VoIP steganography method based on optimum similarity matching
A similarity matching and similarity technology, applied in the field of secure communication, can solve the problem of underutilization of secret information and carriers, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0050] The present invention will be further described below through specific embodiments.
[0051] The present invention is applicable to the speech coder of any parametric coding, as ITU-T G.711μ law and A law, ITU-T G.723.1, ITU-T G.729a etc., will use ITU-T G. 711A-law speech coding is taken as an example, and the present invention is further described in conjunction with the accompanying drawings.
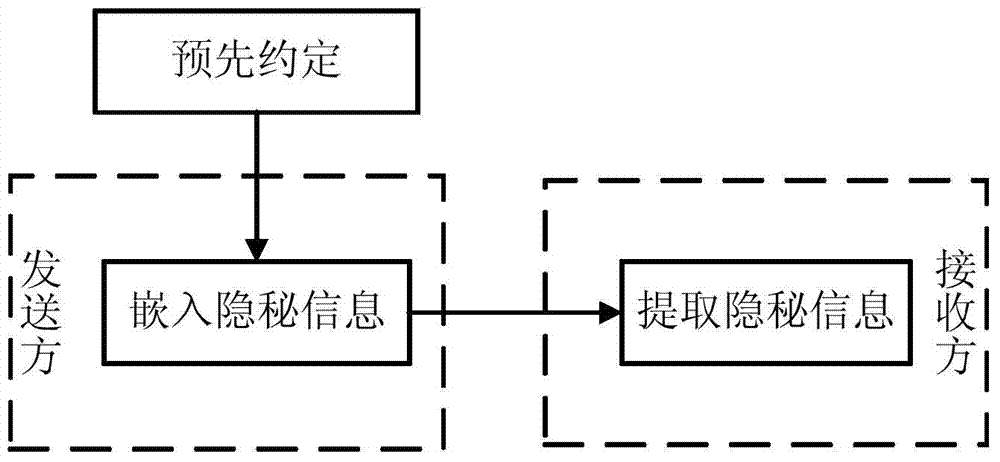
[0052] The processing flow of the present invention is as attached figure 1 As shown, it includes the step of pre-agreement, the step of embedding secret information and the step of extracting secret information.
[0053] 1. Pre-agreement step: the communication parties pre-agreed that the speech coder adopted in the communication process is the ITU-T G.711A law; agree on the carrier and secret information packet length n, such as n=7; agree on the pseudo-random number generation algorithm used.
[0054] There are many kinds of pseudo-random number generation algorithms, and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More