Data encryption method, device, equipment and system and data decryption method, device, equipment and system
A data encryption and data technology, applied in the field of data security, can solve the problem of low security of encryption and decryption methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0114] In order to make the object, technical solution and advantages of the present invention clearer, the implementation manner of the present invention will be further described in detail below in conjunction with the accompanying drawings.
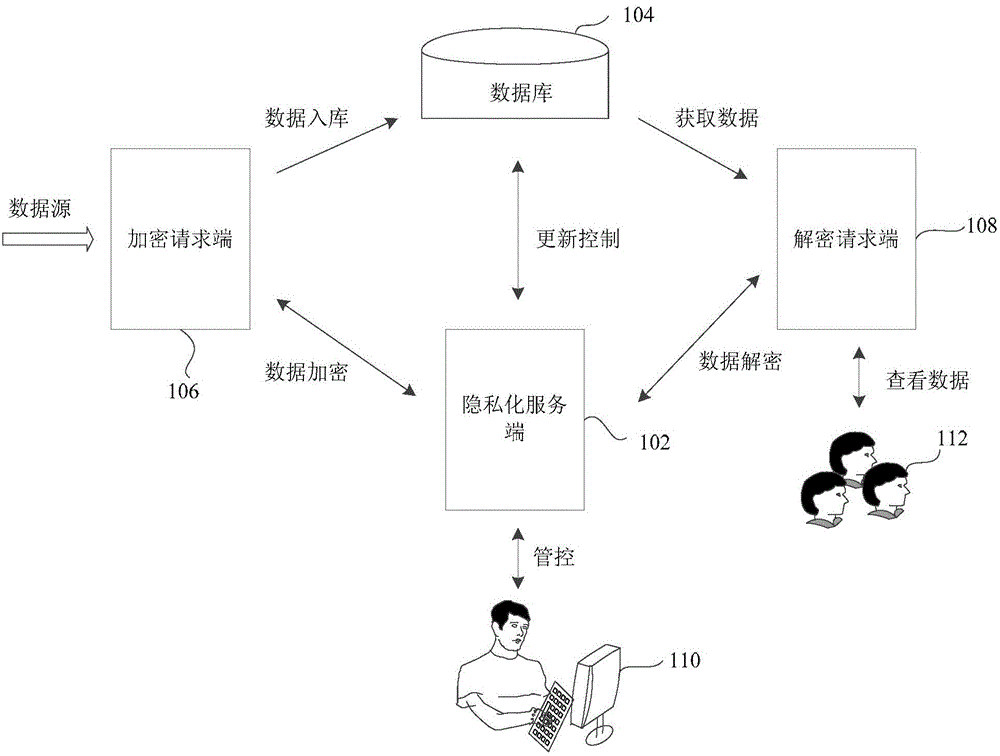
[0115] See figure 1 As shown, it shows a schematic diagram of the implementation environment involved in the data encryption method and the data decryption method provided in some embodiments of the present invention. The implementation environment may include: a privacy service end 102 , a database 104 , an encryption request end 106 and a decryption request end 108 .
[0116] The administrator 110 can manage the content in the privacy server 102, such as setting encryption rules for the data corresponding to the fields in the predetermined form in advance, and the privacy server 102 performs privacy services according to the content set by the administrator 110 In addition, the privacy server 102 is connected to the database 104, an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More