Access control method and access control device of user data
An access control and user data technology, applied in the computer field, can solve problems such as occupying system storage space, affecting the rational use of system resources, and not proposing solutions, and achieves the effect of optimizing resource use and saving storage space
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
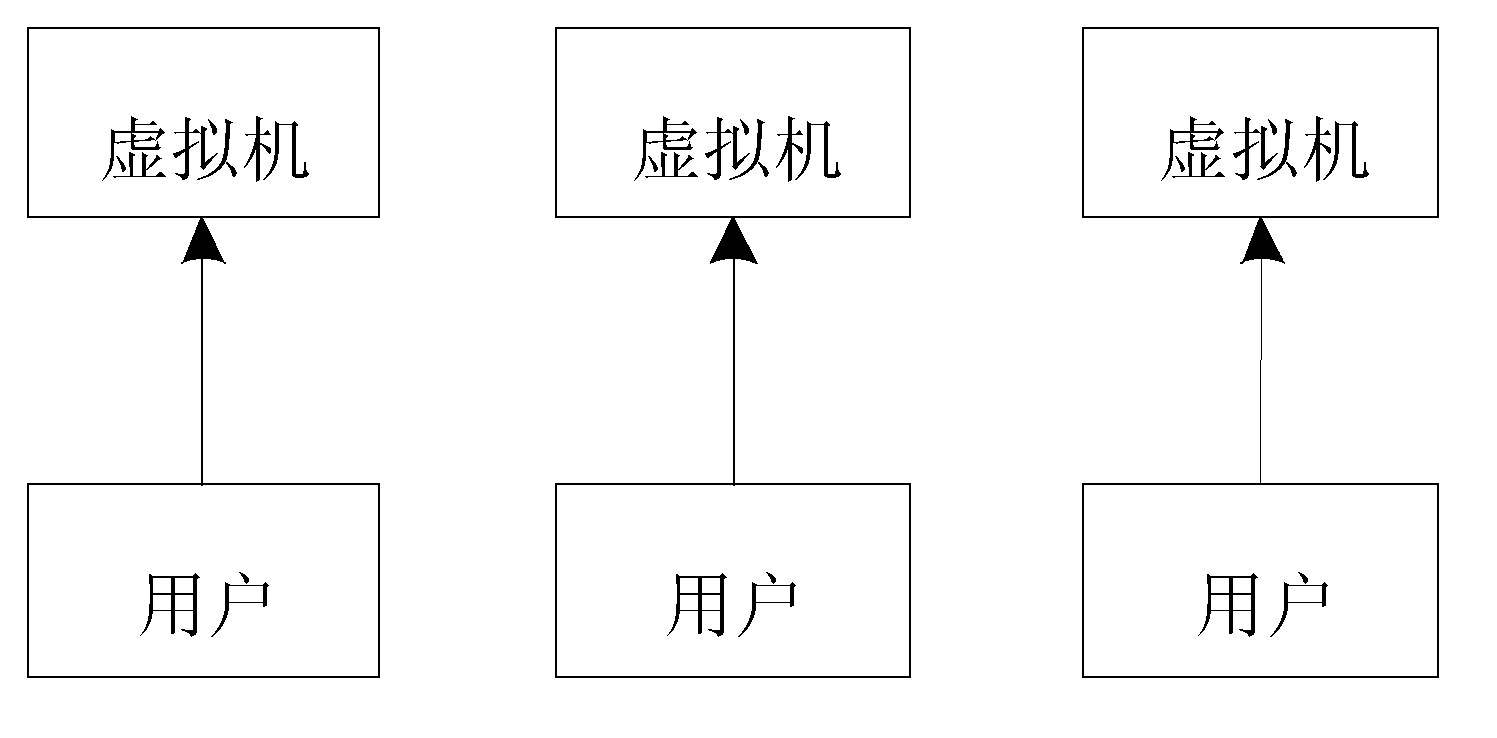
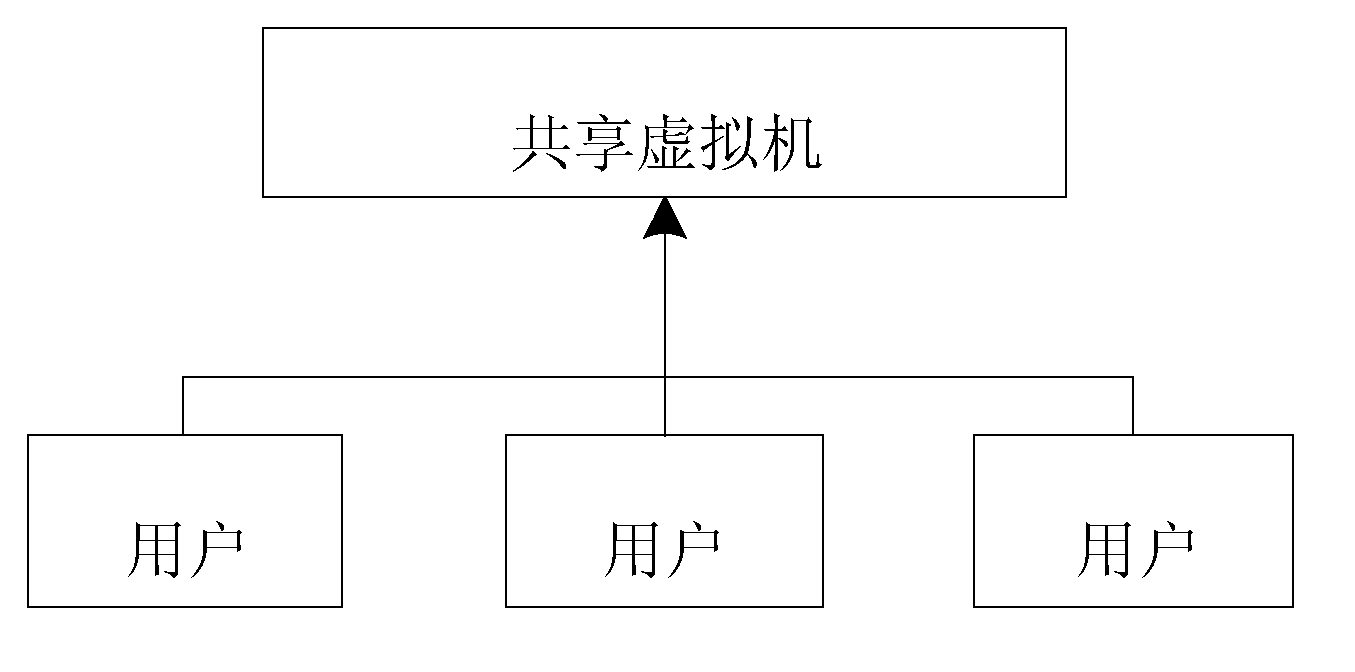
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0042] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. All other embodiments obtained by persons of ordinary skill in the art based on the embodiments of the present invention belong to the protection scope of the present invention.
