Authentication processing method and device
A processing method and authentication request technology, applied in the field of communication, can solve problems such as the inability to realize implicit authentication of a single terminal, and achieve the effect of meeting the flexibility requirements
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0030] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
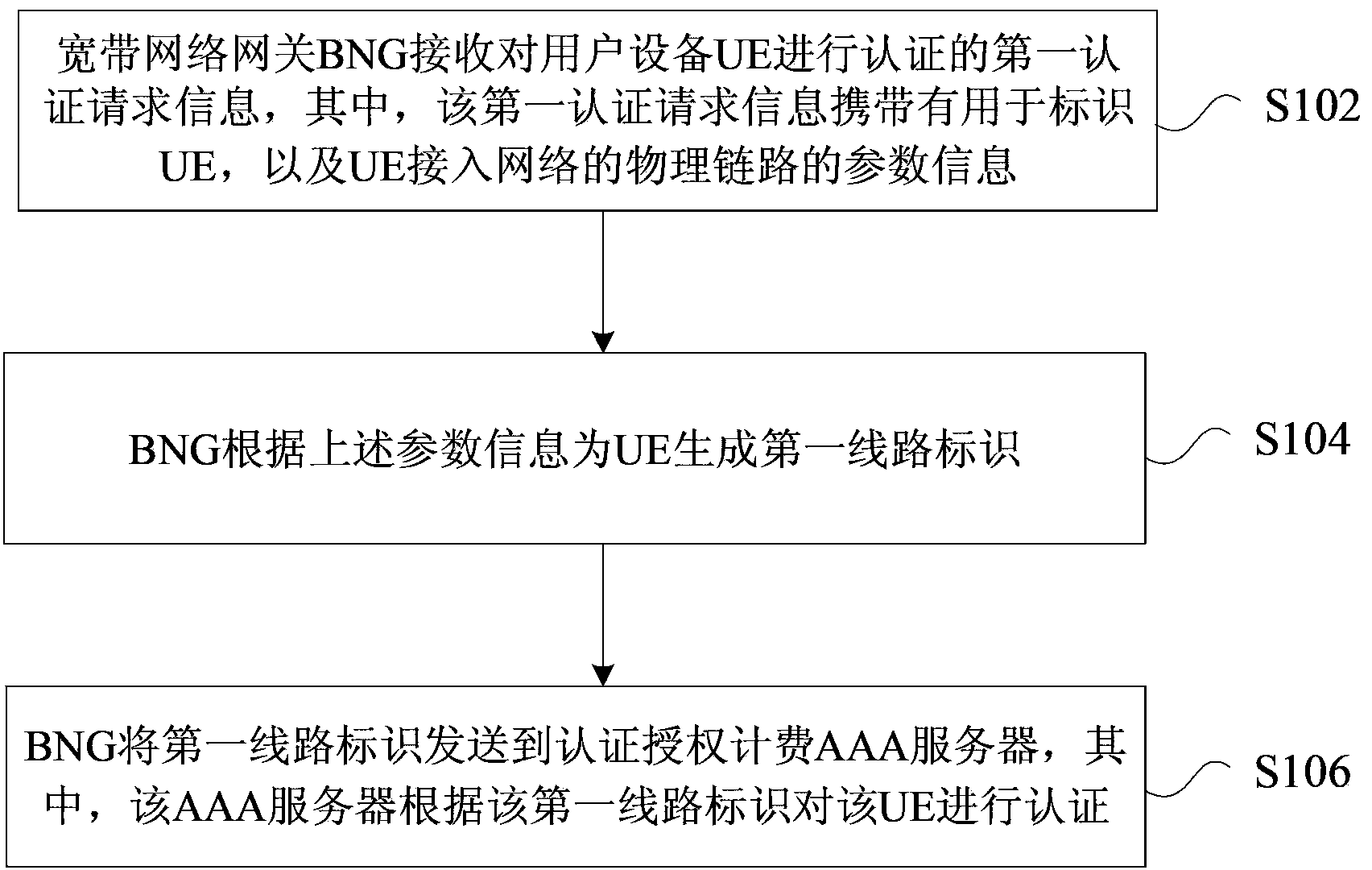
[0031] In this embodiment, an authentication processing method is provided, figure 1 is a flowchart of an authentication processing method according to an embodiment of the present invention, such as figure 1 As shown, the process includes the following steps:
[0032] Step S102, the broadband network gateway BNG receives the first authentication request information for authenticating the user equipment UE, wherein the first authentication request information carries parameter information for identifying the UE and the physical link of the UE accessing the network, wherein, The parameter information identifying the UE may include at least one of the following: the UE's medium access control layer M...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More