Method and apparatus for preventing network intermedium from accessing into control address
A medium access control and address configuration technology, applied in the field of network communication, can solve the problems of lack of flexibility and scalability, MAC address spoofing security, and inability to realize automatic MAC address configuration.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025] In order to make the purpose, technical solutions and advantages of the present invention clearer, the preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit this invention.
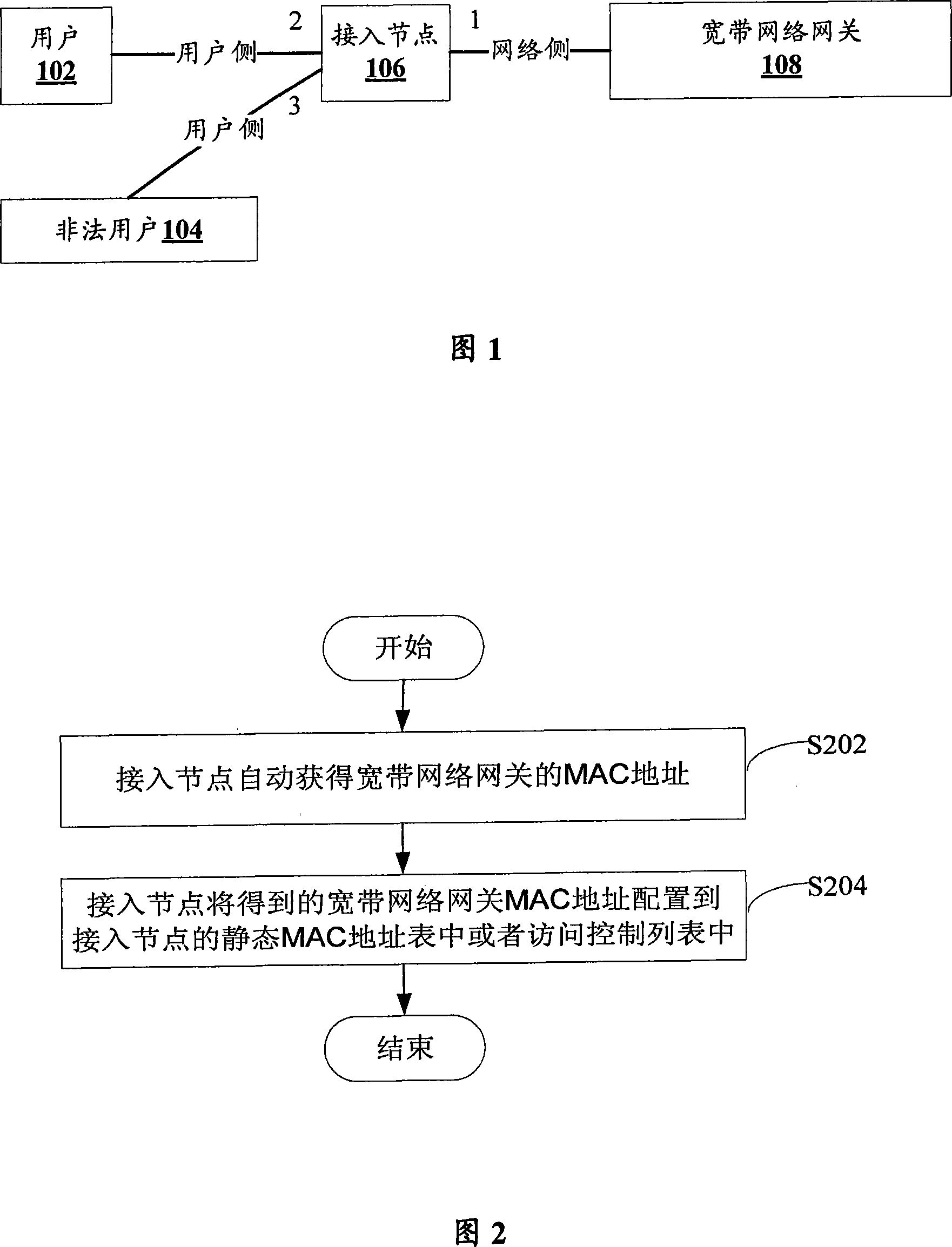
[0026] Fig. 1 is a network structure diagram according to an embodiment of the present invention.
[0027] As shown in FIG. 1 , the network is composed of users 102 , illegal users 104 , access nodes 106 , and broadband network gateways 108 . Among them, the user 102 is connected to the access node 106 through the user-side link 2 of the access node 106, the illegal user 104 is connected to the access node 106 through the user-side link 3 of the access node 106, and the access node 106 is connected to the access node 106 through the network side Link 1 is connected to broadb...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More