[0043] According to one aspect of the present invention, a method for access control of user data is provided:
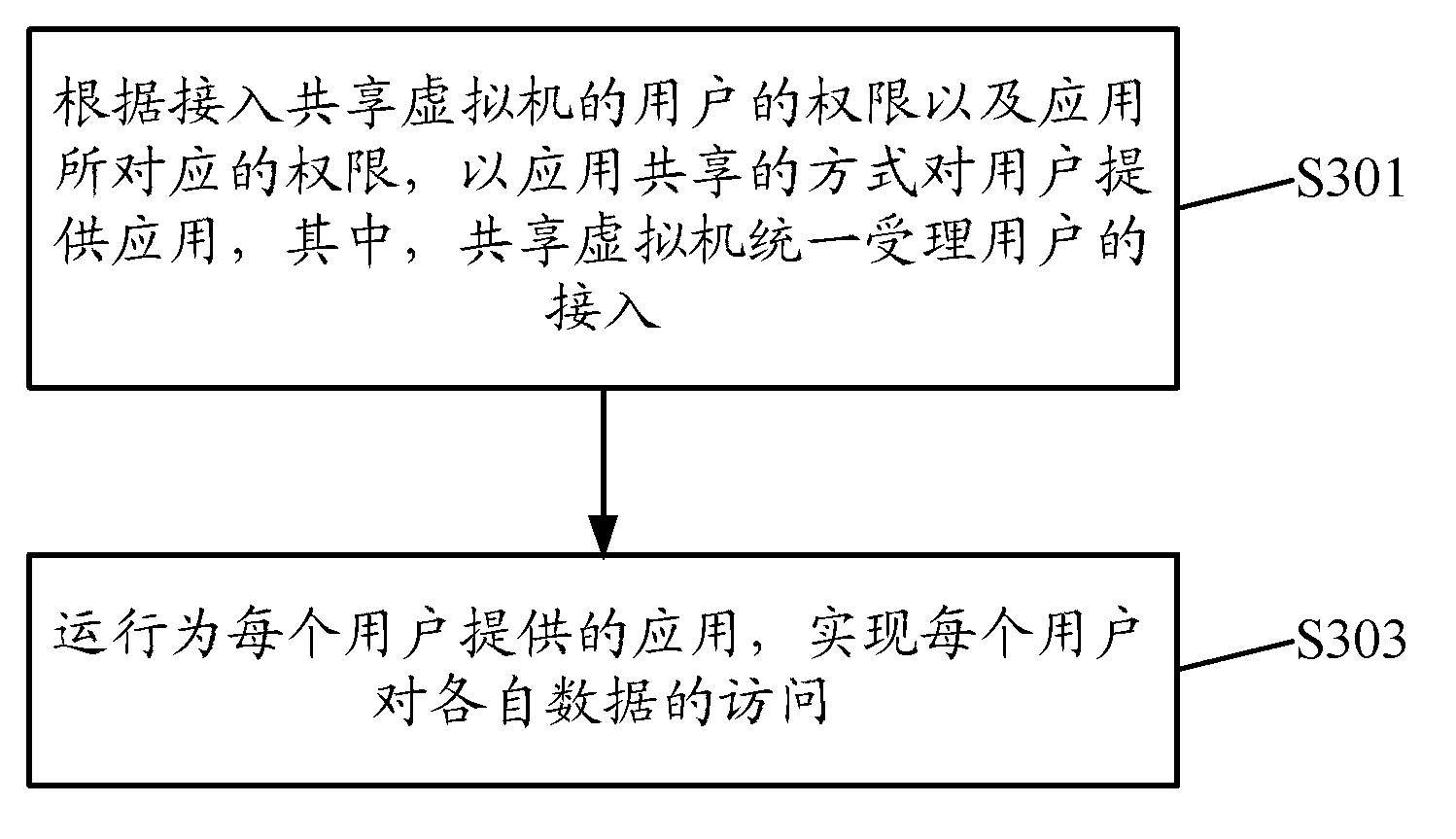
[0044] Such as image 3 As shown, it is characterized in that the access control method includes:
[0045] Step 301, according to the authority of the user accessing the shared virtual machine and the authority corresponding to the application, the application is provided to the user in the form of application sharing, wherein the shared virtual machine uniformly accepts the user'...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More