Information protection method for unconnected system
A technology of encryption system and manager, applied in key distribution, which can solve problems such as difficulty in ensuring system reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
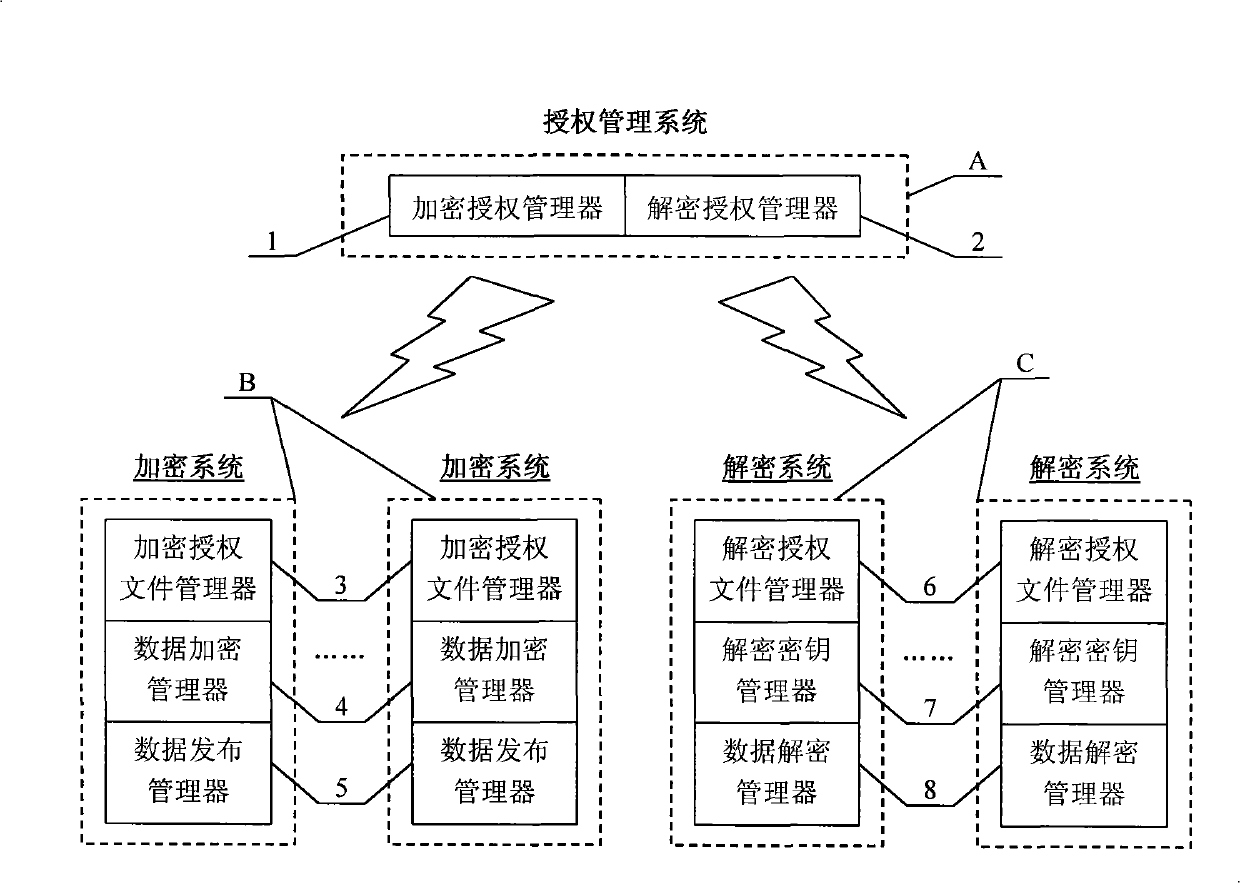
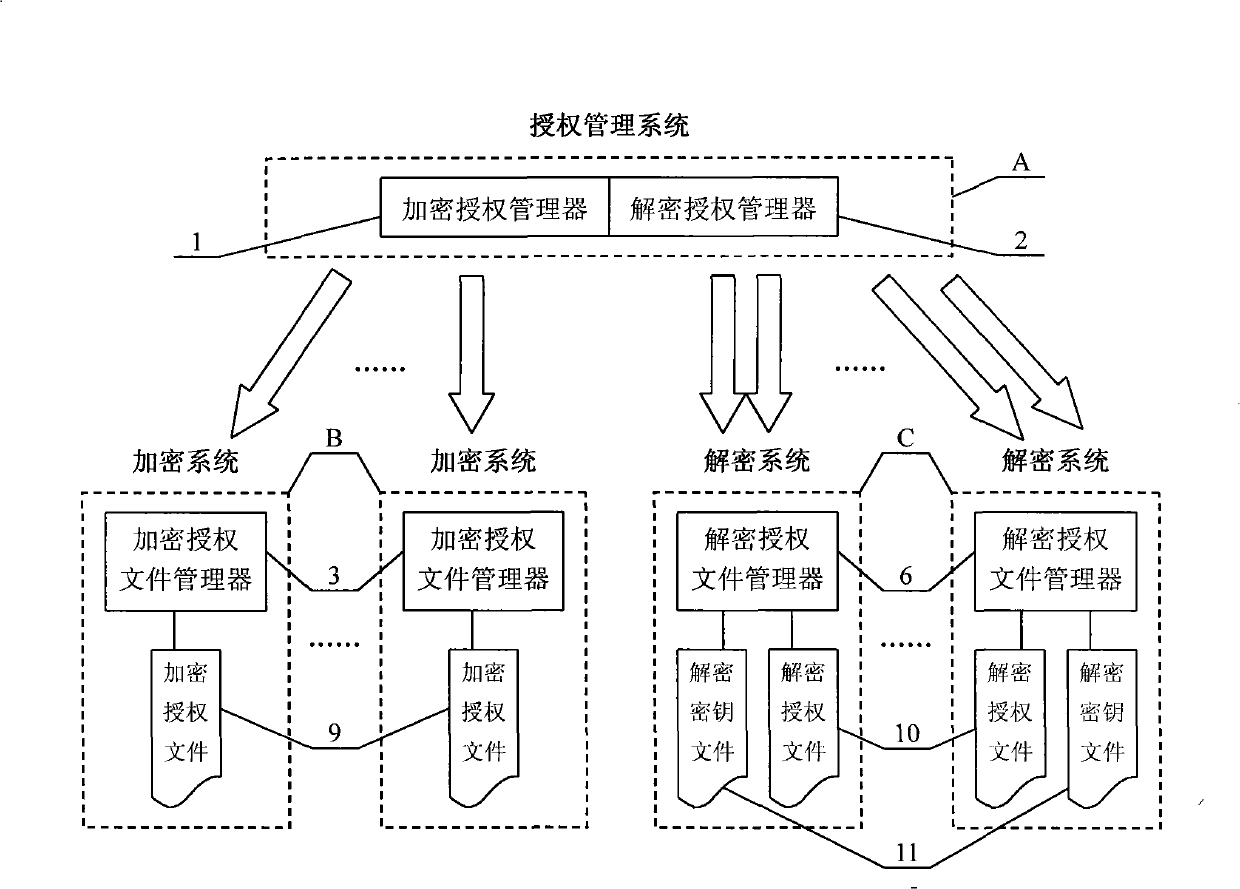
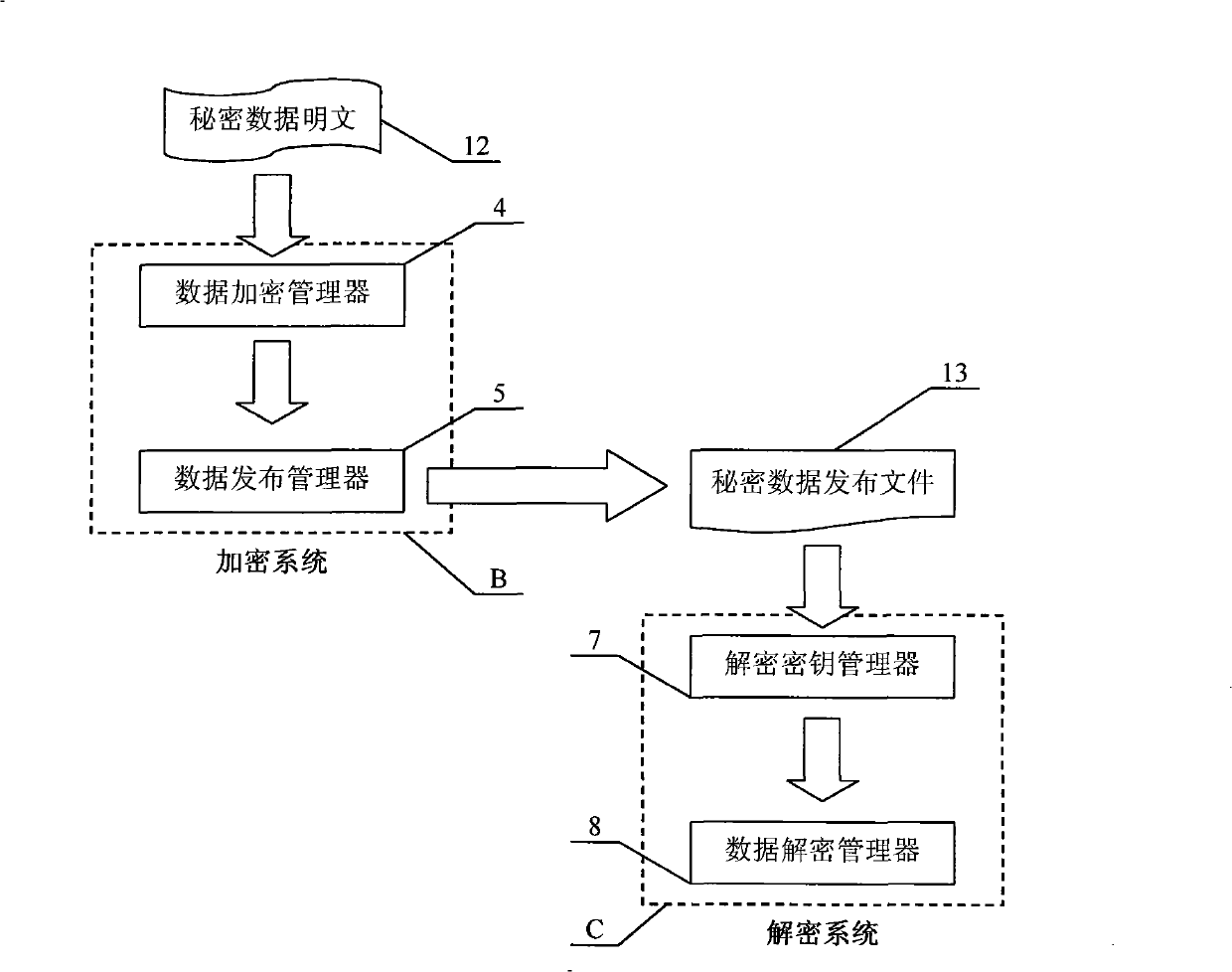
[0025] see figure 1 , the device applying the method of the present invention is composed of an authorization management system A, a plurality of encryption systems B and a plurality of decryption systems C which are not connected to each other. Authorization management system A is composed of encryption authorization manager 1 and decryption authorization manager 2; encryption system B is composed of encryption authorization file manager 3, data encryption manager 4 and data release manager 5; decryption system C is managed by decryption authorization file Device 6, decryption key manager 7 and data decryption manager 8. Authorization management system A performs authorization management on encryption system B and decryption system C, encryption system B encrypts and publishes secret data, and decryption system C decrypts and utilizes secret data.
[0026] see figure 2 and image 3 , the steps of the information protection method of the present invention are:
[0027] 1)...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More