Method, device and system for recognizing abuse of emergency bearing resource in IMS
An emergency bearer and resource technology, applied in the field of identifying the abuse of emergency bearer resources, can solve problems such as the abuse of emergency bearer resources, and achieve the effect of avoiding abuse
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0044] The preferred embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings.
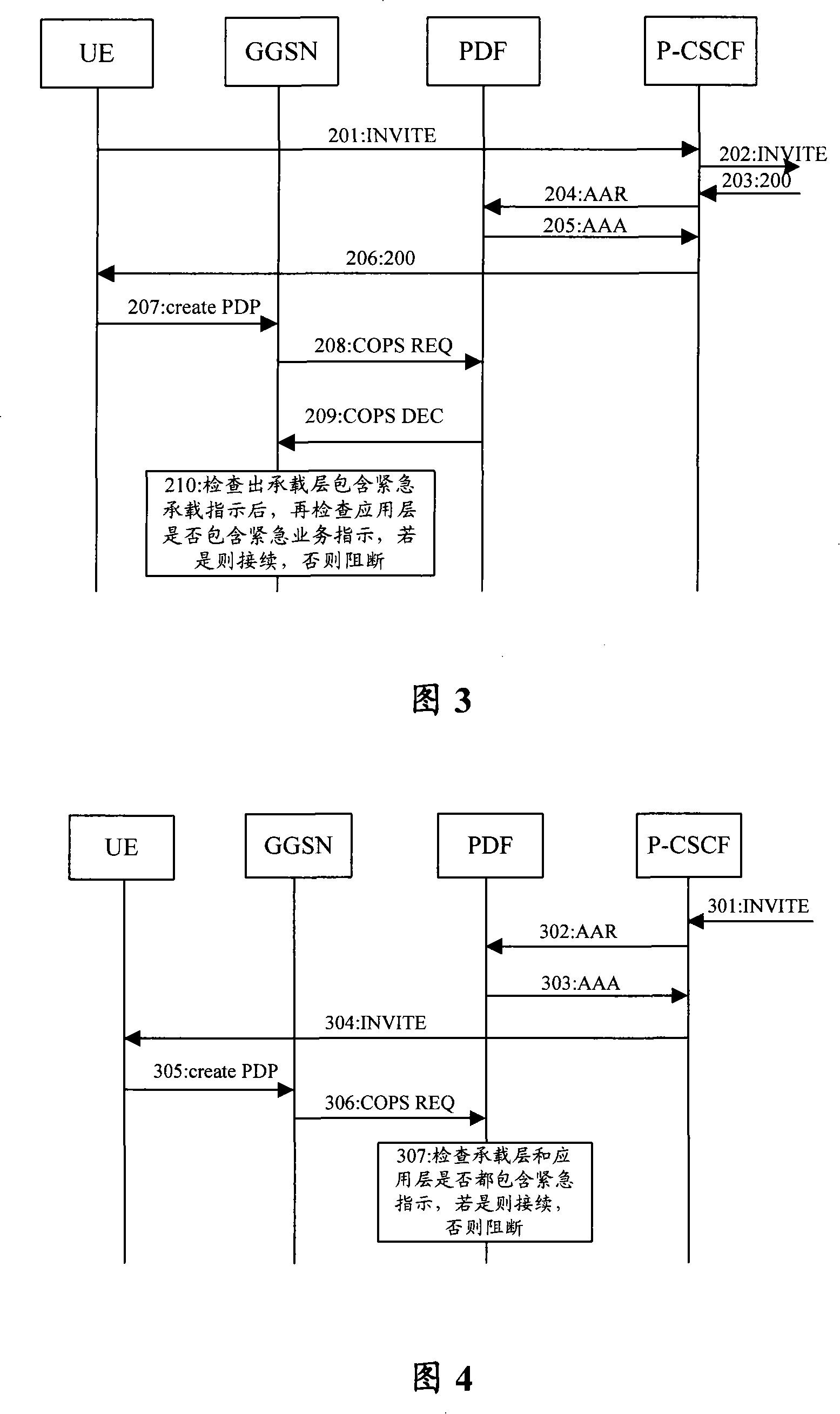
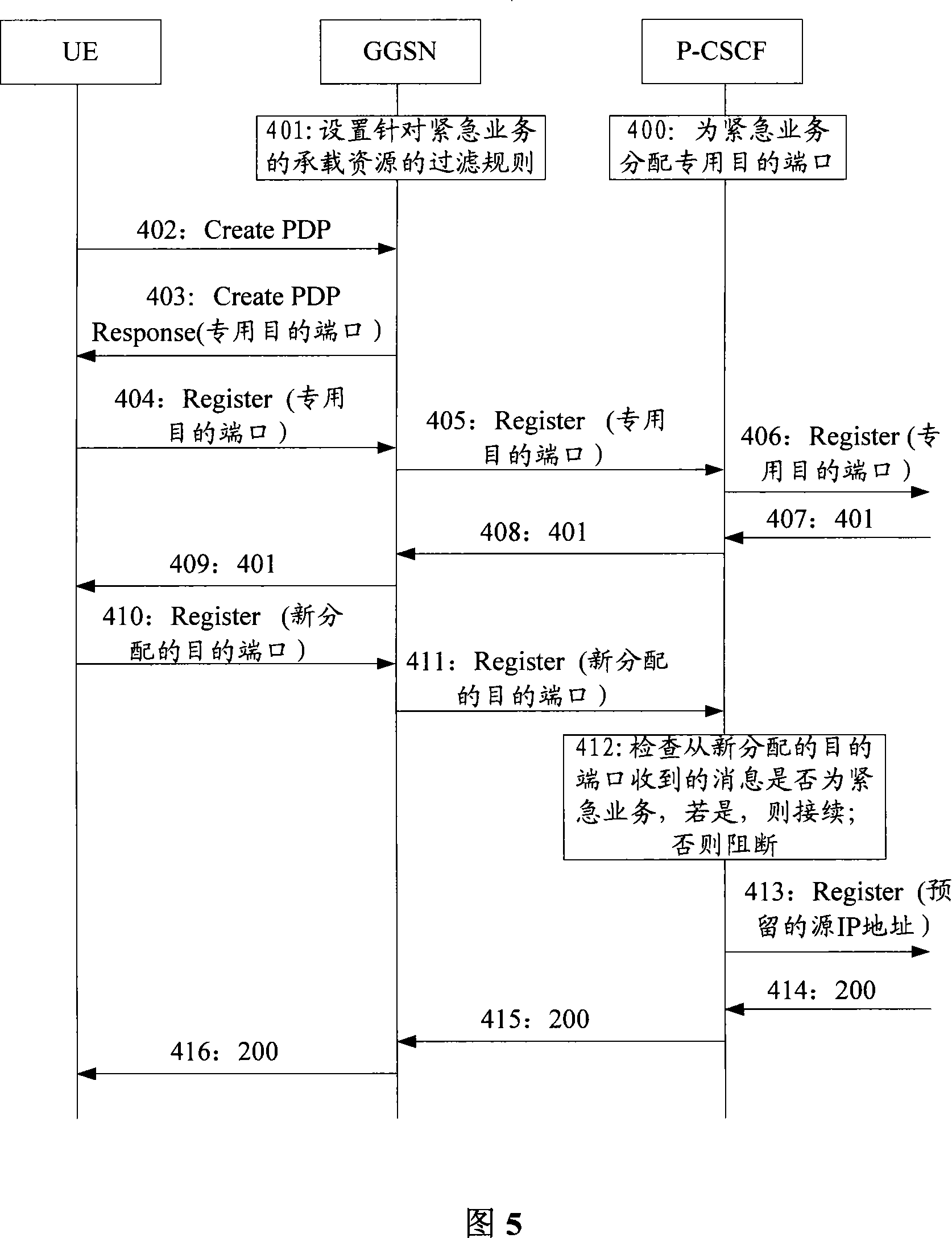
[0045] In the embodiment of the present invention, in the same service-related request, the intermediate entity used to transfer information obtains the emergency attribute information of the bearer layer and the application layer. If the bearer layer uses emergency bearer, it will check whether the application layer is an emergency service. If the service is not urgent, it is determined that the request abuses the emergency bearer resource. The emergency attribute information includes: bearer emergency indication and service emergency indication.
