A broadcast authentication method for wireless sensor networks based on ecdsa algorithm
A wireless sensor and sensor network technology, which is applied in the field of communication technology and information security, can solve the problem of large amount of calculation, etc., and achieve the effect of less memory usage, good real-time performance, and reduced memory usage
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0044] The concrete steps of a kind of wireless sensor network broadcast authentication method based on ECDSA algorithm of the present invention are as follows:
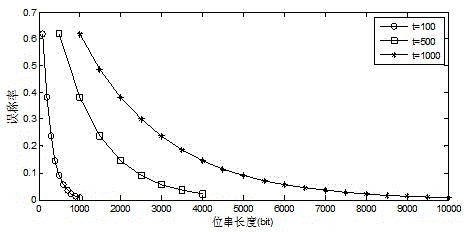
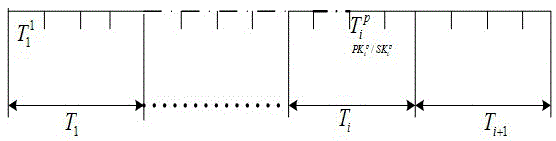
[0045] 1. Divide the lifetime T of the sensor network into t time periods T i (1≤i≤t), each time period T i For several minutes or several hours, for security authentication within several hours or several minutes, here we choose the key length of ECDSA as 80 bits.
[0046] 2. Generate a parameter set for the ECDSA algorithm. The generation algorithm of the parameter set is as follows:
[0047] 1). Input: the order of the domain is q, F q The domain of represents FR, and the security level L meets the requirements;
[0048] 2). Output: parameter group 2;
[0049] 3). If F q Is prime field, binary field or OEF, randomly select a, b∈F q , let S be the generated seed, if F q is prime field or OEF then let E be y 2 =x 3 +ax+b; if F q is a binary field, then y 2 +xy=x 3 +ax 2 +b
[0050] 4). Calculate N=#E(F...
Embodiment 2
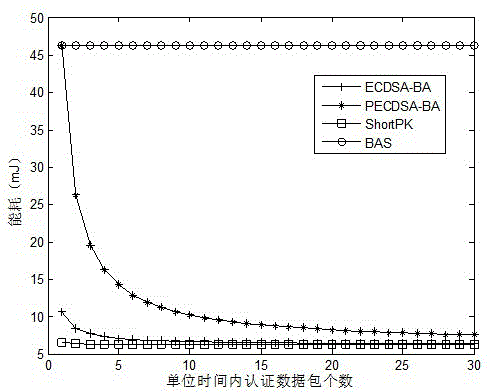
[0101] In the ECDSA-BA algorithm, in order to achieve a higher security level, let T i = 10 minutes, t = 1000, then after reaching p e =1.36e-21 Under the condition of false alarm rate, the system can work for one week, occupying 12.2kbyte of memory, and the working time is relatively short. When the lifetime t of the sensor network increases, in order to achieve the same error rate, the amount of memory occupied increase, when t=5000, it takes up 61kbyte of memory, which is not suitable for sensor network systems with limited resources, so we improved the ECDSA-BA algorithm and proposed the PECDSA-BA algorithm, using this algorithm The specific steps of the wireless sensor network broadcast authentication method are as follows:
[0102] 1. Divide the lifetime T of the sensor network into t time periods T i (1≤i≤t), each time period T i for several days; then T i Divided into smaller time slice
[0103] 2. Every time period corresponding to generate a key pair The...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More