Method for monitoring counterfeit card risk and transaction processing system implementing the method
A transaction processing and transaction technology, applied in the computer field, can solve problems such as failure
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
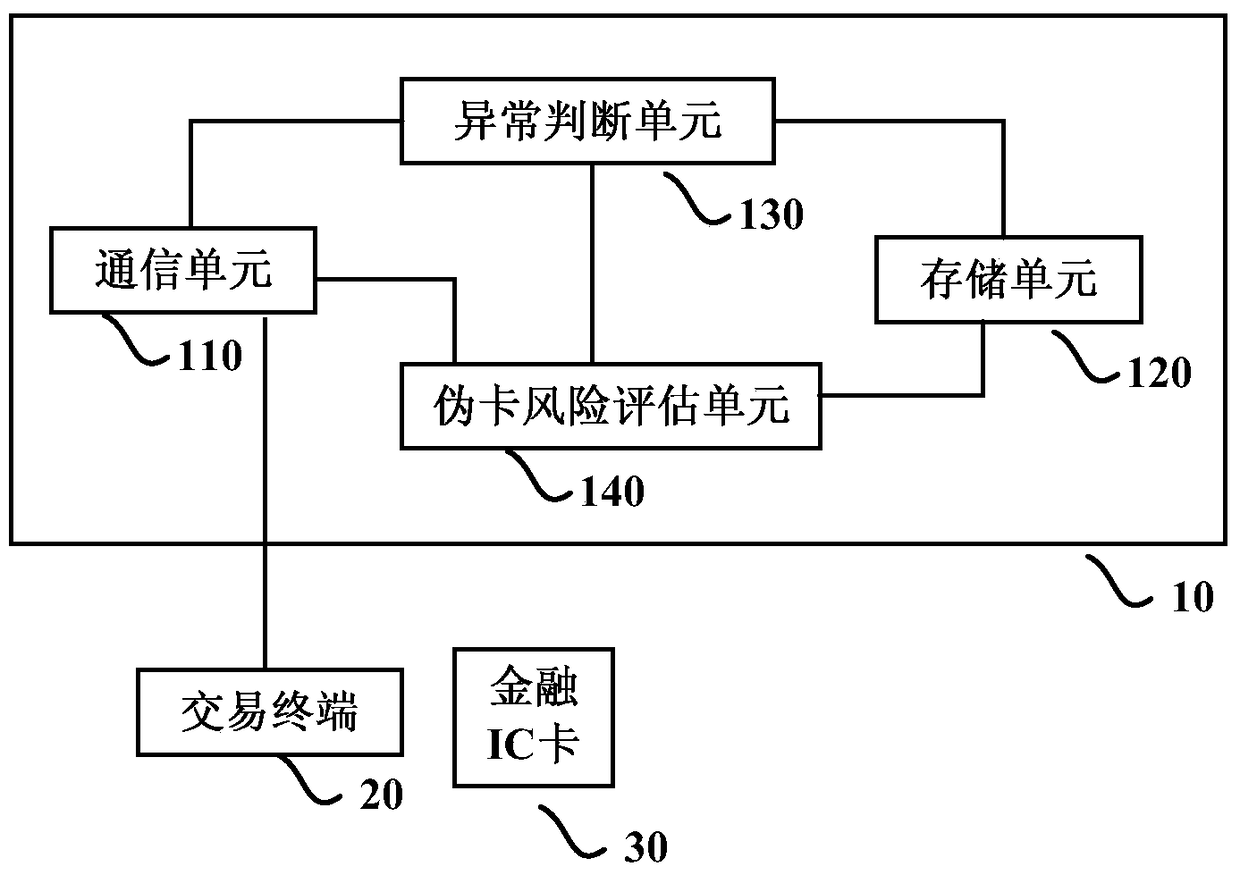
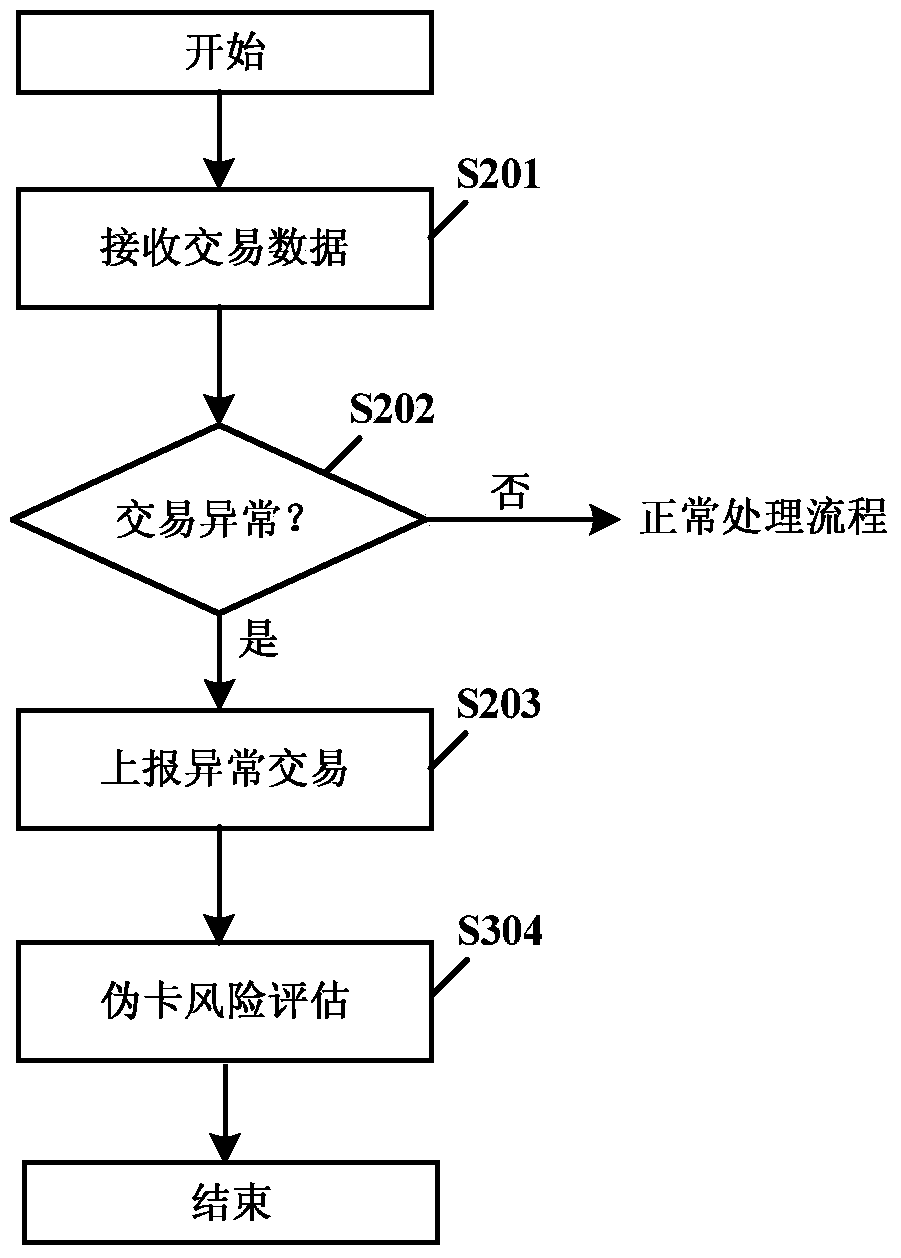
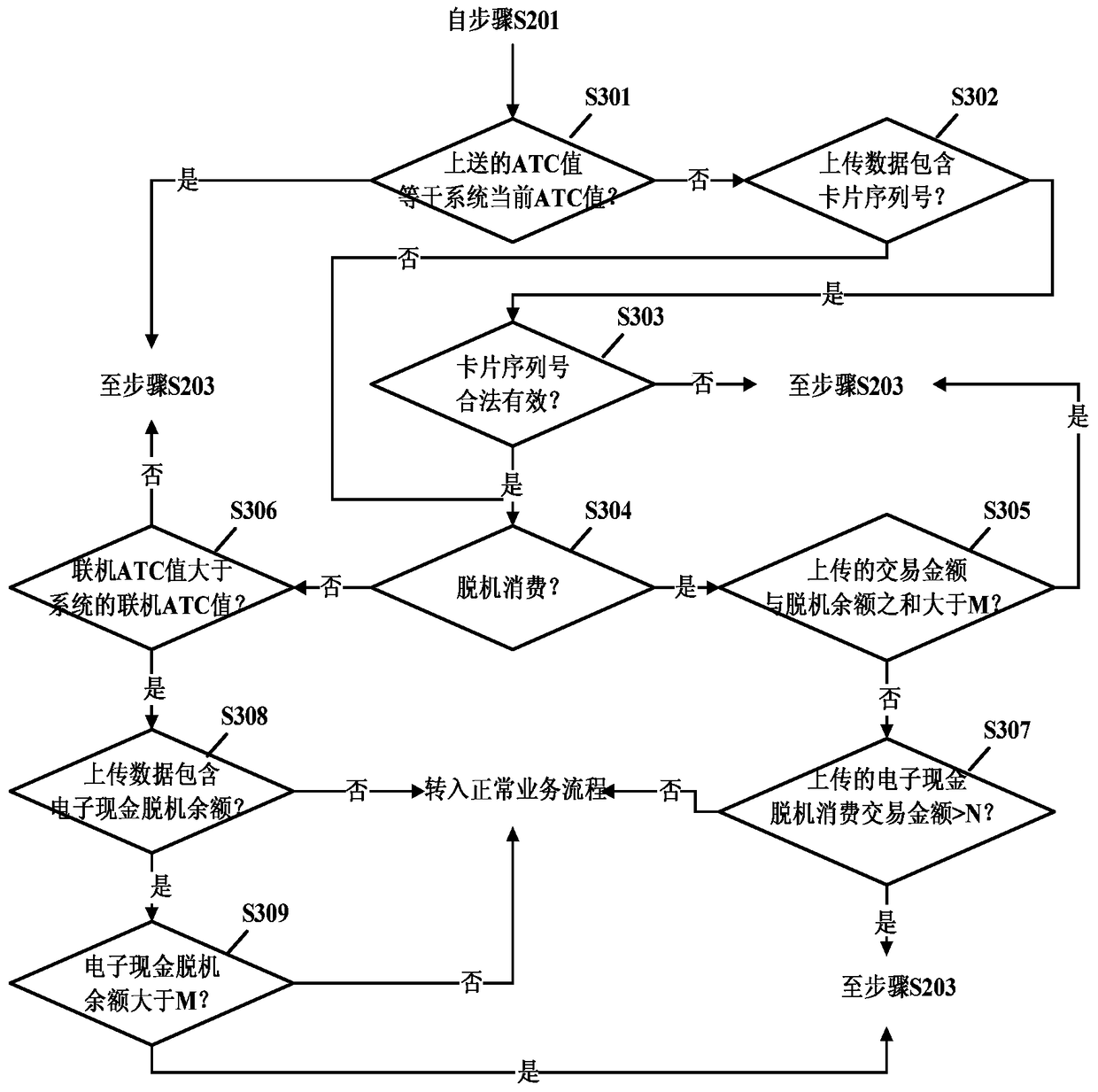
[0032] The present invention will be described more fully hereinafter with reference to the accompanying drawings, in which exemplary embodiments of the invention are shown. This invention may, however, be embodied in different forms and should not be construed as limited to only the embodiments set forth herein. The above-mentioned embodiments are given to make the disclosure of this document comprehensive and complete, so as to make the understanding of the protection scope of the present invention more comprehensive and accurate.
[0033] Words such as "comprising" and "comprising" mean that in addition to the units and steps that are directly and explicitly stated in the specification and claims, the technical solution of the present invention does not exclude other elements that are not directly or explicitly stated. Situation of units and steps.
[0034] Terms such as "first" and "second" do not indicate the order of units in terms of time, space, size, etc., but are on...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More