Protection method for confidential files
A technology for secret files and files, applied in the field of software implementation, can solve problems such as file damage development of complex and transparent encryption software, achieve the effect of strong versatility, reduce the workload of integrated development and testing, and improve reliability
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
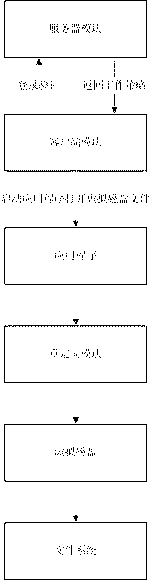
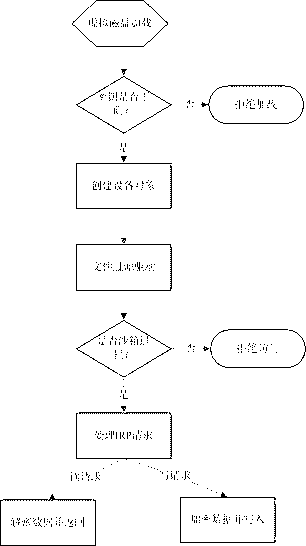
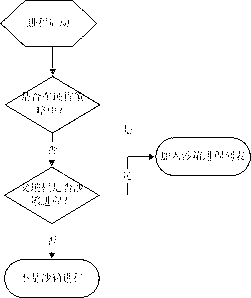
Image
Examples
Embodiment Construction
[0025] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the embodiments described here are only used to explain the present invention, not to limit the present invention.
[0026]1, the system environment of the present embodiment is the Windows2000 of Microsoft and above version operating system; The function that realizes is to be integrated with the file management software of the third party, allows the user to safely operate (as: open, browse, edit) on the client computer ) The secret-related files downloaded from the server, that is, to control the user from taking the files out of the client computer by copying, saving them, etc. during the process of using the downloaded files, so as to ensure the security of the secret-related files.
[0027] 2. The file security soft...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More