Method and system for safety certificate
A technology of security authentication and identity authentication, applied in transmission systems, electrical components, etc., can solve problems such as user information insecurity, achieve the effect of improving technical difficulty, reducing the risk of user information leakage, and increasing technical difficulty
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0058] In order to make the above objects, features and advantages of the present application more obvious and comprehensible, the present application will be further described in detail below in conjunction with the accompanying drawings and specific implementation methods.
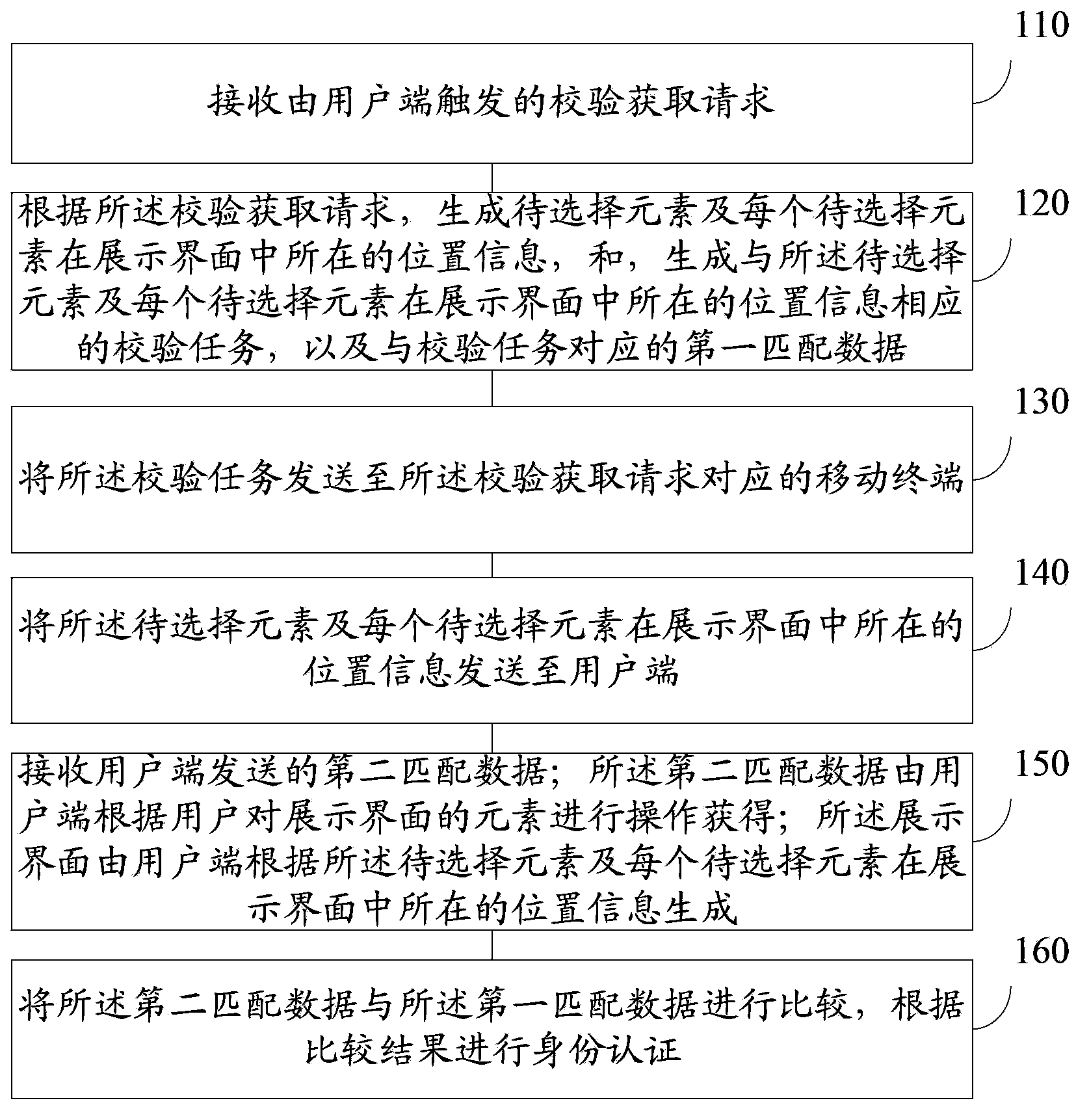
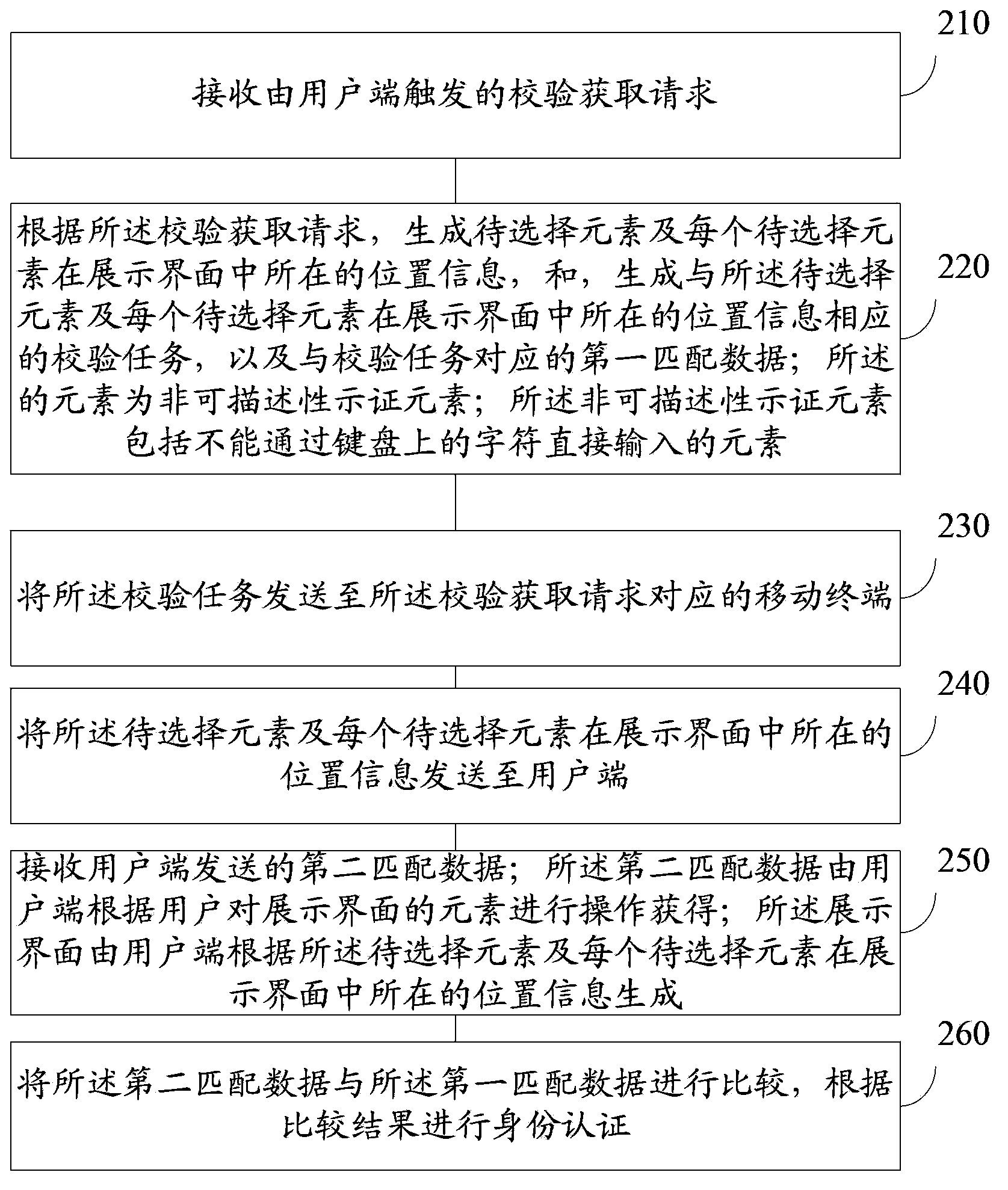
