User identity authentication method and system
A user identity authentication and user identity technology, applied in the direction of user identity/authority verification, etc., can solve the problems of network equipment user maintenance difficulties, increase production costs, information security threats, etc., to reduce maintenance difficulties and cumbersomeness, and achieve centralized management. , the effect of enhancing flexibility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] In order to make the technical problems, technical solutions and beneficial effects to be solved by the present invention clearer and clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
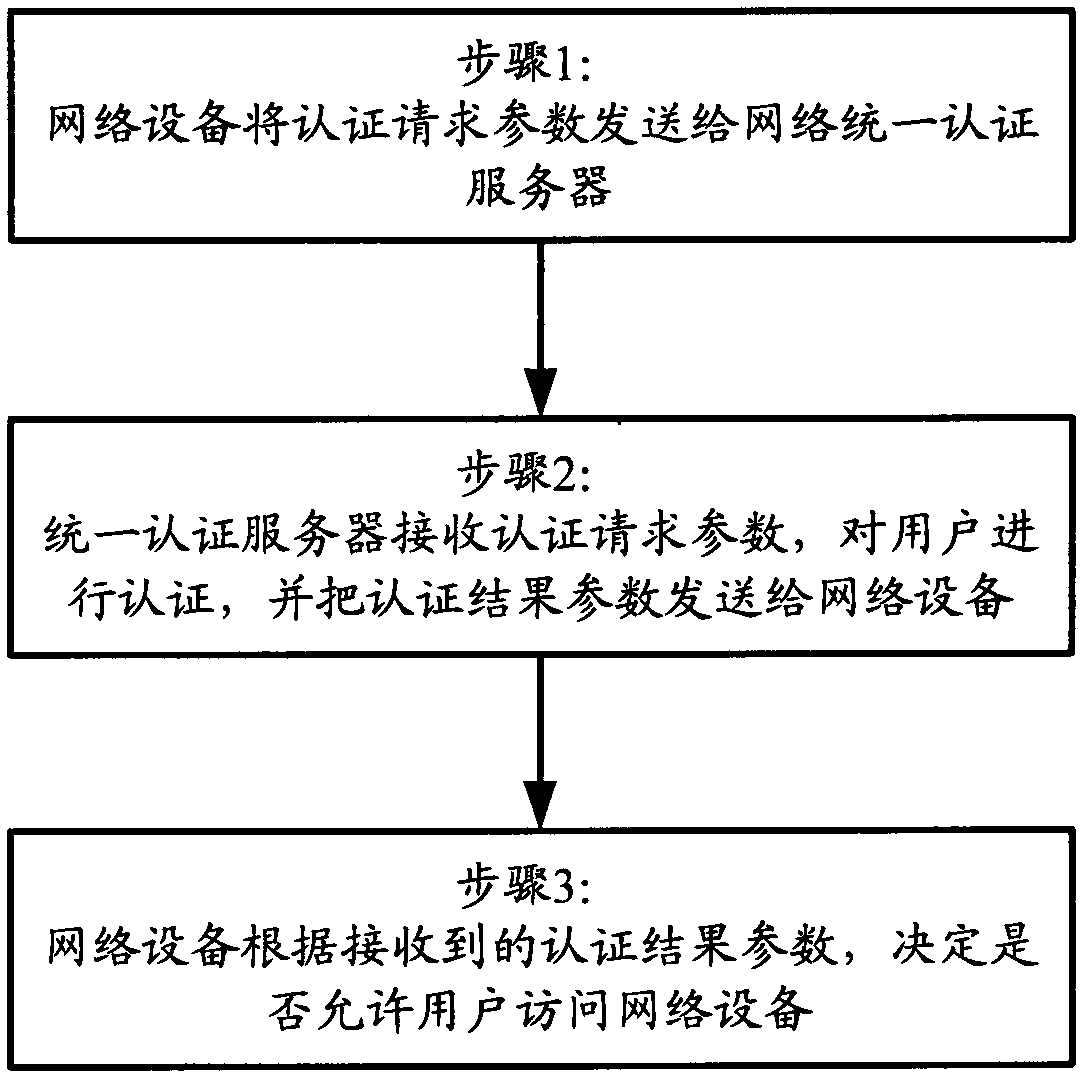
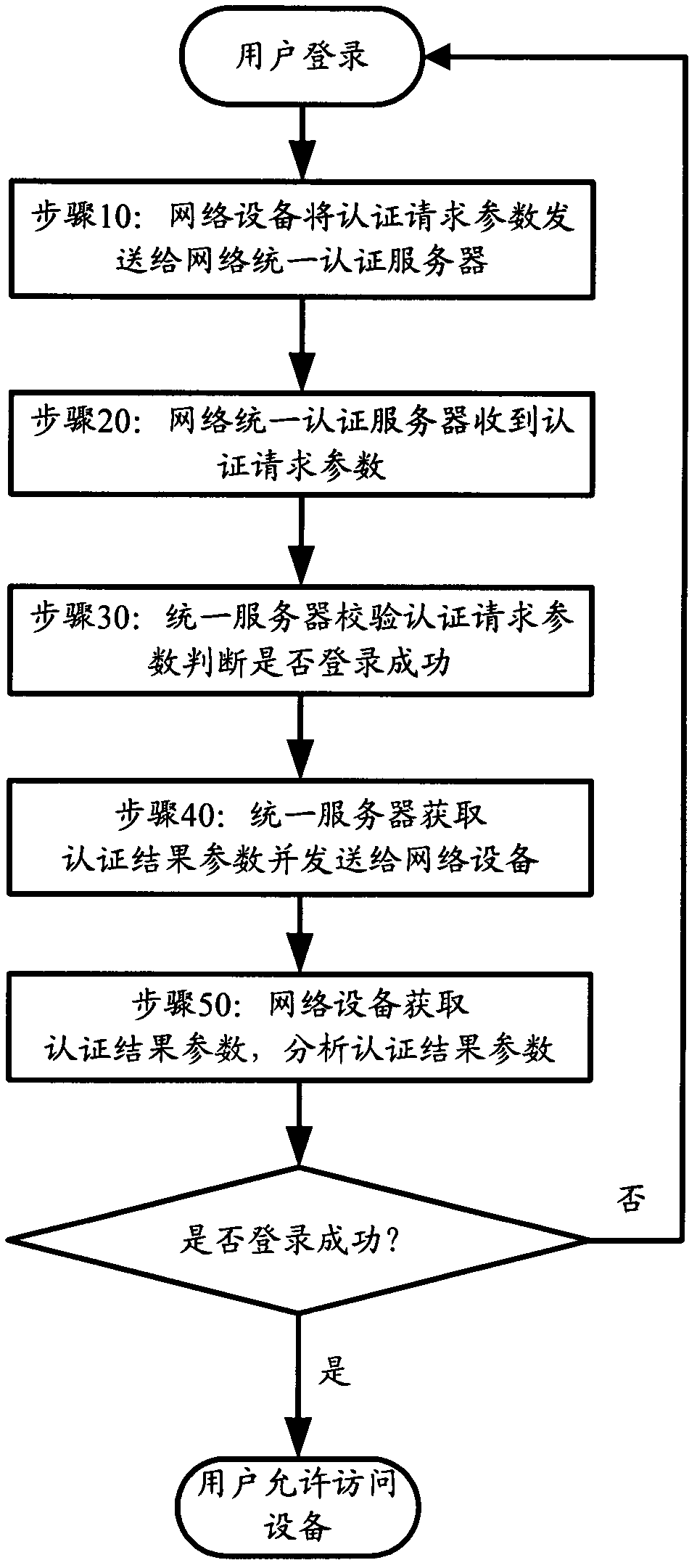
[0035] The invention provides a user identity authentication method, which uniformly stores and records user identity authentication parameters such as user name and password in a unified authentication server, and uniformly authenticates the user's legitimacy when the user logs in to a network device. The method includes:
[0036] Step 1. When the user accesses the network device, the network device sends the authentication request parameters to the unified authentication server; specifically includes:
[0037] Step 1.1, the network device receives au...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More