Wireless multi-hop network authentication access method based on ID
A wireless multi-hop network and access method technology, which is applied in the field of ID-based wireless multi-hop network authentication access, and can solve problems such as security risks of authentication access methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
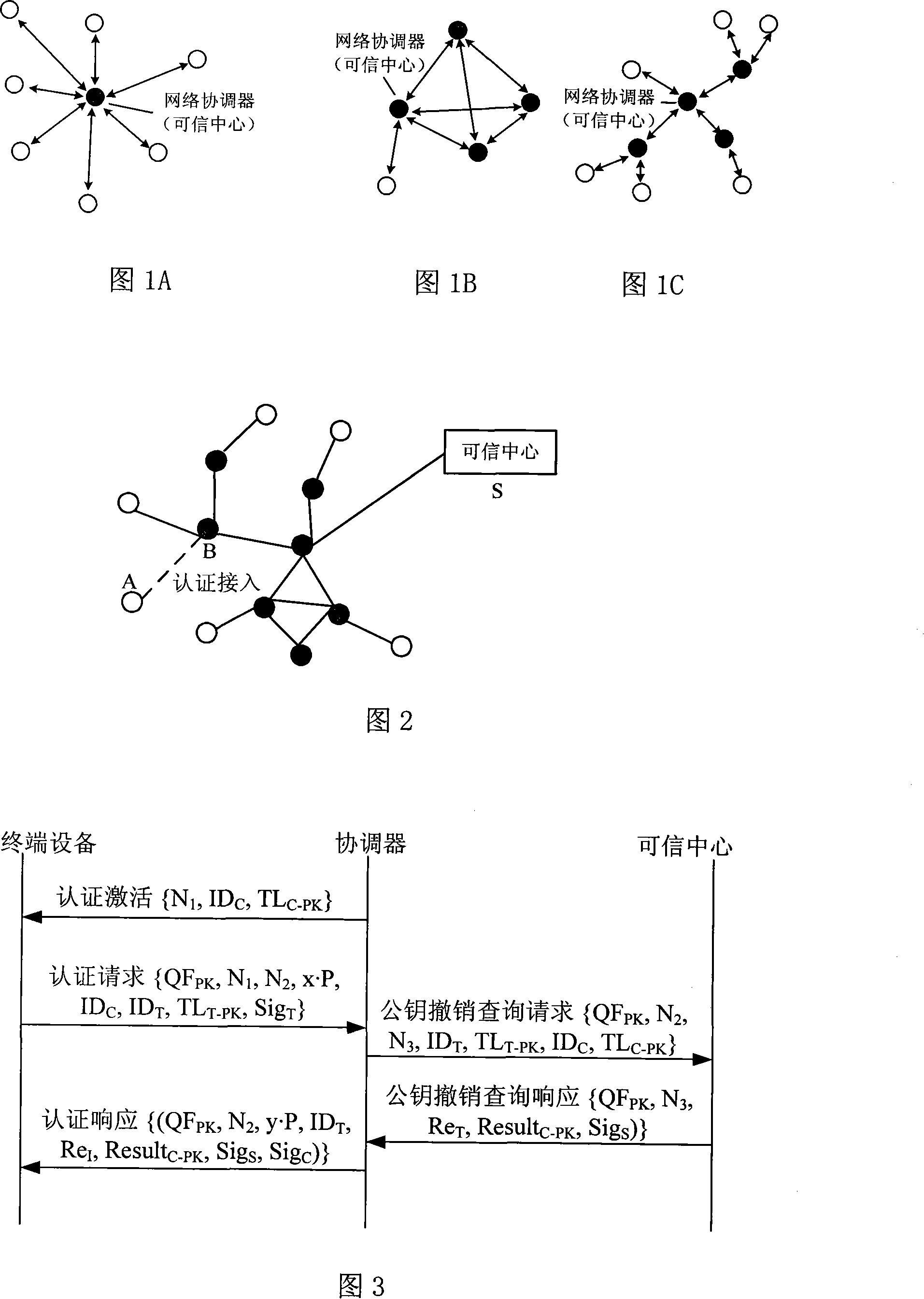
[0106] The invention is applicable to the security application protocol when the WAPI framework method (TePA, an access control method based on ternary peer-to-peer authentication) is applied on specific networks including wireless local area networks and wireless metropolitan area networks.