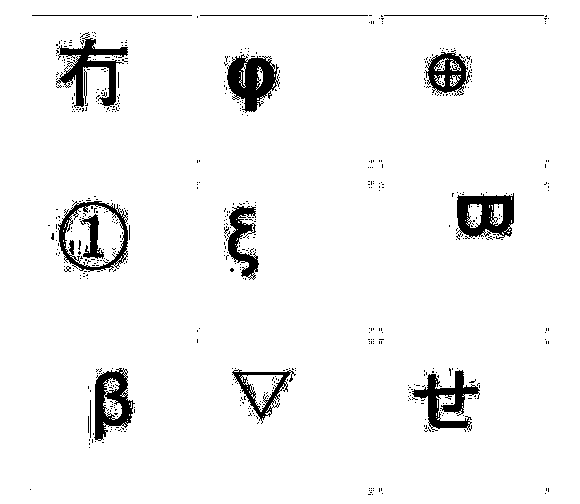
[0059] One of the core ideas of this application is that the verification input page of the target website in the prior art (such as the payment verification page of the payment website) is easy to handle the verification code, which makes it easy to be attacked by phishing websites and seriously endangers user information. In the case of potential safety hazards, this application utilizes a dual-channel format, and the server generates the elements to be selected and the location information of each element to be selected in the display interface according to the verification acquisition request triggered by the client, and generates the same information as the to-be-selected element Select the element a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More