Proxy method for improving SSL algorithm intensity of browser
A browser and algorithm technology, applied in the field of network security, can solve problems such as changing the way users use, incompatibility with old and new users, etc., to achieve the effect of expanding algorithm support
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
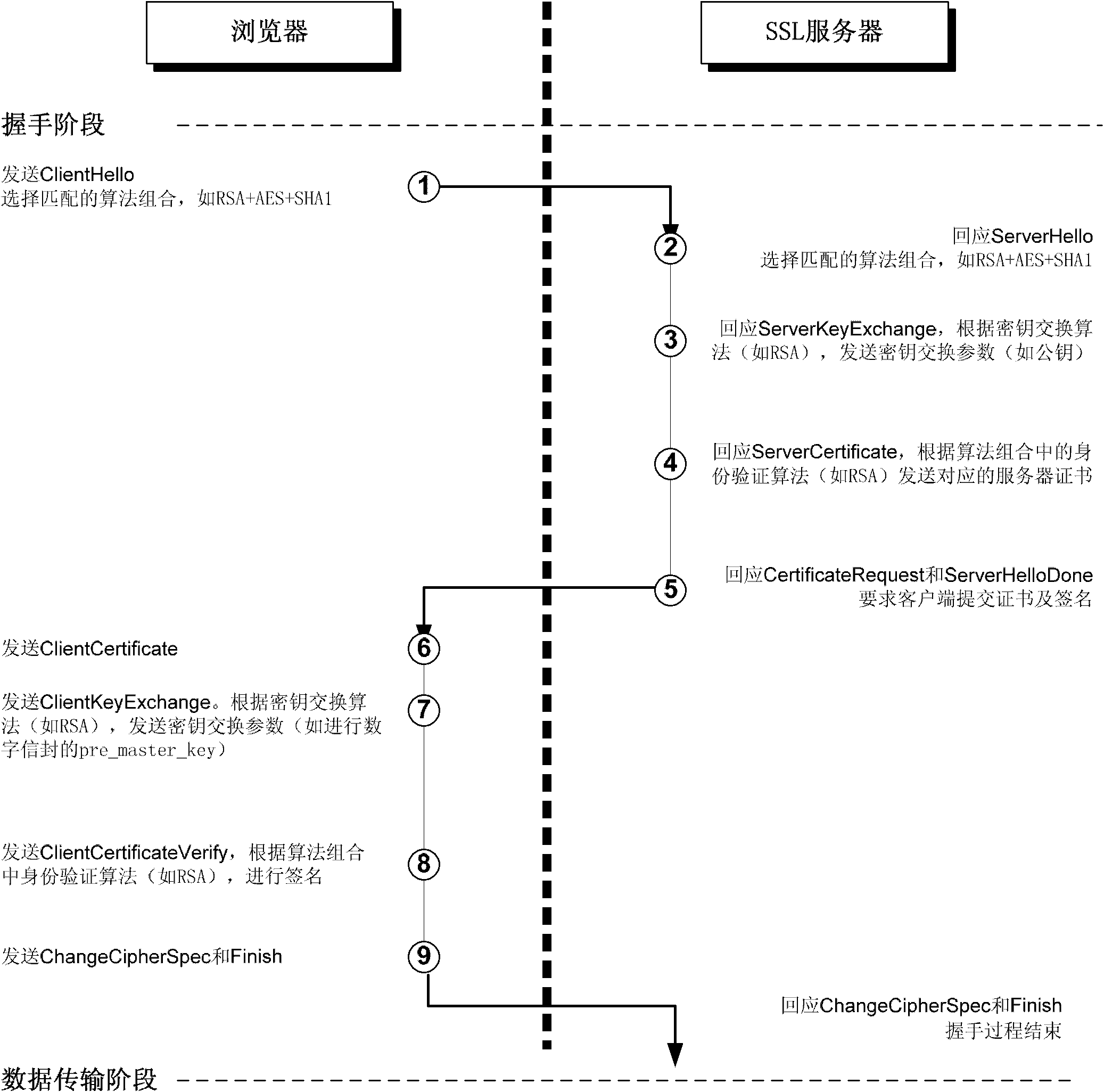
[0032] In order to make the technical means, creative features, goals and effects achieved by the present invention easy to understand, the present invention will be further described below in conjunction with specific illustrations.
