Authentication method, reader and label
An authentication method and reader technology, applied in the fields of authentication methods, readers and labels, can solve the problems of poor forward security and achieve the effect of ensuring forward security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
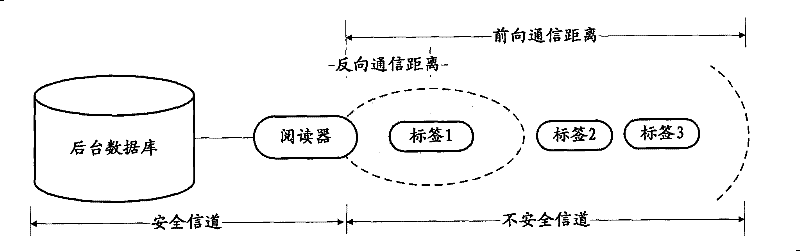
[0049] The technical solutions of the embodiments of the present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
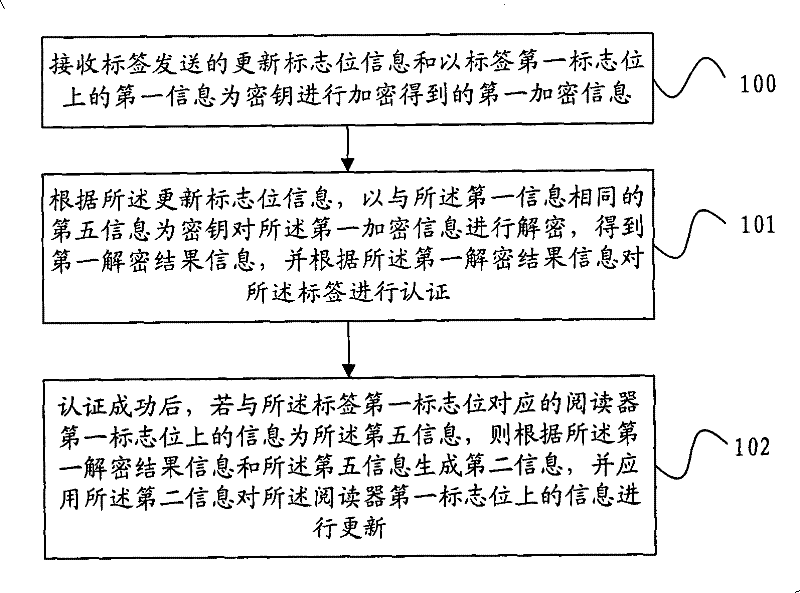
[0050] figure 2 It is a flowchart of an authentication method embodiment of the present invention, such as figure 2 As shown, the method includes:
[0051] Step 100, receiving the updated flag bit information sent by the tag and the first encrypted information obtained by encrypting the first information on the first flag bit of the tag as a key;
[0052]In the process of authenticating a tag, the reader needs to receive the authentication information sent by the tag. The authentication information includes the update flag information of the tag and the first encrypted information. The first encrypted information is the authentication information sent by the tag to the reader. Before the information, firstly receive the reader random number sent by the reader, and then the tag itself generates a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More