Network information interaction method and network security system
An interactive method and network information technology, applied in the field of computer security protection, can solve the problems of catastrophe, data not carefully and effectively screened, and incoming unsafe data, etc., and achieve the effect of easy identification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
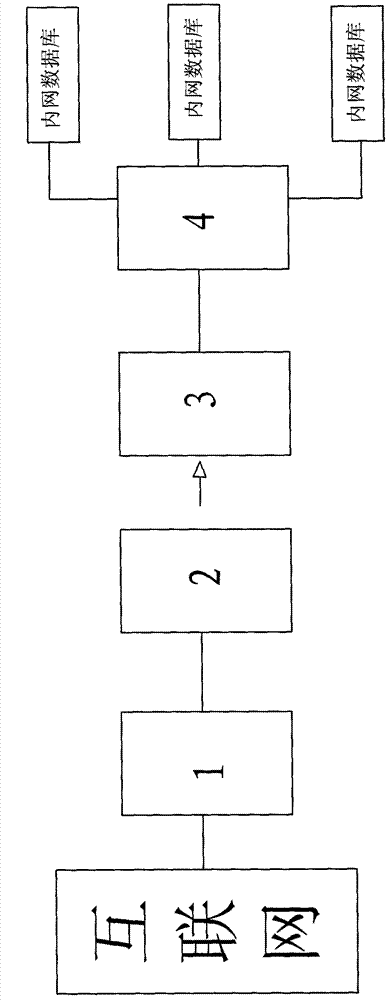
[0018] A network information interaction method, comprising the following steps:
[0019] Firstly, build an external network heterogeneous data collaborative server, the external network data heterogeneous system includes a heterogeneous data collaborative server and a display, and the heterogeneous data collaborative server restores external network data displayed in different forms into information in XML format, Then integrate and unify the processing, and translate the information in XML format into Unicode code;
[0020] Secondly, build the intranet identification control system, the intranet identification control system includes a photography or camera device and a data identification control server, and the photography or camera device is used to convert the data displayed on the display screen into an image file, so The data identification control server adopts OCR identification technology to restore the image file to XML information;
[0021] Third, the heterogeneo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More