[0033] Since the proxy method for HTTPS (that is, SSL) in the HTTP protocol is mainly through the CONNECT method (http: / / tools.ietf.org / html / rfc2616#section-9.9), that is, the proxy server is only responsible for forwarding the browser and TCP packets between target servers without other processing, so when using HTTPS proxy, the actual SSL handshake still occurs between the browser and the server, and the supported algorithms are also determined by the browser.
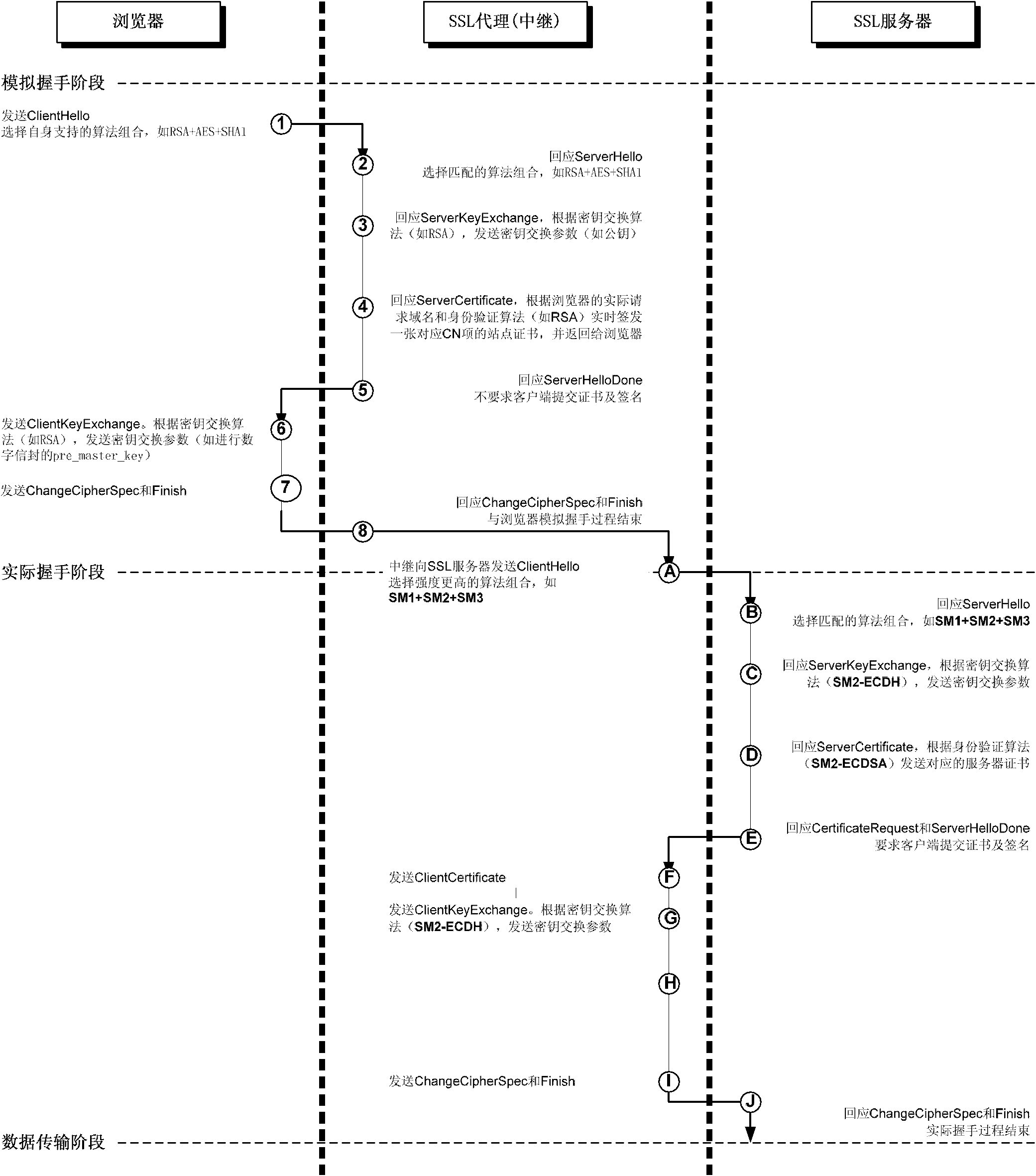
[0034] Based on the principle of above-mentioned HTTPS proxy agreement, the present invention provides a kind of proxy method that strengthens browser SSL algorithm strength, and this method is a kind of HTTPS relay agent, and its main principle is as follows:
[0035] First install a ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More