User identity authentication method for intelligent mobile terminal
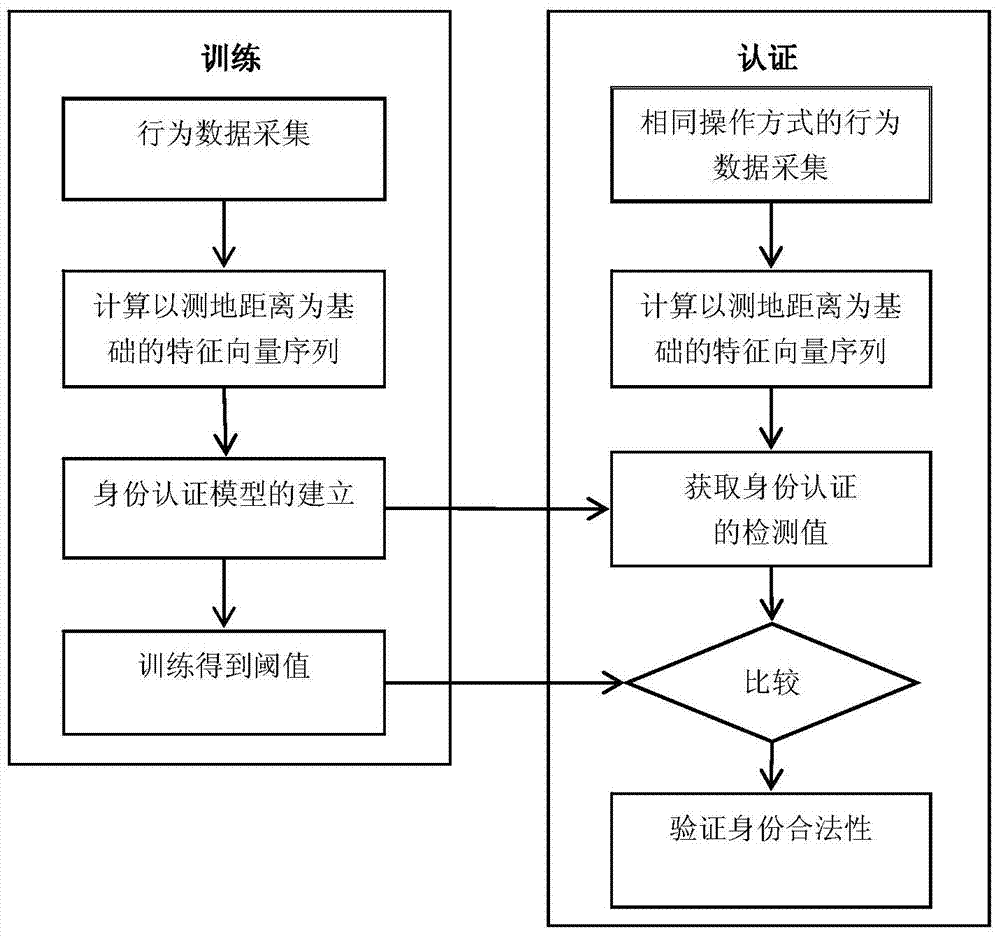
A technology for user identity authentication and smart mobile terminals, applied in digital data authentication, instruments, electrical digital data processing, etc., can solve the problems of not being able to distinguish all users, high cost, and large data noise, and achieve simple and natural operation , high stability, and the effect of improving the ability to distinguish
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0036] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the drawings in the embodiments of the present invention. Obviously, the described embodiments are part of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts shall fall within the protection scope of the present invention.
[0037] 1. Example of operation mode
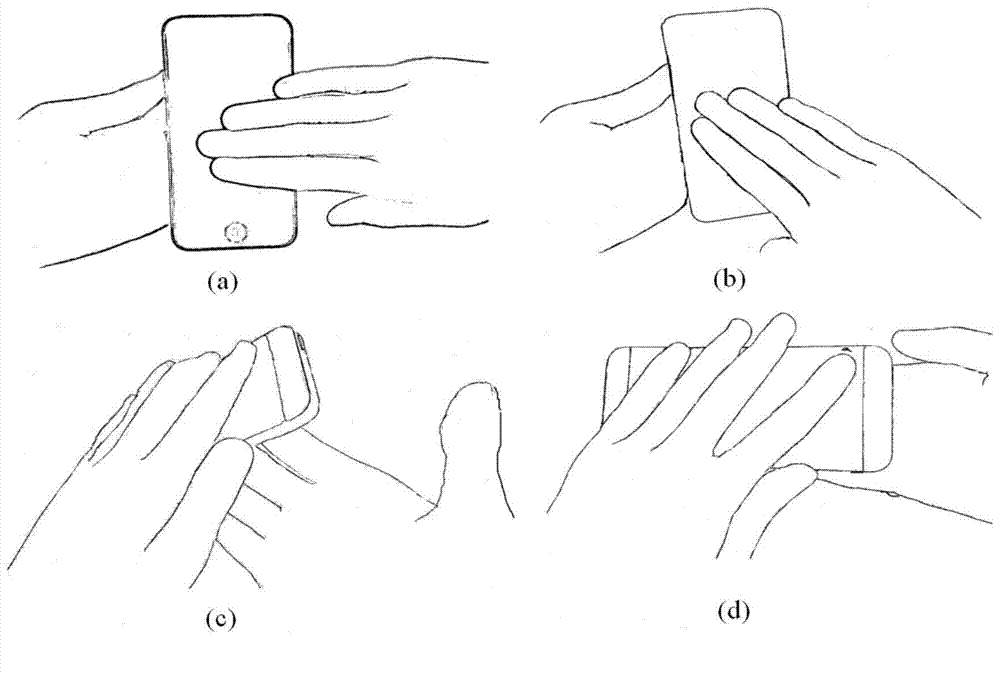
[0038] Two-handed operation (such as figure 1 shown):
[0039] The hand holding the phone drives the mobile terminal to make a 270-degree spatial rotation in a specific mode. While rotating, multiple adjacent fingers of the other hand straighten and close together to rotate and slide on the touch screen. The specific operation is described as follows:
[0040] figure 1 The picture in (a) shows the starting state of ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More