File encryption method based on TCM (trusted cryptography module) and USBkey
A password module and file encryption technology, applied in the field of information security, can solve the problems of unfavorable file sharing, easy forgetting of user passwords, low efficiency, etc., and achieve the effect of improving encryption and decryption efficiency, flexibility, and security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
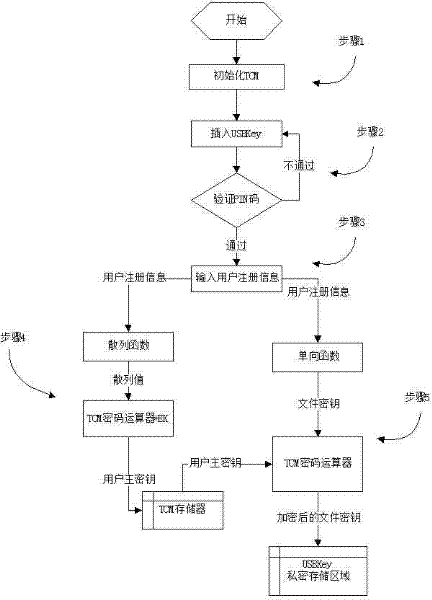
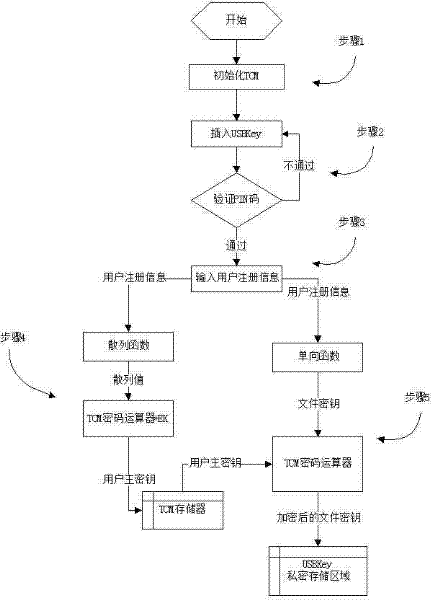
[0029] figure 1 The implementation method flow of the initialization module is given, as shown in the figure, the initialization implementation steps are as follows:
[0030] Step 1 The initialization module first activates and initializes the environment and owner of the TCM trusted cryptographic module. After initialization, the root key and platform environment in the TCM trusted cryptographic module are available.
[0031] Step 2 After the initial configuration of the TCM trusted cryptographic module is completed, insert the user's USBKey, enter the PIN code and pass the verification, then continue the initialization, otherwise return to continue the verification.
[0032] Step 3 The USBKey initialization unit pops up the user initialization interface, and enters the user registration information;
[0033] Step 4 Use the hash function in the USBKey to map the user registration information of the user's USBKey to a hash value, and pass the hash value to the TCM trusted pas...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More