Secure guiding system, method, code signature construction method and authentication method
A security boot and code technology, applied in the field of communication, can solve the problems that the elliptic curve cryptography technology has not been well applied, and achieve the effects of simplifying key management, protecting the security of the operating system, and preventing the loss of users
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
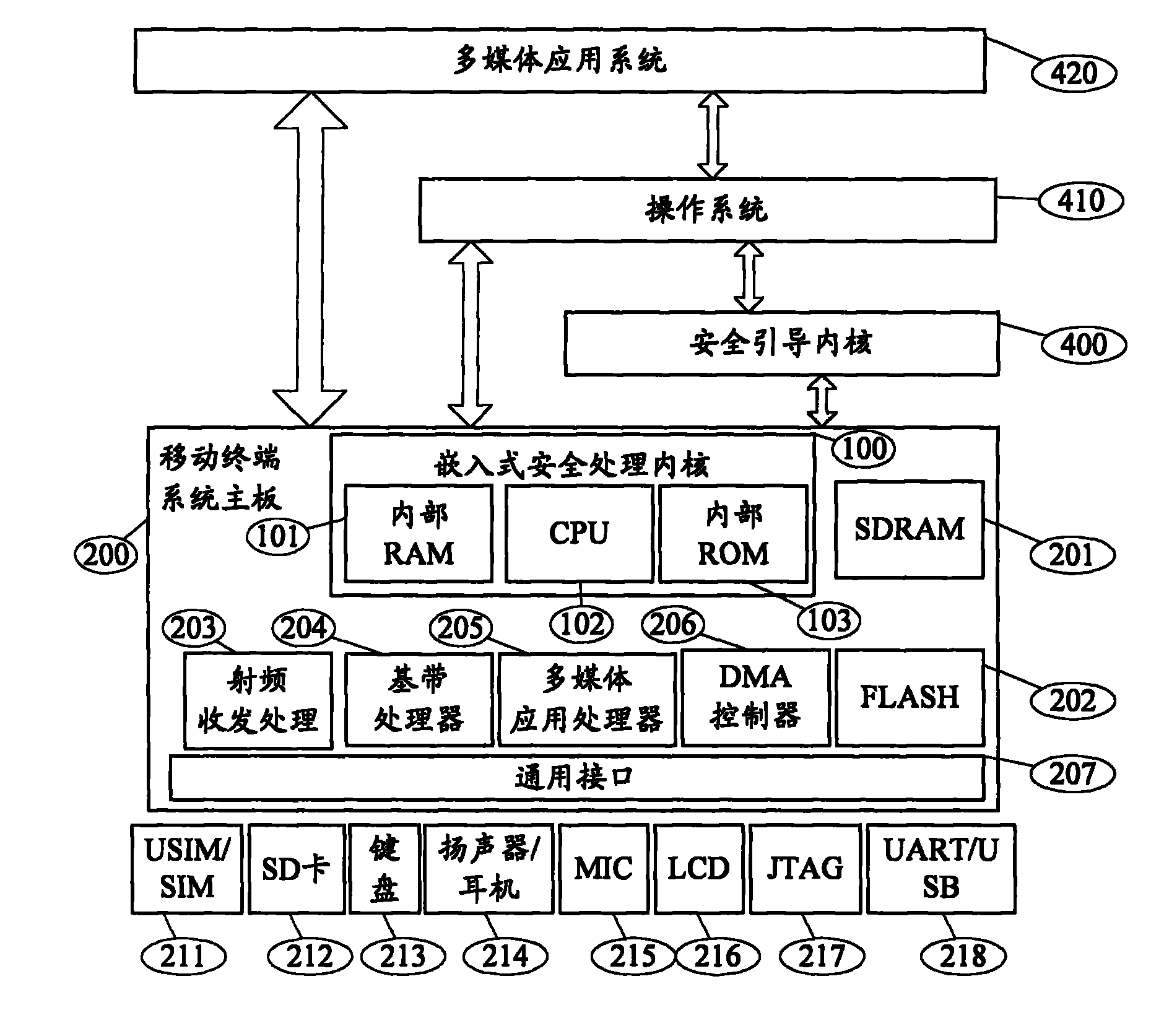
[0038] Such as figure 1 As shown, the secure boot system of the mobile terminal according to the first embodiment of the present invention mainly includes: a secure processing kernel (preferably, may be an embedded secure processing kernel) 100, including a CPU 102, a RAM 101, and a ROM (internal flash) 103, used to establish a secure boot program, and complete the authentication process to the operating system software image file or the application system software image file based on elliptic curve cryptography; the secure operating system 410 is connected to the secure processing kernel, including the multimedia application processor 205 , a baseband processor 204, and an external interface device common interface 207, configured to execute a hardware initialization function.
