Method and system for file protection
A technology for protecting systems and files, applied in the fields of instruments, electrical digital data processing, computer security devices, etc., can solve problems such as hidden dangers and insufficient key protection.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
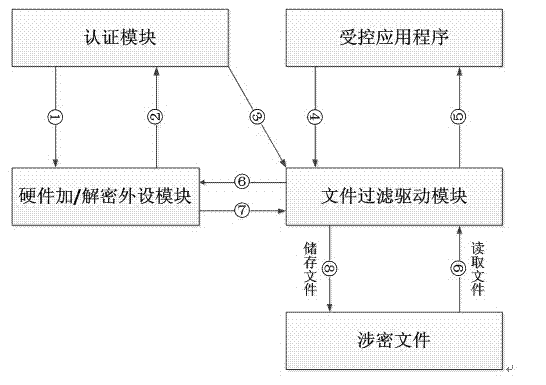
[0016] The present invention will be further described below in conjunction with the accompanying drawings and specific embodiments.
[0017] like figure 1 As shown, in this embodiment, the mechanism of the present invention is described in detail by taking the operation process of a user using an encrypted doc file as an example.
[0018] Step 1: The user starts the authentication module, and the authentication module allows the connected hardware encryption peripherals to perform authentication.
[0019] Step 2: If the encryption module is not connected, then connect the hardware encryption module, and the authentication module requires input of authentication information.
[0020] Step 3: The user enters the authentication information, and the authentication module and the hardware encryption module perform authentication. If the authentication is passed, the driver will be prompted to start successfully, otherwise it will fail.
[0021] Step 4: After passing the authenti...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More