Method and device for protecting class files
A technology for protecting devices and files, applied in digital data protection, computer security devices, instruments, etc., to achieve the effect of easy to use, maintain cross-platform characteristics, and prevent decompilation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
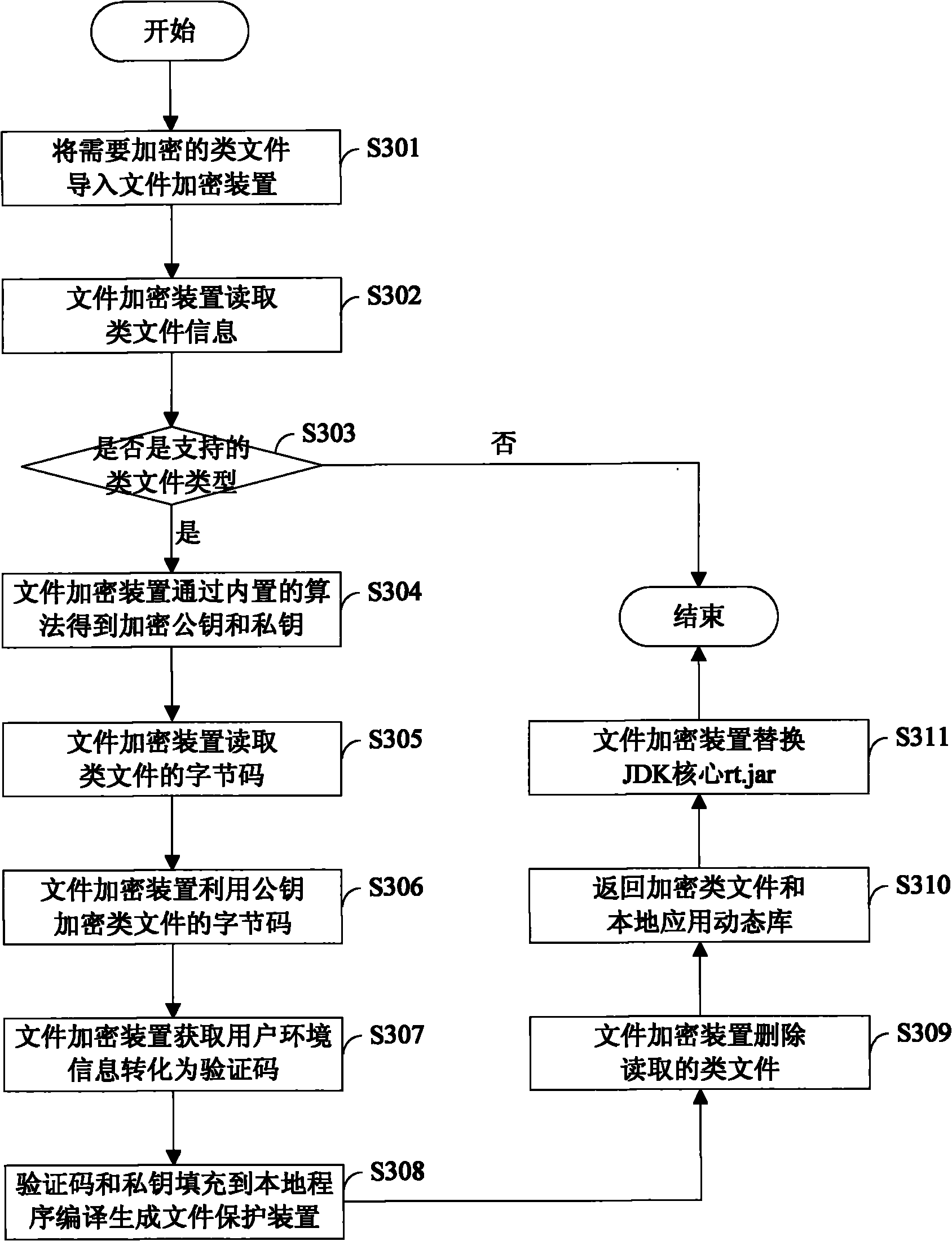
[0022] The preferred embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described below are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
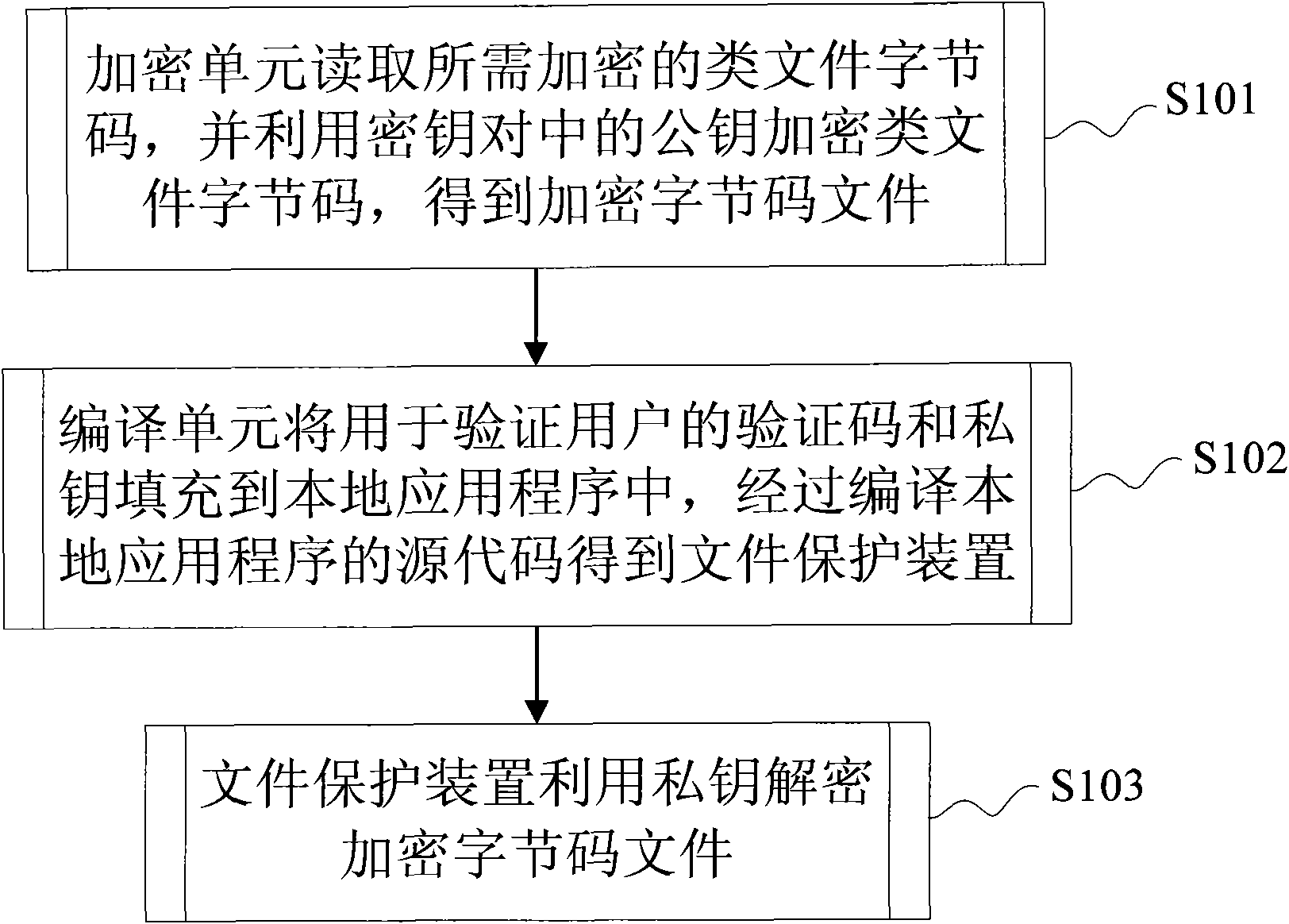
[0023] figure 1 Shows the method flow of the protection file provided by the present invention, such as figure 1 Shown:
[0024] Step S101, the encryption unit reads the bytecode of the class file to be encrypted, and uses the public key in the key pair to encrypt the bytecode of the class file to obtain the encrypted bytecode file.
[0025] Prior to this, it is necessary to judge the file type of the imported class file. If the file type is not supported, the encryption operation will be terminated. If the file type is supported, the key generation unit will obtain the key pair through the built-in algorithm. The key A pair includes a public key for en...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More