Link login method and system
An algorithm and symmetric encryption algorithm technology, applied in the computer field, can solve the problem of high risk of obtaining keys, and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
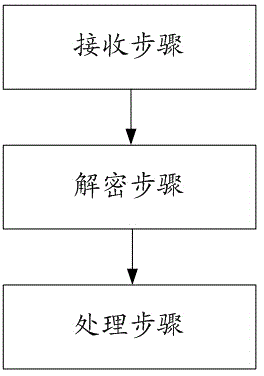
[0048] Such as figure 1 As shown, the present invention discloses a login link method, in which the following preparatory work needs to be done:
[0049] Choose a secure asymmetric encryption algorithm (such as RSA), the following is regarded as using RSA;
[0050] Choose a secure symmetric encryption algorithm (such as AES), the following is regarded as using AES;
[0051] The developer generates a pair of RSA public key and private key. The public key is stored in the mobile game client (hereinafter referred to as the client) and is open to everyone. The private key is stored in the game server (hereinafter referred to as the server), and no third party can obtain it.
[0052] In the login link method of the present invention, the following steps are performed in the server:
[0053]In the receiving step, the server receives the encrypted login message login_message sent by the client;
[0054] In the decryption step, after the server receives the login message login_mess...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More