Two-factor authentication method and two-factor authentication device for wireless sensor network and network comprising two-factor authentication device
A technology of a wireless sensor network and an authentication method, which is applied in the wireless sensor network two-factor authentication method and device and its network field, and can solve problems such as data forgery attacks, inability to guarantee security, gateway counterfeit attacks, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0095] Below in conjunction with accompanying drawing, structural principle and working principle of the present invention are specifically described:
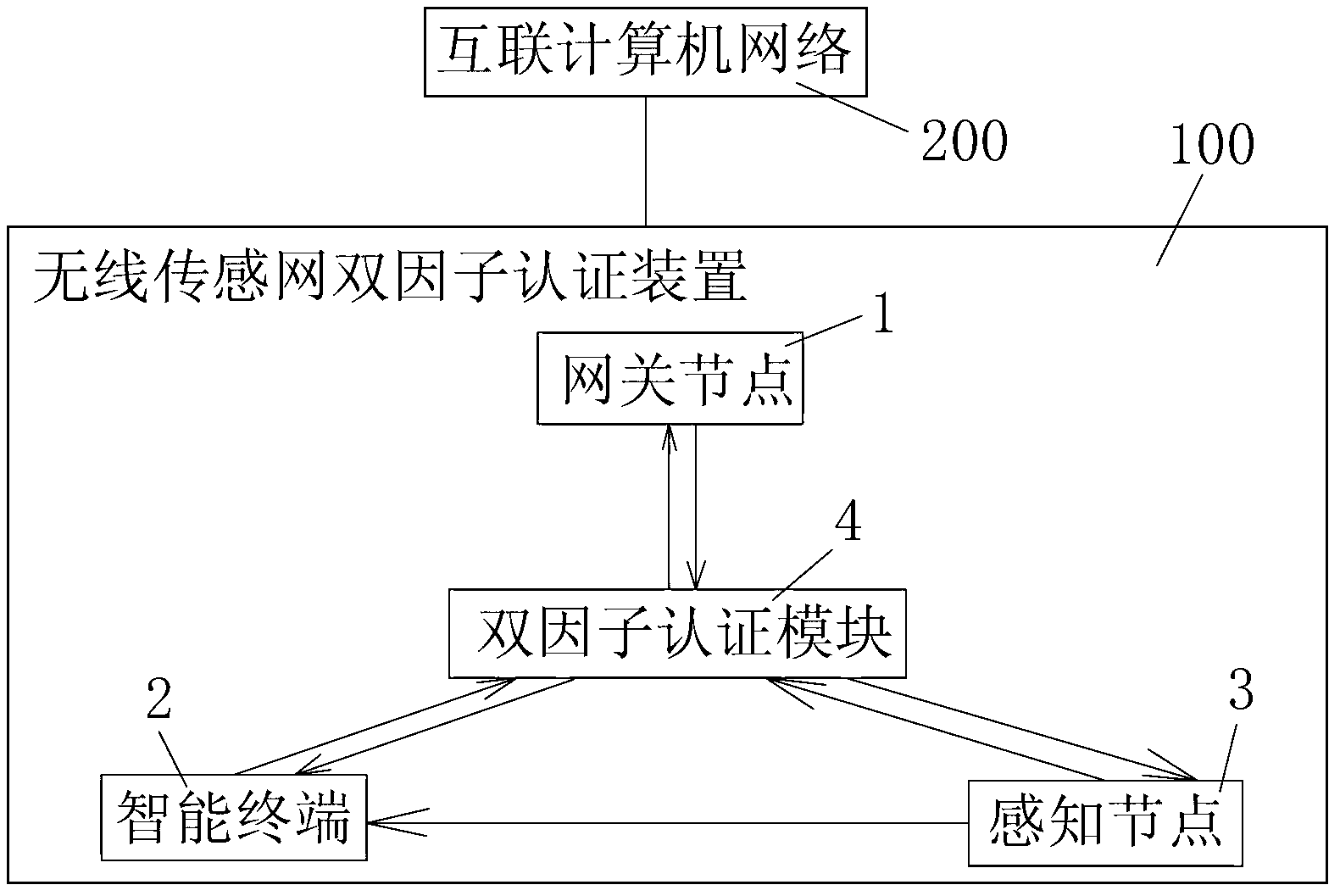
[0096] see figure 1 , figure 1 It is a schematic diagram of the device structure of an embodiment of the present invention. The wireless sensor network two-factor authentication device 100 of the present invention includes a gateway node 1, an intelligent terminal 2, and a sensing node 3. Factor authentication module 4, the two-factor authentication module 4 adopts the following two-factor authentication method for wireless sensor network based on Merkle hash tree. At the same time, the present invention also provides an interconnected computer network 200 having the above-mentioned wireless sensor network two-factor authentication device 100 .
