Multi-stage authentication method and multi-stage authentication system
A multi-level authentication and access credential technology, applied in the field of network security, can solve problems such as impersonation login, failure to log in, efficiency and stability reduction, etc., and achieve the effect of improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
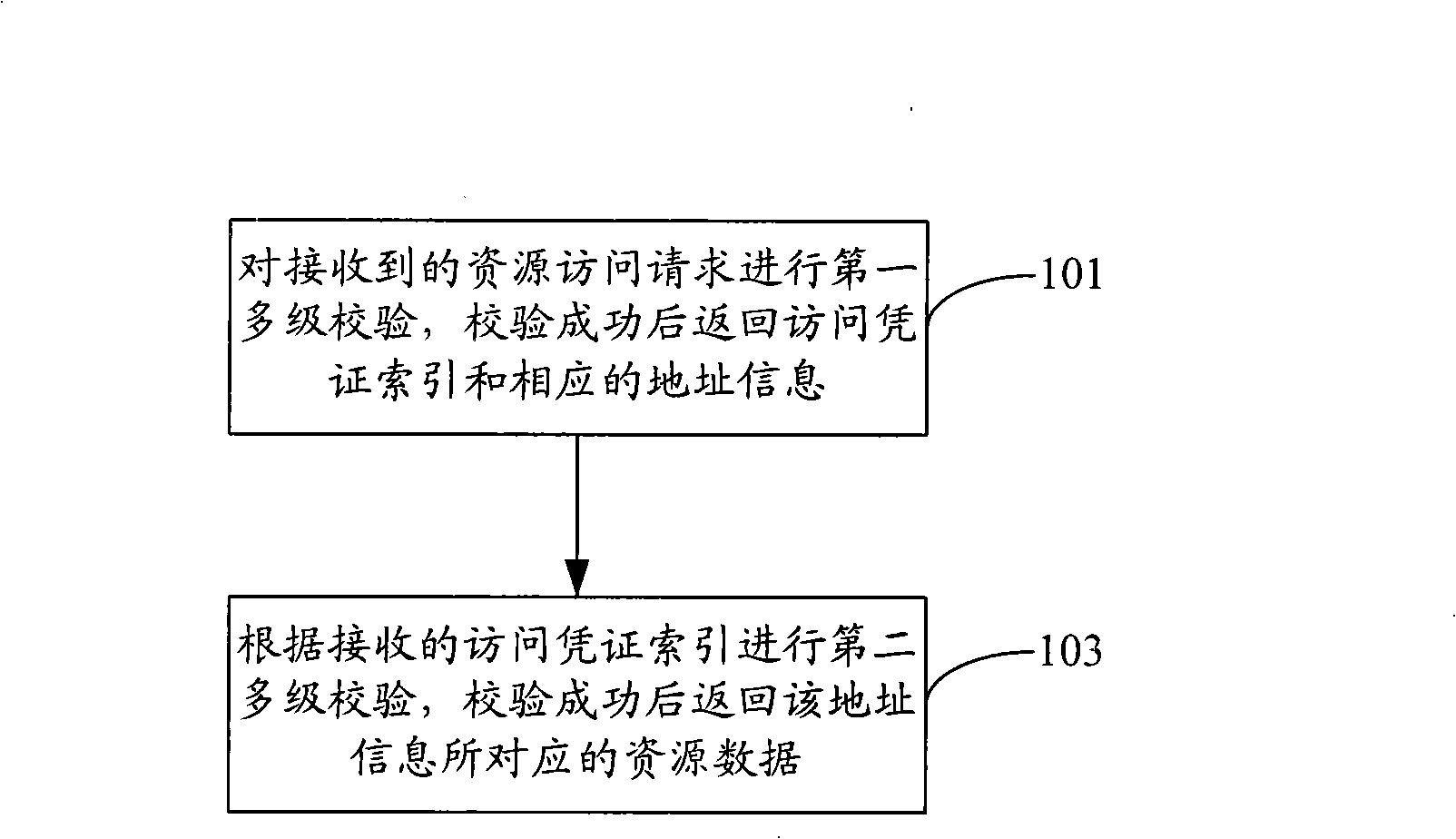
[0020] figure 1 It is a flow chart of the first embodiment of the multi-level authentication method of the present invention. Such as figure 1 As shown, the method includes:
[0021] Step 101, perform a first multi-level verification on the received resource access request, and return the access credential index and corresponding address information after the verification is successful;
[0022] This multi-level verification is to verify the legal identity of the user corresponding to the user login information carried in the resource access request, that is, to determine whether the user has successfully logged in, and the verification process is a step-by-step verification. The verification process may be as follows: the login authentication server performs the first multi-level verification on the received resource access request. No successful login; if the verification is successful, it means that the user has successfully logged in, and the access credential index and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More