[0039]In addition, the security guidance system at least includes: a radio frequency signal transceiving module, a baseband signal processing module, a multimedia processor, a terminal flash memory 20...
no. 2 example
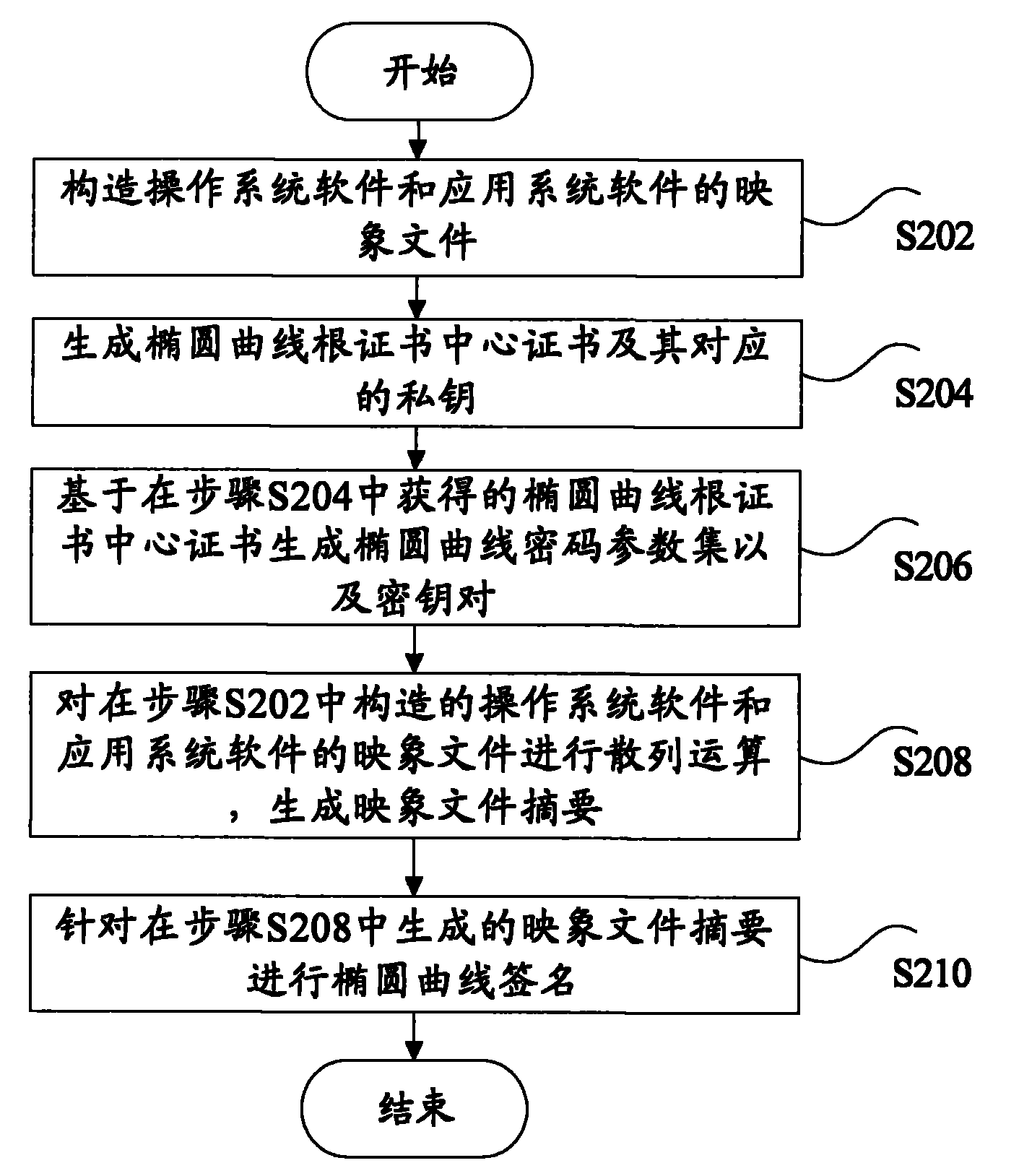
[0047] According to the second embodiment of the present invention, based on the secure boot system of the mobile terminal in the first embodiment, a code signature construction method is provided.
[0048] Such as figure 2 As shown, the method includes the following steps: Step S202, constructing the image file of the operating system software and the application system software; Step S204, generating the elliptic curve root certificate center certificate and its corresponding private key; Step S206, based on the The obtained elliptic curve root certificate center certificate generates an elliptic curve cryptographic parameter set and a key pair; step S208, hashing the image files of the operating system software and application system software constructed in step S202 to generate an image file summary ; and step S210, performing an elliptic curve signature on the image file digest generated in step S208.
