End-to-end speech ciphering method, apparatus and system
A voice encryption and voice stream technology, applied in transmission systems, selection devices, electrical components, etc., can solve the problem that the voice stream of the mobile terminal is not encrypted, and achieve the effect of being easy to implement, simple to implement, and ensuring communication security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
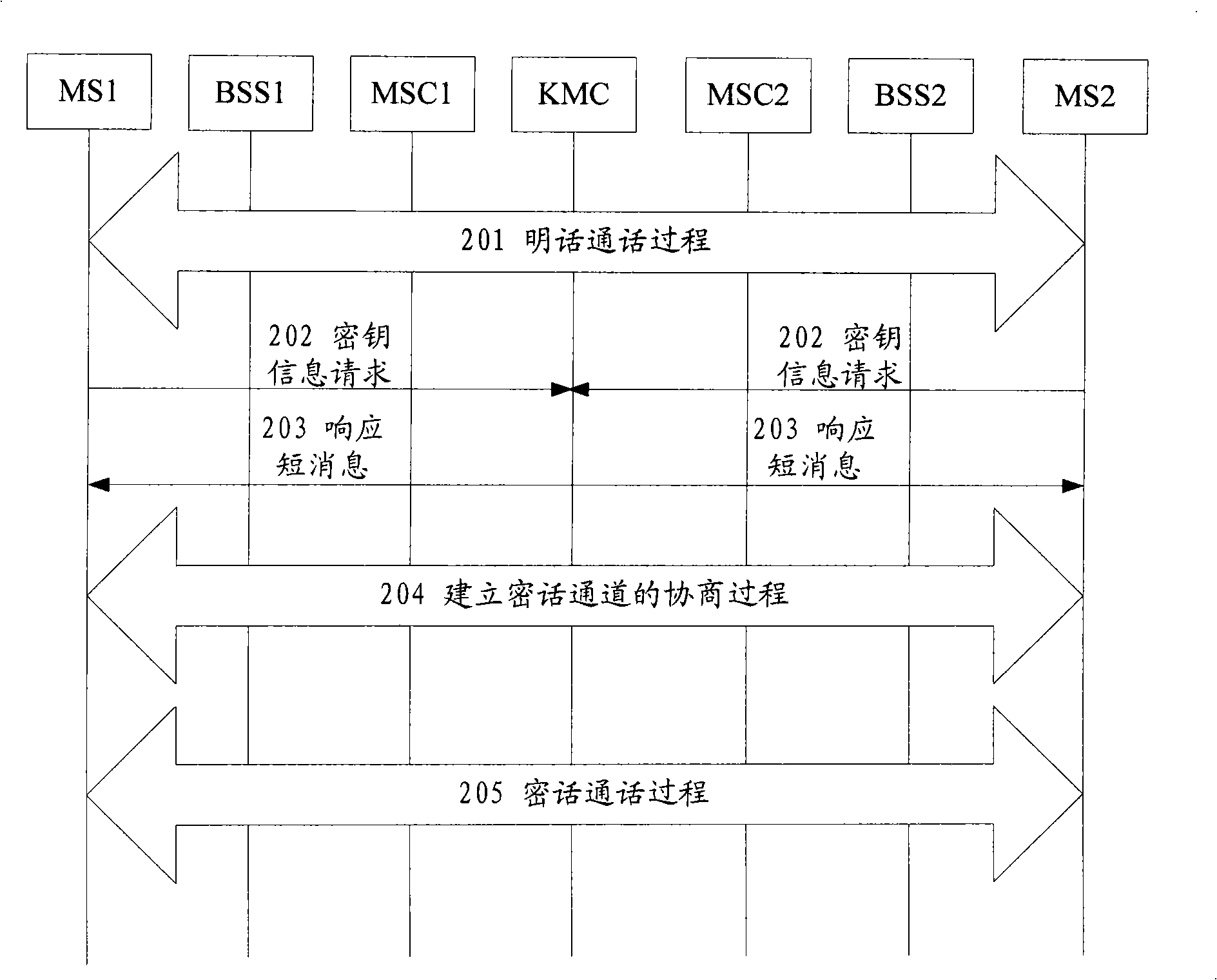
[0035] The technical solutions of the present invention will be described in further detail below with reference to the accompanying drawings and embodiments.
