Position privacy protection method based on dynamic pseudonyms
A privacy protection and pseudonym technology, applied in location information-based services, security devices, electrical components, etc., can solve the problems of long-term pseudonym and real identity relationship leakage, user real identity and location leakage, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] specific implementation plan
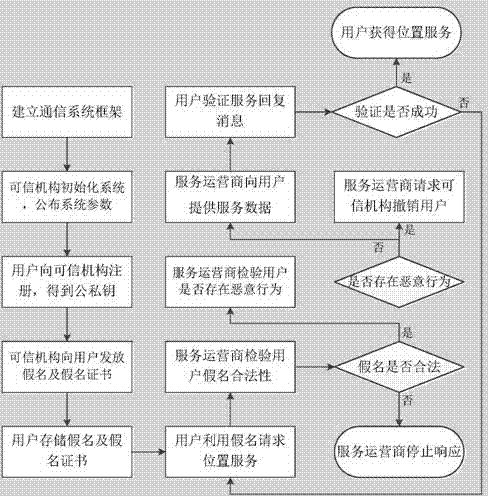
[0038] The core idea of the present invention is to make the user constantly change the identity through the dynamic pseudonym, realize more effective identity anonymity, make the user's spatiotemporal information and identity information cannot be easily linked, and improve the user's privacy; add a pseudonym certificate to the pseudonym to enhance the usability of the pseudonym security, enabling service operators to verify the legitimacy of anonymous users and revoke malicious users.
[0039] refer to figure 1 , the present invention is based on the location privacy protection method of dynamic pseudonym, and its realization steps are as follows:
[0040] Step 1, establish the communication system framework.
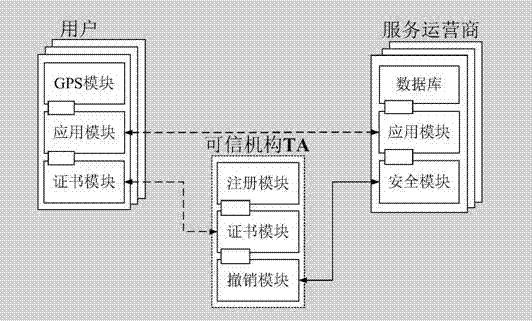
[0041] refer to figure 2 , the communication system established in this step includes: users, trusted organizations TA, and service operators. The trusted organization TA and the service operator have a two-way wired connec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More