[0049] Wherein, in step S208, a hash function is used for hash oper...
no. 3 example
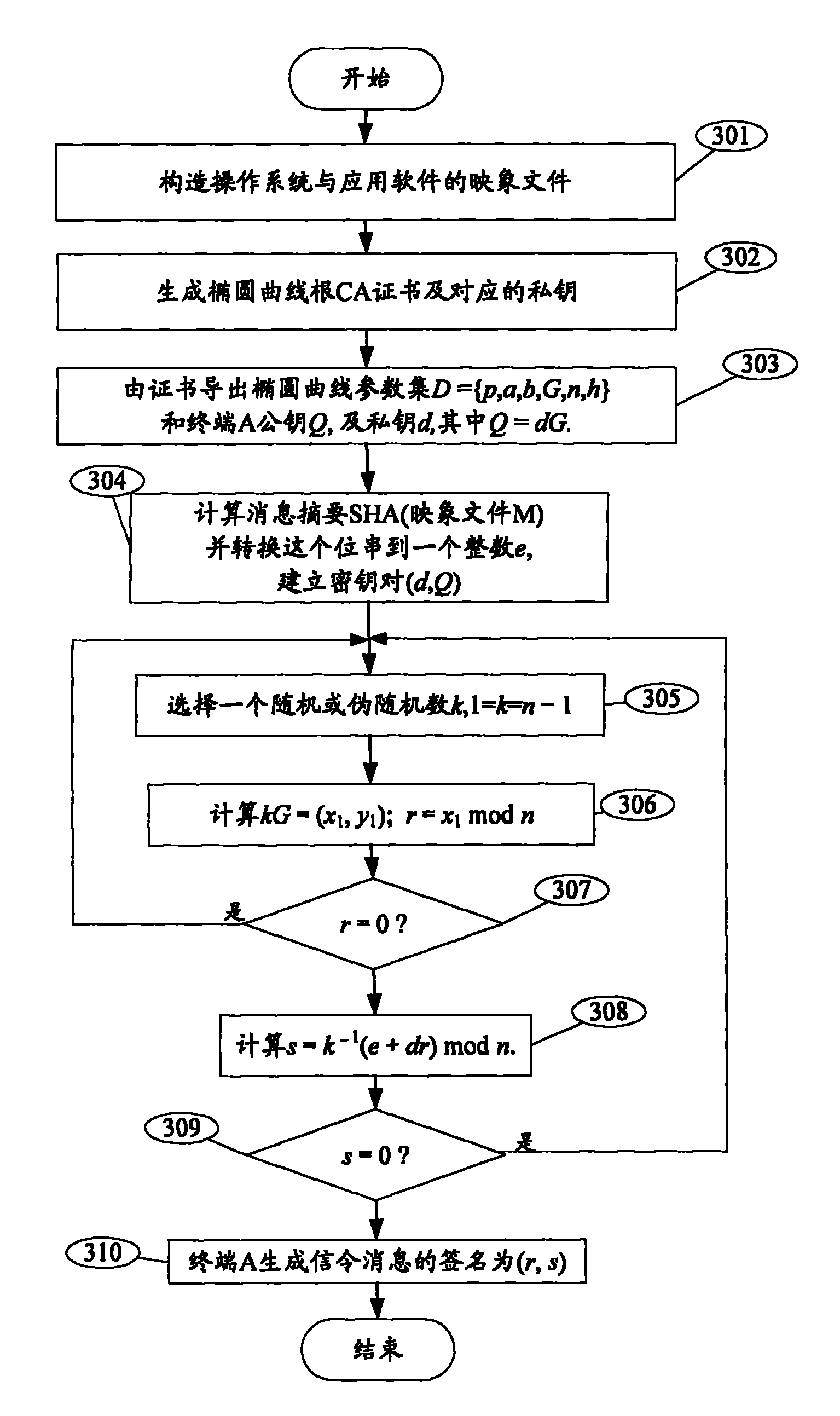
[0062] According to the third embodiment of the present invention, based on the secure boot system of the first embodiment, a code signature authentication method is provided.
[0063] Such as Figure 4 As shown, the method includes the following steps: Step S402, the security processing kernel boot program obtains a public elliptic curve parameter set and related public keys based on the elliptic curve root certificate authority certificate; Step S404, the security processing kernel boot program verifies the signature of the image file Whether exceed the scope of elliptic curve base point group order; Wherein, under the situation that verification result is no, proceed to step S406; Step S406, generate the message summary of image file; Step S408, calculate respectively w=s-1 mod n, u1=ew mod n, u2=rw modn, and X=u1G+u2Q=values of (x1, y1); step S410, verify the code signature according to the value of the abscissa of X calculated in step S408.
[0064] Wherein, in step S4...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap