A client-led client authentication method
A client and authentication technology, applied in location information-based services, electrical components, wireless communications, etc., can solve problems such as poor service quality, slow operation, and increased server load, and reduce performance hits Effects of demand, cost reduction, and flow saving
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
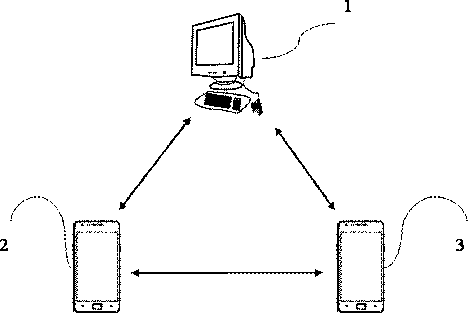
[0033] Embodiment 1 of the present invention provides a client-led client authentication method, which is applied to a server / client architecture network, and is characterized in that it includes:
[0034] Step 202, the server stores in the authentication database the identification serial numbers and geographical locations of the clients that have successfully authenticated;
[0035] Step 204, the first client applying for authentication to the server sends an authentication request to the server, which includes the identification serial number and geographic location of the first client and the identification serial number of the second client;
[0036] Step 206, when the server receives the authentication request, it judges whether it contains an authentication failure message, if not, then enters step 208; if yes, then enters step 222;
[0037] Step 208, the server looks up the identification serial number of the second client in the authentication database; if no matching...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More