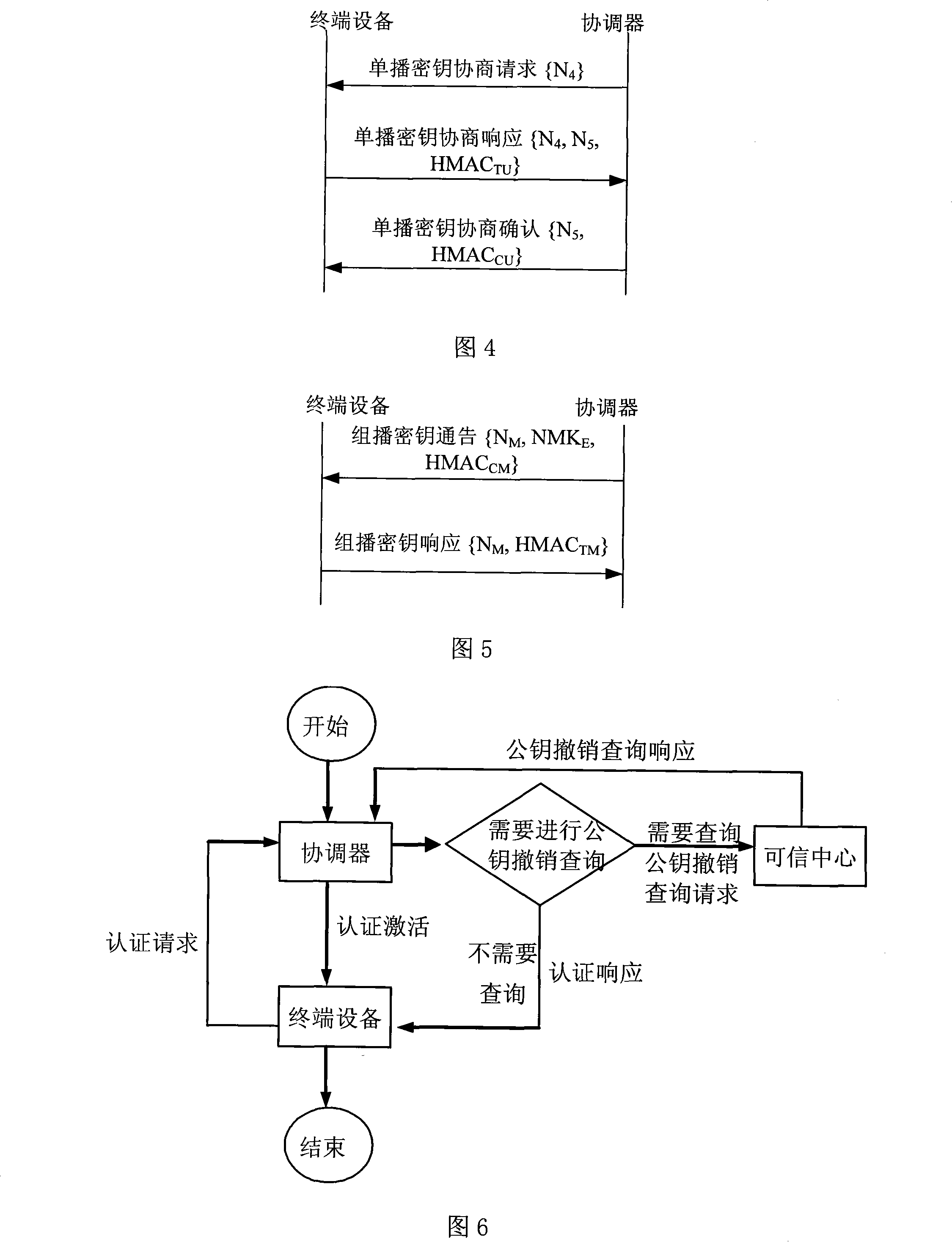
[0107] In the authentication access system of the wireless multi-hop network, the purpose of authentication is to establish trust between the terminal device and its associated coordinator, and to protect the data transmitted on the link between them. The terminal device and its associated coordinator belong to the same management domain, that is, a wireless multi-hop network, and the trusted center of the wireless multi-hop network needs to configure all devices in the wireless multi-hop network, such as: Configure key information under different authentication and key management suites.
[0108] In the authentication access system of the wireless multi-hop network, the coordinator broa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More