Identification method and device of cheating application program
A technology of application programs and identification methods, applied in the field of network communication, can solve problems such as easy misjudgment and difficult identification of identification schemes, and achieve the effect of accurate identification
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0029] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
[0030] The following embodiments can be applied to computers, such as PCs. It can also be applied to mobile terminals using intelligent operating systems at present, and is not limited thereto. There is no special requirement for the operating system of the computer or mobile terminal, as long as it supports the operation of the plug-in application. For example, the following embodiments can be applied to a Windows operating system.
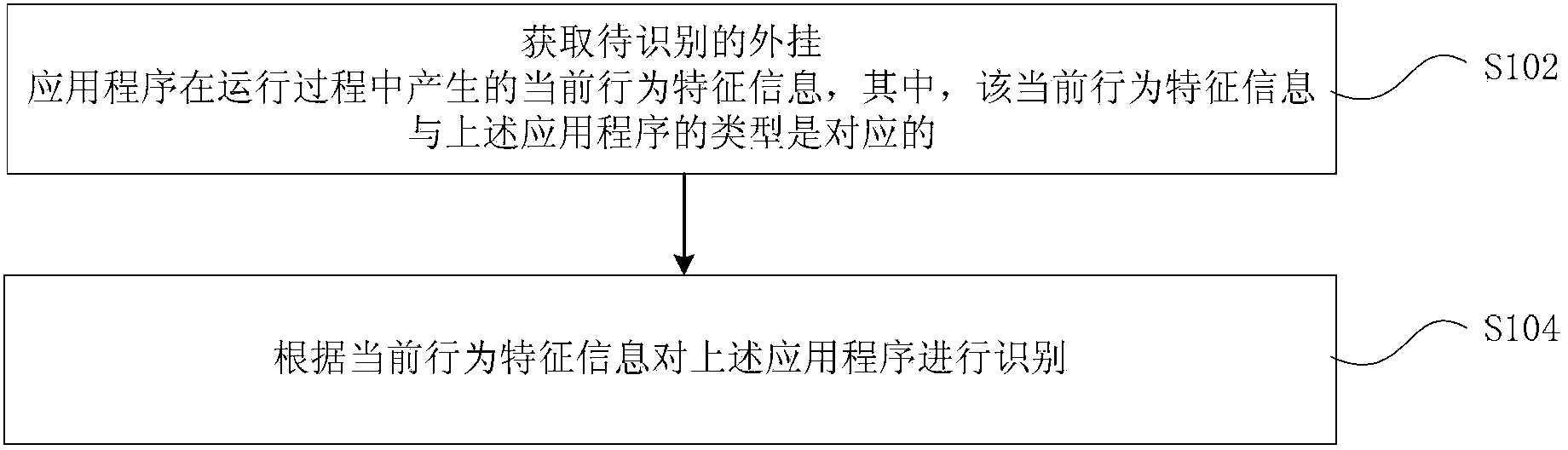
[0031] figure 1 It is a flowchart of a method for identifying plug-in applications according to an embodiment of the present invention. Such as figure 1 As shown, the method includes:
[0032] Step S102, acquiring current behavior feature information generated dur...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More