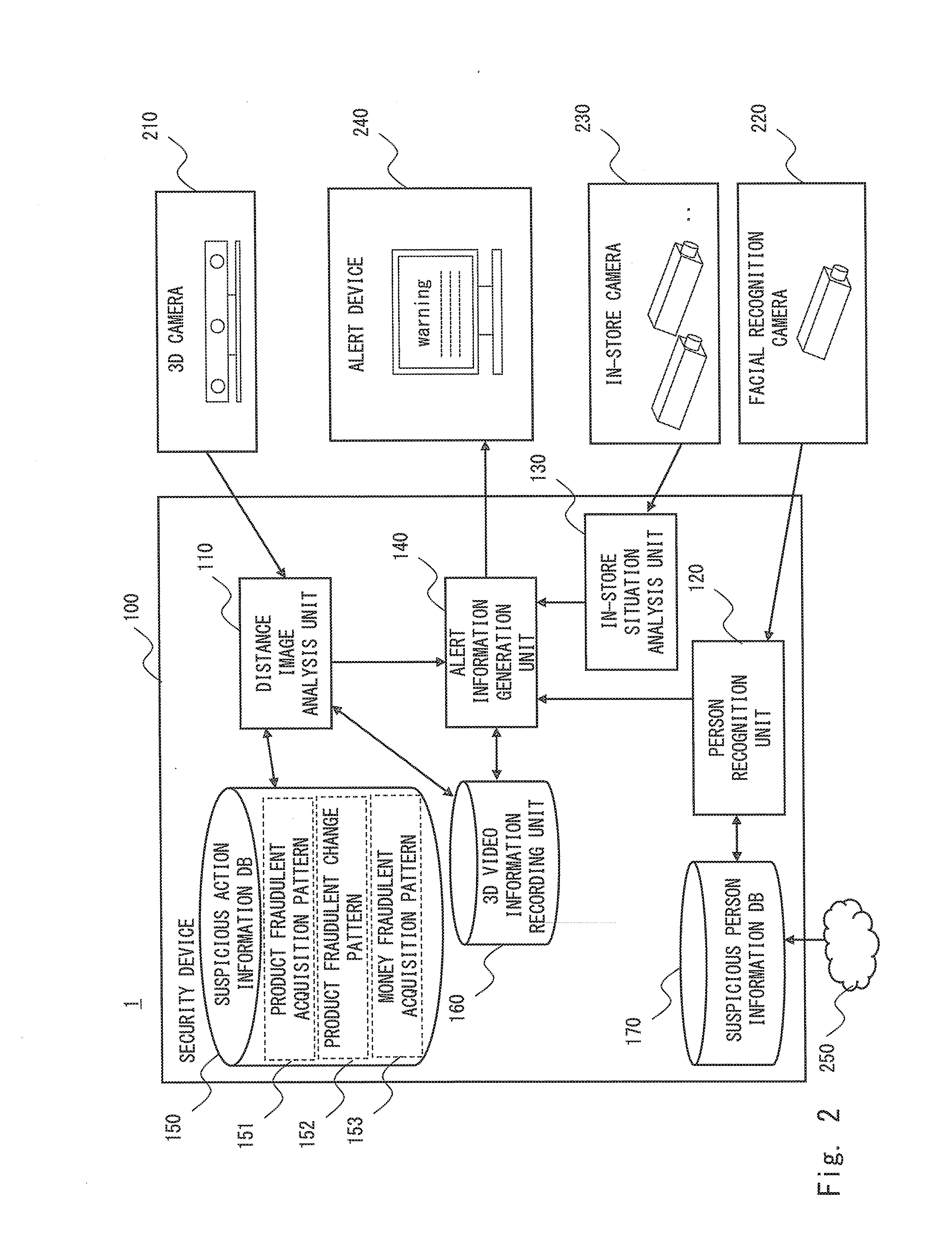
[0031]A first exemplary embodiment is described hereinafter with reference to the drawings. FIG. 2 is a block diagram showing the configuration of a security system according to this exemplary embodiment. This security system is a system that detects a suspicious action of a customer or a store staff in a store or the like and outputs (displays) an alert (alarm) and the like. Note that customer includes all persons who come to (enter) a store, and the store staff includes all persons who work in a store.
[0032]As shown in FIG. 2, a security system 1 according to this exemplary embodiment includes a security device 100, a 3D camera 210, a facial recognition camera 220, an in-store camera 230, and an alert device 240. For example, while the respective components of the security system 1 are placed in the same store, the security device 100 or the alert device 240 may be placed outside the store. Although it is assumed in the following description that the respective components of the s...
second exemplary embodiment
[0080]A second exemplary embodiment is described hereinafter with reference to the drawings. This exemplary embodiment is an example that, as a complement to the suspicious action recognition in the first exemplary embodiment, detects a suspicious action by detecting a deviant action from normal action information patterns. Specifically, the present invention is not limited to the example of the first exemplary embodiment, and a suspicious action may be determined by detecting a deviation from a store staff's normal action such as work at a cash register, rather than detecting an action of a store staff that embezzles the sales, appropriates a product (puts money in a pocket etc.) or gives a product to a customer as a conspirator without receiving a full price and the like.
[0081]FIG. 9 shows a configuration of a security system according to this exemplary embodiment. As shown in FIG. 9, in this exemplary embodiment, the security device 100 further includes a normal action informatio...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More