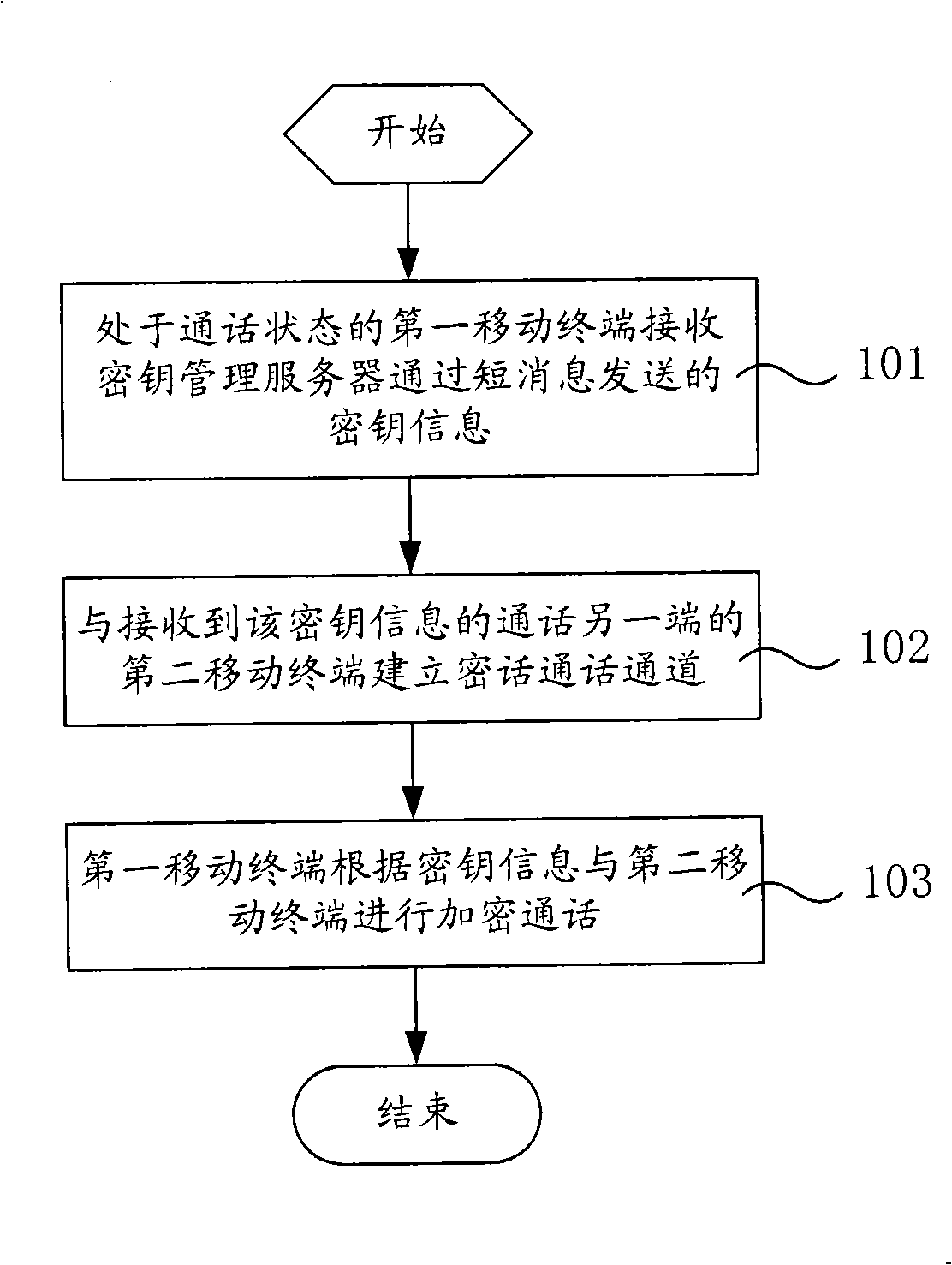
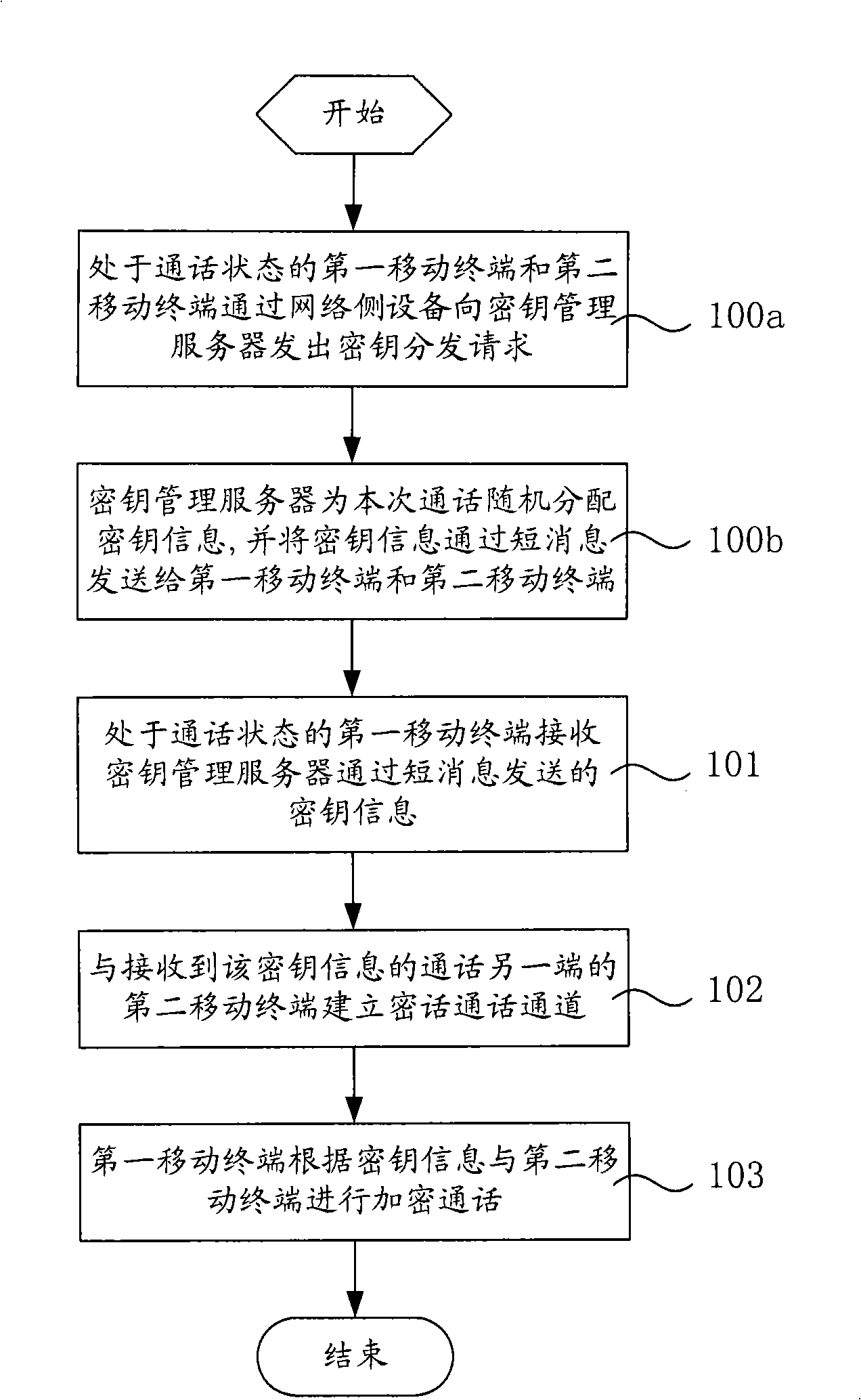
[0036] Such as figure 1 As shown, it is a schematic flow chart of an embodiment of the end-to-end voice encryption method of the present invention. In this embodiment, the end-to-end voice encryption process includes the following steps:
[0037] Step 101, the first mobile terminal in the call state receives the key information sent by the KMC through a short message;
[0038] Step 102, the first mobile terminal establishes an encrypted conversation channel with the second mobile terminal at the other end of the conversation that has received the key information;
[0039] Step 103, after establishing an encrypted conversation channel, the first mobile terminal conducts an encrypted conversation with the second mobile terminal according to the key information.
[0040] The existing voice encryption and decryption mod...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More