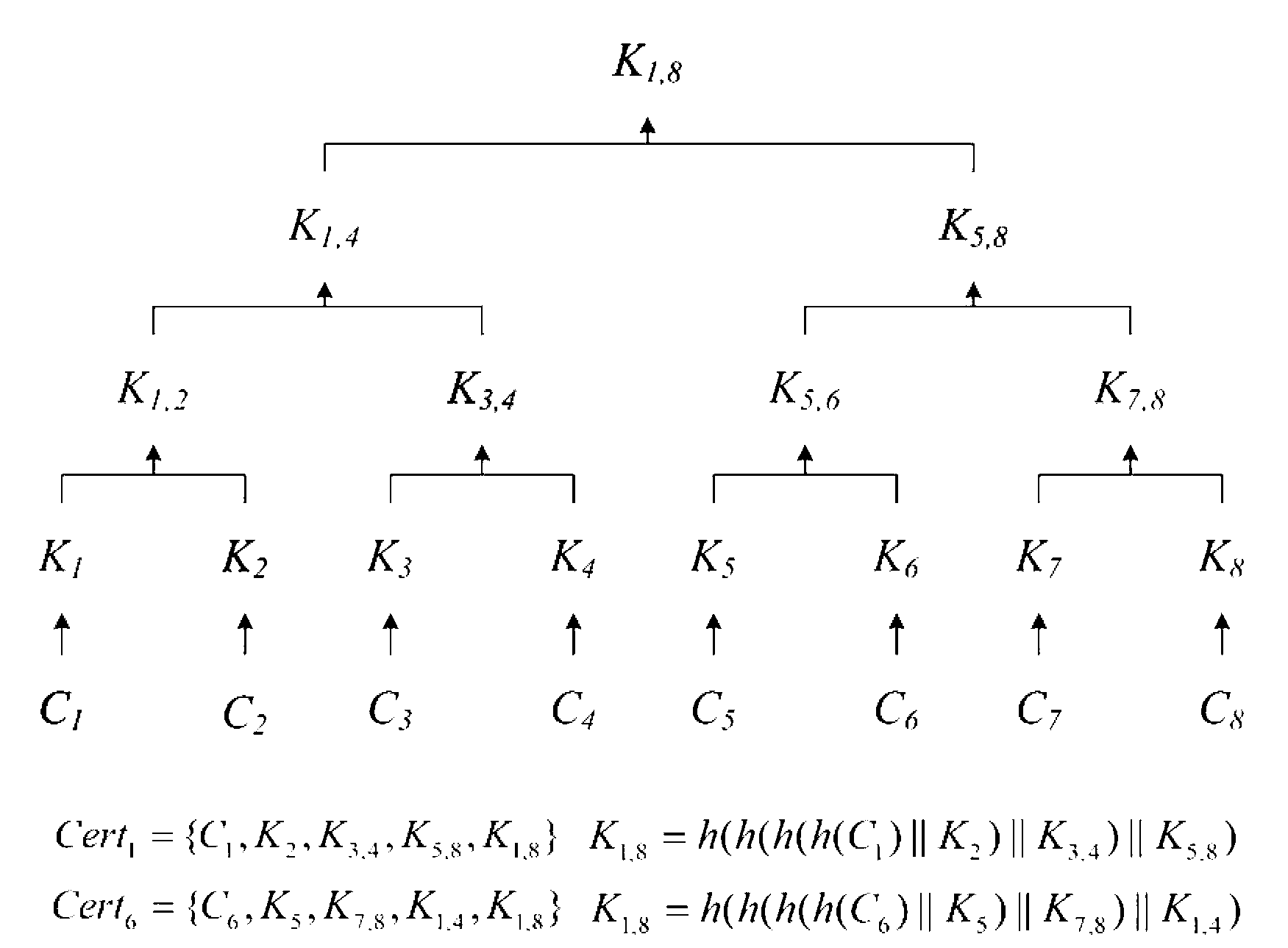
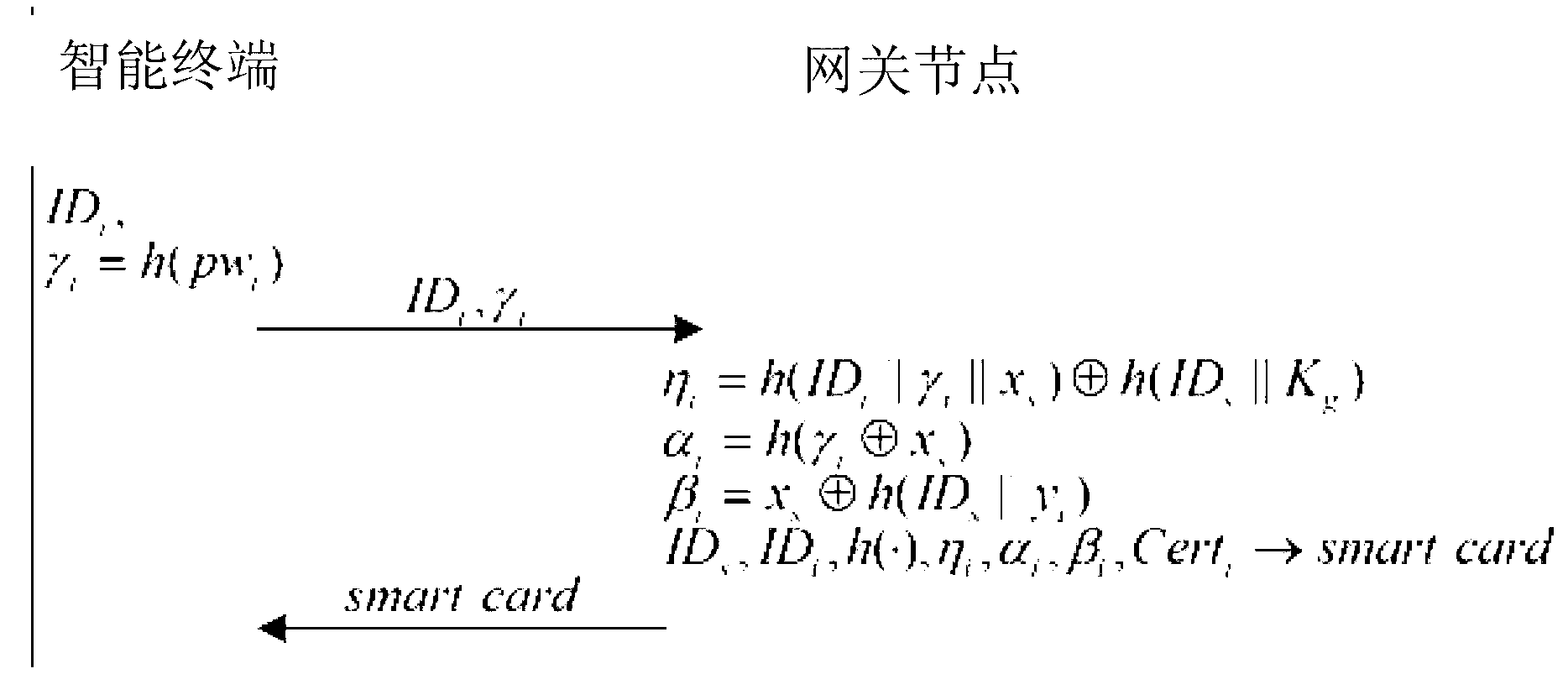
[0097] The wireless sensor network two-factor authentication method of the present invention comprises the following steps:
[0098] Step 100, gateway pre-authentication step, gat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More