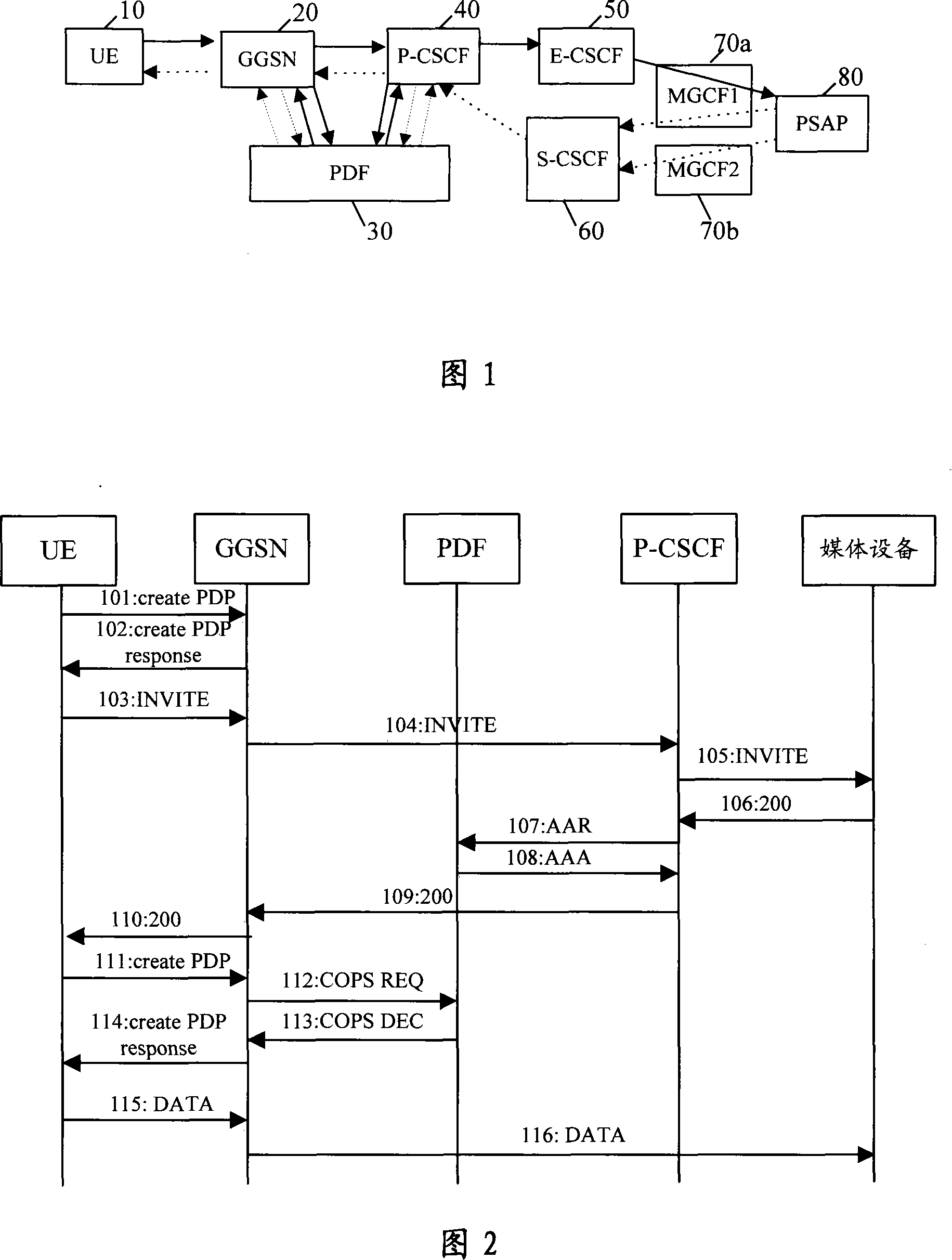
[0046] The above-mentioned intermediate entity for transferring information may be a bearer control IP gateway on the access side, such as GGSN, Packet Data Serving Node (PDSN), etc., or PDF or application server, etc., of course, it is not limited thereto. Moreover, the emergency ser...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com